- Steps to Develop Biometric Software the Way Production Teams Actually Ship It
- What Biometric Software Development Actually Involves
- Technologies Powering Modern Biometric Software Development
- Biometric SDK and API Integration in Mobile and Web Apps
- U.S. Compliance Requirements for Biometric Systems
- Security Considerations and Data Privacy Risks
- Custom Biometric Software Development Cost: A Realistic Breakdown
- Biometric Software Development Trends Shaping 2026
- Biometric vs Facial Recognition: Settling the Confusion
- Real-World Use Cases of Custom Biometric Software Development
- Choosing a Biometric Software Development Company
- How Can Appinventiv Help You Out
- FAQs
Key takeaways:
- Define the use case first. 1:1 verification and 1:N identification need different accuracy targets.
- Pair every modality with liveness. No liveness, no defense against a printed photo.
- Decide build vs. buy early. SDKs ship faster; custom only wins with proprietary ML needs.
- Go hybrid on architecture. On-device extraction, server-side matching — beats pure cloud or pure edge.
- Red-team before launch. Test against real spoofs: photos, silicone, voice clones, deepfakes.
There’s a gap between what a biometric demo looks like and what ships, a gap most teams encounter during real-world biometric software development. A face-match API call works the first time you run it.
Six months later, your team is debugging why enrollment fails on Android devices with under-display sensors, why matching latency doubles on hotel Wi-Fi, and why the vendor’s 99% accuracy number translates to a noticeable false-rejection rate at your actual scale.
The market is pulling more teams into that gap every quarter. The biometrics market stands at $67.86 billion in 2026 and is projected to more than double to $136.86 billion by 2031, with software leading growth at a 16.35% CAGR.
This guide is for the team that has decided to build. The sections ahead walk through the sequence production teams actually follow: choosing a modality for the use case you have, deciding between build and buy, architecting for edge versus server-side matching, and budