- The Reality of Multi-Framework Compliance in Enterprise Environments
- Where Traditional Compliance Tools Fall Short
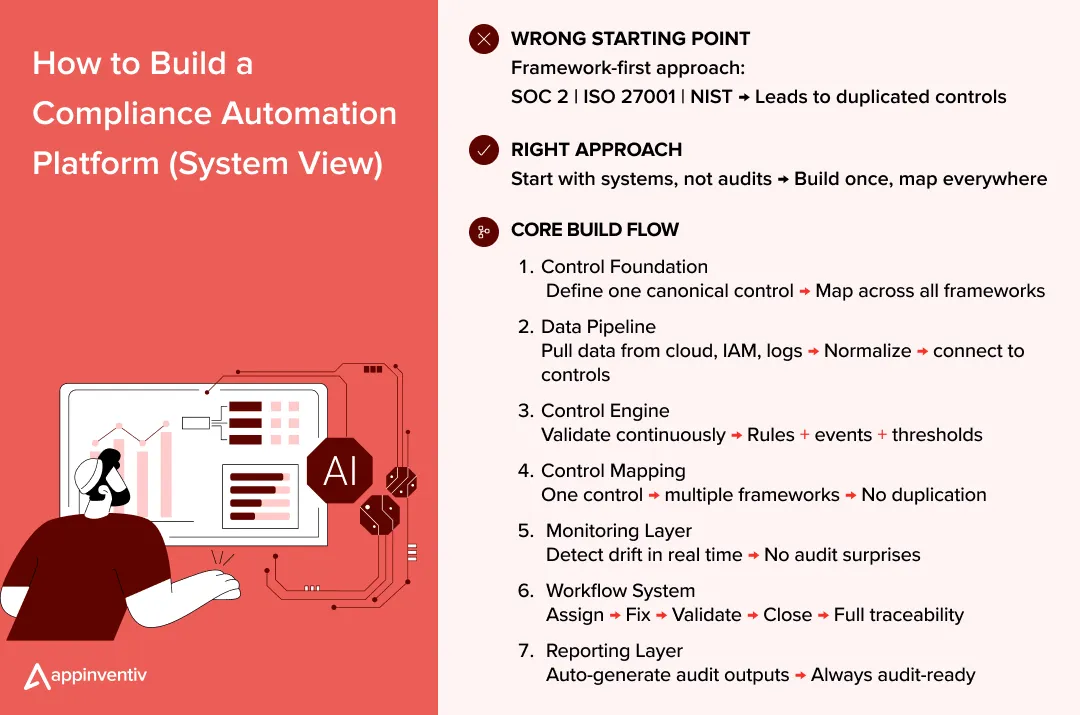
- Step-by-Step guide for compliance automation process
- Control Mapping Across SOC 2, ISO 27001, and NIST (How It Actually Works)
- Key Features of Compliance Automation Platform
- Security and Compliance Considerations While Building the Platform
- Common Mistakes in Compliance Platform Development
- Cost of Building a Compliance Automation Platform
- Build vs Buy: Should You Develop or Use Existing Tools?
- How Appinventiv Builds Compliance Automation Platforms That Scale
- FAQs
Key takeaways:
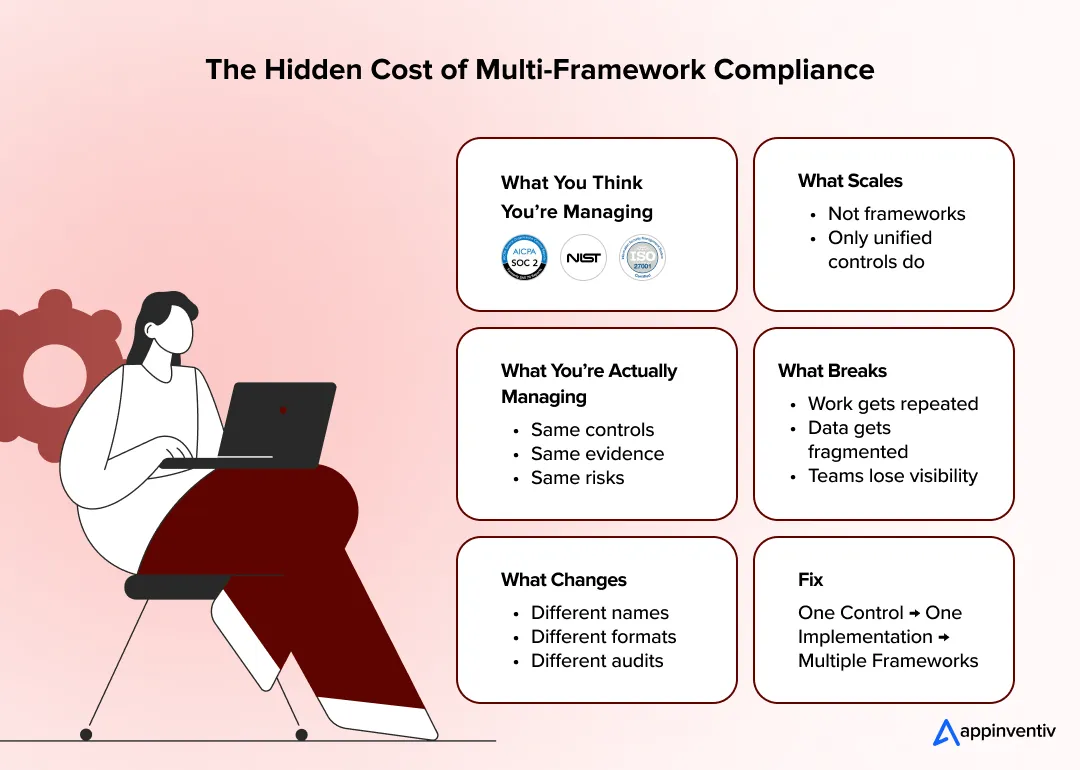
- Multi-framework compliance creates duplication unless controls are unified
- Compliance failures usually come from gaps between systems, not missing controls
- Automation shifts compliance from periodic audits to continuous monitoring
- A well-built platform connects controls, evidence, and workflows in one system
- Cost depends on integration depth and automation, not just features
Most teams don’t fail compliance because they don’t understand frameworks. They fail because things start slipping between systems. One team updates access, another forgets to log it, and suddenly evidence is missing. On paper, everything looks fine. In reality, nothing is fully connected. That gap is where compliance starts breaking.
The numbers make it hard to ignore. According to IBM, the average data breach now costs around $4.44 million globally, and even with better tools, it still takes about 241 days to identify and contain a breach. That’s eight months where something is wrong inside the system and no one has full visibility. The longer it stays unnoticed, the more damage builds quietly in the background.
What’s interesting is not just the cost, but the pattern. Many breaches don’t happen because controls don’t exist. They happen because controls aren’t consistently enforced or monitored. Human error alone still accounts for a significant share of incidents, and things like misconfigurations or missed updates continue to create entry points. In other words, the issue isn’t lack of compliance. It’s a lack of continuity.
This is where most setups fall apart at scale. SOC 2, ISO 27001, and NIST controls start living in different tools, owned by different teams, reviewed at different times. Overlap increases, but alignment doesn’t. If you try to manage that manually, it turns into constant rework.
That’s exactly why companies reach a point where they need to build a compliance automation platform through structured compliance automation software development, not to add another layer, but to finally connect what’s already there.
We help enterprises build compliance automation platforms that connect controls, data, and monitoring into one unified system, turning reactive audits into continuous compliance.
The Reality of Multi-Framework Compliance in Enterprise Environments
At enterprise scale, compliance doesn’t stay contained. It expands across clients, geographies, and regulatory expectations.
- A US-facing product needs SOC 2 for trust assurance.
- A global expansion brings in ISO 27001 for structured ISMS alignment.
- Government or enterprise contracts often introduce NIST for risk and security controls.
None of these replace each other. They layer on top. And over time, teams are no longer managing compliance. They’re managing multiple versions of the same controls, expressed differently.
Where the overlap actually exists
If you break these frameworks down to their core, the overlap is obvious. They are all enforcing the same security and risk fundamentals, just framed differently.
- Access control: Every framework expects strict access governance. That includes least privilege, role-based access, periodic reviews, revocation of unused access and identity and access management especially in healthcare and fintech. The implementation inside systems is identical, but each framework describes it using different control structures and audit expectations.
- Incident response: Whether it’s SOC 2 or NIST, the expectation is the same: detect incidents early, respond in a defined way, and maintain a clear record of actions taken. What changes is how deeply the process is documented and how evidence is presented during audits.
- Data protection: All frameworks require sensitive data to be secured at rest and in transit, with clear ownership and traceability. Encryption standards, access logging, and data handling policies are common across frameworks, even if the control IDs and descriptions differ.
The overlap is not partial. It’s structural. Yet most teams don’t treat it that way.
How fragmentation shows up in real systems
The problem starts when these shared controls are implemented separately for each framework instead of once at the system level.
- Same control, different language: Teams rewrite the same control multiple times to match framework terminology.
Result: duplicated controls with slight wording differences
- Same evidence, different formats: One access review generates logs, approvals, and reports. Each framework demands it in a different format
Result: repeated manual work for the same proof
- Same risk, tracked separately: A single control failure gets logged across multiple frameworks. Each system tracks it independently.
Result: inconsistent severity, duplicated remediation
Why this becomes unsustainable at scale
At a certain point, this approach stops working. Not because compliance requirements increase, but because duplication compounds.
- Effort grows linearly with every new framework added
- Control inconsistencies start appearing across systems
- Audit preparation consumes operational bandwidth
- Teams spend more time maintaining compliance than improving security
The issue is not the frameworks themselves. It’s the lack of a unified system that connects them.
Mature organizations eventually shift their approach. Instead of managing frameworks independently, they treat controls as shared building blocks:
- One control
- One implementation inside systems
- Mapped across multiple frameworks
That shift is what turns compliance from repetitive work into a scalable system. Without it, every new requirement simply adds another layer of duplication.
Where Traditional Compliance Tools Fall Short
Most compliance management softwares were not designed for how modern systems operate. They were built around audits, not around live environments. So even when companies invest in tools, the way compliance is managed doesn’t fundamentally change.
At a surface level, these tools look structured. They provide templates, dashboards, and control libraries. But underneath, they still rely on the same manual inputs and disconnected workflows that teams were already struggling with.
| Area | Traditional Approach | What Actually Happens in Practice | Why It Breaks at Scale |
|---|---|---|---|
| Compliance Model | Checklist-driven workflows | Teams update control status manually and periodically | Cannot keep up with dynamic systems and continuous changes |
| Control Execution | Documented controls | Policies exist, but enforcement varies across systems | No guarantee that controls are consistently applied |
| Monitoring | Periodic reviews | Issues are identified during audits or after incidents | No real-time visibility into control failures |
| Control Mapping | Frameworks handled separately | Same controls duplicated across SOC 2, ISO 27001, and NIST | Leads to redundant work and inconsistent control definitions |
| Evidence Collection | Manual uploads or partial integrations | Evidence recreated in different formats for each audit | Increases effort without improving accuracy |
| Audit Traceability | Scattered logs and reports | Hard to track how a control performed over time | Weak audit trails and difficult validations |
| Workflows | Tool-based task tracking | Teams rely on emails, spreadsheets, and manual coordination | No unified workflow or ownership clarity |
| Source of Truth | Multiple dashboards | Data spread across tools, systems, and teams | No single, reliable compliance view |
What this means in reality
Even after investing in tools, teams still operate in fragments. Controls are documented but not continuously enforced. Evidence exists but isn’t consistently reusable. Risk is tracked, but not in a unified way.
That’s why most organizations don’t eliminate manual work. They just shift where it happens.
The underlying gap
Traditional tools improve visibility, not execution.
They help you see compliance. They don’t ensure compliance is actually happening inside systems.
And that’s the point where teams realize they don’t just need better tools. They need a system built around control mapping, automation, and real-time monitoring.
What a Unified Compliance Automation Platform Actually Means
A unified compliance platform is not another dashboard layered on top of existing tools. It’s a system that sits closer to how your infrastructure, access controls, and workflows actually operate, forming a unified compliance management system.
Instead of treating SOC 2, ISO 27001, and NIST as separate programs, it treats them as different views of the same control environment. This is where modern compliance automation solutions go beyond basic tools.
The shift is simple in theory, but hard in execution.
What the platform actually does
At its core, a unified system connects controls, systems, and evidence in a single loop:
- Maps controls across frameworks
Controls are not recreated for each framework. They are defined once and mapped across multiple standards. Access control, incident response, and cloud data protection exist as shared controls, not duplicated entries. - Automates evidence collection directly from systems
Instead of uploading screenshots or reports, the platform pulls data from source systems such as cloud environments, identity providers, and logging tools. Evidence is generated as a byproduct of system activity, not manual effort. - Continuously monitors compliance posture
Controls are not checked quarterly or during audits. They are evaluated continuously. If access policies drift, configurations change, or logs indicate anomalies, the system flags it immediately. - Maintains an audit-ready state at all times
Audit preparation is no longer a separate phase. Since controls, evidence, and logs are already connected, the system can produce audit-ready outputs without manual reconciliation.
What changes compared to traditional setups
The biggest difference is where compliance lives.
- It moves from documents to systems
- From periodic reviews to continuous validation
- From isolated frameworks to unified control logic
Instead of asking, “Are we compliant for this audit?”
The question becomes, “Are our systems behaving in a compliant way right now?”
The core principle behind unification
Everything comes down to one idea:
- One control
- One implementation inside systems
- Mapped across multiple frameworks
This removes duplication at the root. Teams no longer maintain separate controls for each framework or recreate evidence for each audit. The same control execution satisfies multiple requirements.
Why this matters at scale
Without this structure, every new framework adds more work. With it, new frameworks mostly add mappings, not effort.
That’s the difference between compliance that grows linearly with requirements and compliance that scales with the system.
Step-by-Step guide for compliance automation process
Most teams start with frameworks. That’s usually the wrong starting point.
If you begin with regulatory compliance in financial software like SOC 2, ISO 27001, or NIST as separate tracks, you’ll end up recreating the same controls multiple times. The build has to start from the system layer, not the audit layer, especially when designing for regulatory compliance automation at scale.
This is what compliance automation tools development actually looks like in practice when you build it right.
Step 1: Define a Unified Control Model (Foundation Layer)
Before writing any code, you need a normalized control structure.
- Break frameworks into atomic controls
- Identify overlaps across frameworks
- Create a canonical control library
Each control should include:
- Control ID (internal, not framework-specific)
- Control logic (what needs to be enforced)
- Validation method (how it is checked in systems)
- Evidence sources (where proof comes from)
- Framework mappings (SOC 2, ISO, NIST references)
Example: Access control is not three controls. It’s one control mapped across frameworks.
This step decides whether your platform scales or collapses under duplication.
Step 2: Design the Compliance Data Pipeline
Compliance systems fail when they rely on manual input. You need a pipeline that continuously pulls data from source systems.
Core integrations:
- Cloud providers: AWS CloudTrail, Azure Monitor, GCP Logging
- Identity systems: Okta, Azure AD, IAM roles
- DevOps pipelines: CI/CD logs, deployment configs
- Security tools: SIEM, EDR, vulnerability scanners
What the pipeline does:
- Ingests logs, configurations, and access data
- Normalizes data into structured formats
- Maps incoming data to control validation logic
At this stage, you are not collecting “evidence.”
You are building a system that generates evidence automatically, which is the foundation of compliance process automation.
Also Read: Top 12 FinTech Compliance Pitfalls & How to Avoid Them
Step 3: Build the Control Evaluation Engine
This is where compliance becomes real.
Each control needs to be translated into executable logic:
- Rule-based validation (e.g., MFA enabled for all users)
- Threshold checks (e.g., inactive users > 90 days)
- Event-based triggers (e.g., privilege escalation detected)
The engine continuously evaluates:
- Current system state
- Historical patterns
- Deviations from expected control behavior
Output:
- Pass / Fail status
- Risk severity
- Timestamped validation logs
This replaces periodic audits with continuous validation.
Step 4: Implement Control Mapping Across Frameworks
Once controls are validated, they need to map back to frameworks.
This is where most tools oversimplify.
You need:
- One-to-many mapping logic
- Versioning for framework updates
- Custom overlays for client-specific requirements
This is critical when building a SOC 2 compliance automation platform, enabling ISO 27001 compliance automation and aligning with a NIST compliance automation platform approach.
Example: A single access control validation can map to:
- SOC 2 CC6.x
- ISO 27001 A.9
- NIST AC family
The system should automatically reflect compliance status across all mapped frameworks.
Step 5: Build Real-Time Monitoring and Drift Detection
Compliance is not static. Systems drift.
- New users get added
- Permissions change
- Configurations update
- Services get deployed
Your platform must detect:
- Control violations in real time
- Configuration drift
- Unauthorized changes
This requires:
- Event streaming (Kafka / PubSub) or scheduled polling
- Alerting mechanisms tied to control failures
- Threshold-based anomaly detection
Without this layer, compliance remains reactive.
Step 6: Design Workflow and Remediation Systems
Detection alone is not enough. You need action.
The platform should:
- Assign control ownership
- Trigger remediation workflows
- Track resolution timelines
- Maintain complete audit logs
This typically integrates with:
- Ticketing systems (Jira, ServiceNow)
- Internal approval workflows
- Notification systems (Slack, email)
Every control failure should move through a defined lifecycle:
Detection → Assignment → Fix → Validation → Closure
Step 7: Build the Audit and Reporting Layer
This is where everything comes together.
Instead of preparing for audits manually, the system should:
- Generate framework-specific reports
- Provide real-time compliance dashboards
- Maintain historical audit trails
- Export evidence in audit-ready formats
This is where automated compliance reporting software becomes essential, reducing manual reporting effort significantly.
Outputs include:
- SOC 2 audit reports
- ISO 27001 documentation sets
- NIST control alignment views
The key difference: Reports are generated from live system data, not assembled manually.
What most teams get wrong
When teams try to build a regulatory compliance software for financial services that automate the compliance management, they often:
- Start with UI instead of control logic
- Treat integrations as add-ons instead of core architecture
- Skip normalization and duplicate controls
- Focus on reporting before validation
This leads to tools that look complete but don’t reduce actual compliance effort.
What a well-built system achieves
When done right, the platform becomes part of your infrastructure:
- Controls are enforced, not just documented
- Evidence is generated continuously
- Compliance status is always current
- Audits become validation, not preparation
That’s the difference between building a tool and building a system.
And that’s what it actually takes to build a compliance automation platform that works at enterprise scale.
If you’re thinking about setting this up, it’s much easier to get the foundation right from the start than fix it later.
Control Mapping Across SOC 2, ISO 27001, and NIST (How It Actually Works)
This is where most compliance platforms either become powerful or completely fall apart.
Everyone claims “multi-framework support.” Very few systems actually implement true control mapping. What they usually do is store separate control sets and loosely link them. That doesn’t reduce effort. It just hides duplication.
Real control mapping is not about linking documents. It’s about normalizing how controls behave at the system level.
Start with a canonical control, not a framework
The mistake most teams make is starting from frameworks.
- SOC 2 says one thing
- ISO 27001 defines it differently
- NIST structures it another way
If you follow that path, you end up creating three versions of the same control.
Instead, define a canonical control first.
Example: Access Control
Instead of:
- SOC 2 CC6.x control
- ISO 27001 A.9 control
- NIST AC family control
You define one internal control: “All user access must follow least privilege and be reviewed periodically”
This becomes your source control, independent of frameworks.
Map one control to multiple frameworks
Once the canonical control is defined, you map it outward.
That same access control can align to:
- SOC 2 CC6.x
- ISO 27001 Annex A.9
- NIST AC controls
This creates a one-to-many relationship:
- One implementation
- Multiple compliance outcomes
This is the point where duplication starts disappearing.
Separate control logic from framework language
A strong system separates:
- What the control does (logic)
- How frameworks describe it (mapping)
Your control should never change because a framework uses different wording.
For example:
- “User access recertification”
- “Logical access review”
- “Access enforcement validation”
Different language, same underlying logic.
If your system ties control logic to framework terminology, every update creates rework.
Connect controls to real system signals
Control mapping only works if it’s tied to actual system behavior.
Each control needs:
- A validation method
- A data source
- A measurable condition
For access control:
- Source: IAM / identity provider
- Signal: active users, roles, permissions
- Validation:
- MFA enabled
- no inactive users beyond threshold
- least privilege enforced
This is where mapping becomes executable, not theoretical.
Handle framework differences without breaking structure
Even with overlap, frameworks don’t align perfectly.
Some differences you need to handle:
- Control granularity (ISO is broader, NIST is deeper)
- Documentation expectations (SOC 2 vs ISO)
- Risk categorization (NIST vs others)
A good mapping system:
- Splits controls where needed
- Aggregates where possible
- Maintains traceability across all mappings
You’re not forcing frameworks to match. You’re creating a structure that can accommodate them.
Versioning is not optional
Frameworks evolve. Controls change.
If your system doesn’t track versions:
- mappings break silently
- audits become inconsistent
- historical traceability is lost
Each control should support:
- version history
- mapping updates
- audit traceability over time
So you can answer: “What was the control state during the last audit?”
What most tools get wrong
They map controls at a document level, not system level, they duplicate controls instead of normalizing them. They don’t connect controls to live data. They treat mapping as static instead of dynamic
This leads to:
- inconsistent compliance status
- repeated evidence collection
- manual reconciliation across frameworks
What proper control mapping achieves
When implemented correctly:
- One control satisfies multiple frameworks
- Evidence is generated once and reused
- Risk is tracked in a unified way
- Audit preparation becomes minimal
Most importantly, compliance stops being framework-driven and becomes control-driven.
Key Features of Compliance Automation Platform
Enterprise software compliance expectations have moved past basic automation. Collecting evidence and generating reports is now the baseline. What matters is how well a platform fits into real systems, development workflows, and day-to-day operations. Compliance is no longer treated as a separate activity. It is expected to run alongside infrastructure, deployments, and security monitoring.
The features below reflect how modern AI-powered compliance automation platform capabilities move compliance closer to how systems actually behave, instead of how audits are conducted.
| Feature | What It Looks Like in Practice | Why It Matters |
|---|---|---|
| Real-time compliance visibility | Dashboards update based on live system data, not periodic reviews. Control failures and risk exposure are visible instantly. | Teams can act on issues as they happen instead of discovering them during audits. |
| API-first architecture | Compliance data, control status, and evidence can be accessed and pushed through APIs across systems. | Enables integration with internal tools and avoids creating another siloed platform. |
| DevOps and CI/CD integration | Compliance checks are embedded into build and deployment pipelines. Non-compliant configurations are flagged or blocked before release. | Shifts compliance earlier in the lifecycle and reduces post-deployment fixes. |
| AI-assisted risk identification | System patterns, anomalies, and unusual behavior are analyzed to identify potential control gaps or risks. | Helps prioritize real risks and reduces noise from manual reviews. |
| Policy-as-code | Policies are written as code, versioned, and enforced during infrastructure provisioning and updates. | Aligns compliance with engineering practices and ensures consistent enforcement. |
What ties all of this together is a clear shift. Compliance is moving from documentation and review cycles to continuous validation inside systems. Platforms that support this shift don’t just help with audits. They reduce operational friction and improve how controls are enforced at scale.
Security and Compliance Considerations While Building the Platform
A compliance platform becomes part of the control environment itself. It stores logs, access data, control mappings, and audit evidence. That means it must meet the same standards it enforces across SOC 2, ISO 27001, and NIST.
Data sensitivity and classification
Compliance data is high-risk by default. It includes IAM roles, logs, and audit evidence that expose system behavior.
- Apply classification (restricted, confidential)
- Minimize storage and enforce retention policies
- Use masking or tokenization where needed
Aligns with ISO 27001 A.5/A.8 and NIST SC-28.
Role-based access control (RBAC)
Access must follow strict separation of duties.
- Auditors: read-only
- Engineers: scoped operational access
- Admins: restricted with approvals
Use RBAC + contextual controls (ABAC) and enforce least privilege.
Covers SOC 2 CC6.x, ISO 27001 A.9, NIST AC controls.
Audit trail integrity
Audit logs must be immutable and verifiable.
- Append-only storage (WORM or equivalent)
- Time-synced logs (NTP)
- Hashing or signed digests for tamper detection
Track all control, evidence, and remediation actions.
Maps to SOC 2 CC7, ISO 27001 A.12, NIST AU controls.
Encryption and key management
Encryption technology alone is not enough. Key control matters.
- TLS 1.2+ in transit, AES-256 at rest
- Centralized KMS (AWS KMS, Azure Key Vault)
- Key rotation and strict IAM policies
Aligned with ISO 27001 A.10 and NIST SC controls.
Multi-tenant vs single-tenant isolation
Architecture defines security boundaries.
- Multi-tenant: strong logical isolation, tenant-scoped keys
- Single-tenant: higher isolation, higher cost
Enforce isolation at application and data layers, not just infrastructure.
Relevant to SOC 2, ISO 27001 A.9/A.13, and NIST SC family.
What matters
Security here is not an add-on. It’s enforced through:
- controlled data exposure
- strict access boundaries
- verifiable audit logs
- enforced isolation
If this layer is weak, the compliance system itself becomes the biggest risk.
Common Mistakes in Compliance Platform Development
Most platforms don’t fail because of missing features. They fail because of how they’re designed. The problems usually stay hidden early on and show up when systems scale, audits increase, and multiple frameworks start overlapping.
Treating frameworks separately
Building separate tracks for SOC 2, ISO 27001, and NIST leads to duplicated controls, repeated evidence collection, and inconsistent definitions across systems.
- Over-engineering without control mapping logic
Investing in dashboards, workflows, or UI before defining a canonical control structure results in systems that look complete but cannot scale. Without one-to-many mapping, every framework update creates rework. - Ignoring integration complexity
Integrating a cloud that adheres with compliance logs, IAM systems, and security tools is not plug-and-play. Data formats differ, APIs fail, and pipelines break. If this layer is weak, automation becomes unreliable. - Lack of ownership and remediation workflows
Detecting issues is not enough. Without clear ownership, ticketing integration, and lifecycle tracking, control failures remain unresolved and audit readiness suffers. - Building dashboards without real data pipelines
Many platforms prioritize visibility over accuracy. When dashboards rely on manual updates or uploaded evidence instead of live system data, they create a false sense of compliance.
What these mistakes lead to
- Repeated manual effort
- Fragmented compliance visibility
- Broken automation pipelines
- Increased audit preparation cycles
More importantly, they prevent compliance from scaling as systems grow.
The pattern behind all of them
These mistakes come from treating compliance as a feature set instead of a system.
The fix is consistent across all of them:
- define controls once
- connect them to real systems
- build automation on top of that foundation
Without this, every improvement just adds another layer of complexity.
Cost of Building a Compliance Automation Platform
The cost to build a compliance automation platform typically falls between $40K and $400K+, but the range exists for a reason. What you’re really paying for is not features, but how deeply compliance is embedded into your systems and the complexity of compliance automation software implementation.
Cost of Building a Compliance Automation Platform
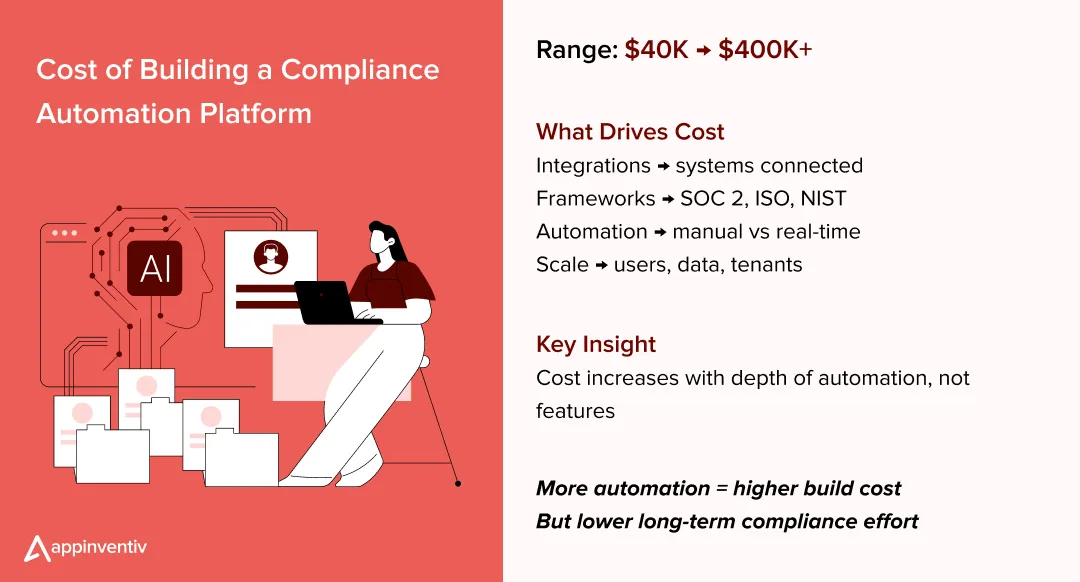 Integration complexity drives the foundation
Integration complexity drives the foundation
Most of the engineering effort goes into integrations, not interfaces.
Connecting cloud environments, identity providers, and logging systems sounds straightforward, but in practice:
- data formats differ across systems
- APIs have limits, latency, and failures
- logs are inconsistent or incomplete
Building reliable pipelines that can normalize and validate this data takes time. The more systems you integrate, the more complex and costly the platform becomes.
Framework coverage increases design complexity
Supporting multiple frameworks changes how the platform is structured.
When you move from one framework to unifying SOC 2, ISO 27001, and NIST:
- controls need to be normalized instead of duplicated
- mapping logic becomes more complex
- reporting must adapt to different audit formats
This is not just additional effort. It requires a different architecture from the start.
Automation depth changes long-term cost
There’s a clear difference between basic and advanced automation.
- Lower-cost systems rely on manual uploads and periodic checks
- Higher-end systems implement real-time monitoring, automated evidence, and continuous validation
Deeper automation increases upfront build cost, but reduces:
- manual effort
- audit preparation time
- operational overhead
This is where advanced compliance process automation delivers long-term ROI.
Enterprise scale adds system-level requirements
As the platform scales, costs increase beyond feature development.
You start designing for:
- high data volume from logs and events
- multiple users and roles
- strict access control and audit traceability
- tenant isolation (multi-tenant vs single-tenant)
At this level, you’re not just building functionality. You’re building for reliability, security, and performance under load.
What actually creates the price gap
Two platforms can look identical on the surface but differ significantly underneath.
The difference usually comes down to:
- whether controls are normalized or duplicated
- whether evidence is automated or manually handled
- whether monitoring is continuous or periodic
- whether systems are integrated or siloed
That’s why the cost range is wide. It reflects how far you move from checklist-based compliance to a system-driven approach.
Build vs Buy: Should You Develop or Use Existing Tools?
This decision usually comes down to one question: Do your compliance needs fit into a standard tool, or do they depend on how your systems actually operate?
Most off-the-shelf tools are designed to help you get audit-ready quickly. That works well in the early stages. But as systems grow and multiple frameworks like SOC 2, ISO 27001, and NIST start overlapping, limitations begin to show.
When building a platform makes sense
Building your own system is not about control for the sake of it. It’s about flexibility and alignment with how your infrastructure works, which is why many enterprises partner with a compliance automation software development company for custom builds.
- Custom workflows and control logic
If your compliance processes involve internal tools, unique approval flows, or domain-specific controls, off-the-shelf platforms struggle to adapt. A custom build lets you design workflows around your systems, not the other way around. - Regulatory and framework complexity
When you need to unify multiple frameworks or meet region-specific regulations, standard tools often treat them separately. Building allows you to normalize controls, reuse evidence, and avoid duplication across frameworks. - Enterprise scale and integration depth
At scale, integrations become the core of the system. If you need deep connections across cloud, IAM, DevOps, and security tools, along with real-time monitoring, a custom platform provides better control over data flow and performance.
In these cases, you’re not just building a tool. You’re building a system that becomes part of your infrastructure.
Also Read: The Role of DevOps in Compliance Management
When buying an existing tool is the better choice
Not every organization needs to build from scratch. In many cases, speed matters more than customization.
- Faster path to compliance
If your goal is to achieve SOC 2 or ISO 27001 certification quickly, existing tools provide pre-built templates, workflows, and audit support that reduce setup time. - Limited internal engineering capacity
Building a compliance platform requires backend engineering, integration expertise, and ongoing maintenance. If your team doesn’t have that bandwidth, buying a tool reduces complexity. - Standard compliance requirements
If your controls and workflows align with common industry practices, off-the-shelf solutions can cover most needs without heavy customization.
If you’re weighing build vs buy, it usually means your needs are already outgrowing standard tools.
How Appinventiv Builds Compliance Automation Platforms That Scale
Compliance automation tools development is not about assembling features. It’s about designing a system where controls, data pipelines, and validation logic work together in real time. As a software development company, Appinventiv brings deep expertise in compliance automation software development.
With 10+ years of experience, 1600+ specialists, and 3000+ solutions delivered, the focus stays on building platforms that hold up under enterprise complexity.
In practice, this means defining controls once and mapping them across frameworks like SOC 2, ISO 27001, and NIST. Evidence is pulled directly from cloud, IAM, and logging systems, while monitoring runs continuously to detect control drift. This approach ensures that compliance reflects actual system behavior, not static documentation. As part of our broader cybersecurity solutions & services, this shift helped the organization move from reactive audits to a system that stays consistently compliant as it scales.
FAQs
Q. What is compliance automation?
A. Compliance automation refers to using software systems to monitor, enforce, and validate regulatory controls without relying on manual processes. Instead of periodic audits, systems continuously track control behavior, collect evidence, and maintain audit readiness. Modern platforms go beyond basic tools and operate as a unified compliance management system, where controls, data, and workflows are connected.
Q. What types of regulations does compliance automation software handle?
A. Compliance automation software can support multiple frameworks and regulatory standards across industries. These include SOC 2 for trust assurance, ISO 27001 for information security management, and NIST for risk and cybersecurity controls. Depending on the system design, it can handle different types of regulations compliance automation software handles, including financial regulations, healthcare compliance, data privacy laws, and internal governance policies.
Q. Compliance automation software vs GRC platform: what’s the difference?
A. Traditional GRC (Governance, Risk, and Compliance) platforms focus on documentation, risk tracking, and policy management. Compliance automation software, on the other hand, focuses on execution. It integrates with systems, automates evidence collection, and continuously validates controls. While GRC tools help manage compliance, automation platforms actively enforce it through system-level integration and workflows.
Q. What is the ROI of compliance automation software?
A. The ROI comes from reducing manual effort, improving accuracy, and minimizing audit overhead. Organizations typically see faster audit cycles, fewer compliance gaps, and better visibility into risks. The benefits of compliance automation include reduced operational costs, improved control consistency, and the ability to scale compliance without increasing workload.
Q. What are common compliance automation software use cases?
A. Compliance automation is used across multiple scenarios, especially in regulated environments. Common compliance automation software use cases include automated access reviews, continuous monitoring of cloud configurations, incident response tracking, and audit-ready reporting. These use cases help organizations move from reactive audits to continuous compliance.
Q. What are compliance automation solutions and how do they help?
A. Compliance automation solutions are platforms designed to connect controls, systems, and evidence into a single workflow. These compliance automation solutions reduce duplication, improve control visibility, and ensure that compliance is maintained in real time rather than prepared periodically.
Q. How does an AI-powered compliance automation platform improve efficiency?
A. An AI-powered compliance automation platform enhances traditional automation by identifying anomalies, predicting risks, and prioritizing issues based on system behavior. Instead of relying only on predefined rules, AI helps surface patterns that may indicate compliance gaps, allowing teams to act faster and focus on high-impact risks.
Q. How does a SOC 2 compliance automation platform work?
A. A SOC 2 compliance automation platform maps trust service criteria to system-level controls, continuously monitors their execution, and generates audit-ready evidence. It integrates with cloud, identity, and logging systems to ensure controls like access management and data security are enforced consistently.
Q. How do ISO 27001 and NIST compliance automation platforms differ?
A. ISO 27001 compliance automation focuses on building and maintaining an Information Security Management System (ISMS) with structured policies and controls. A NIST compliance automation platform is more detailed in terms of risk categorization and technical controls. Both can be unified under a single system through control mapping and shared evidence pipelines.
Q. How can Appinventiv help automate compliance tasks?
A. Appinventiv helps enterprises design and implement platforms that automate compliance at the system level. By building integrated solutions that connect controls, data pipelines, and monitoring systems, we enable organizations to reduce manual effort and maintain continuous compliance. Whether it’s unifying multiple frameworks or building scalable automation workflows, the focus remains on delivering systems that align with real-world operational complexity.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.
Data Center Energy Management Software Development Guide: Architecture, Benefits & Costs
Key takeaways: Data center energy management software development starts with audits, architecture planning, and phased execution to ensure scale and reliability. Integration and testing connect real-time data and validate performance in live conditions. AI systems predict demand and adjust workloads and cooling for better efficiency. Costs depend mainly on energy usage, integration complexity, and scalability…

Biometric Software Development: Architecture, Compliance & Cost Guide for 2026
Key takeaways: Define the use case first. 1:1 verification and 1:N identification need different accuracy targets. Pair every modality with liveness. No liveness, no defense against a printed photo. Decide build vs. buy early. SDKs ship faster; custom only wins with proprietary ML needs. Go hybrid on architecture. On-device extraction, server-side matching — beats pure…
How to Build Workforce Management Software in Australia: What Businesses Should Know in 2026
Key takeaways: Custom workforce management software development in Australia is now a compliance and operational necessity for enterprises managing complex Modern Award structures. Award interpretation logic, integration architecture, and security posture aligned with the ASD Essential Eight are the three technical dimensions that distinguish audit-ready WFM platforms from basic scheduling tools. Total cost of ownership…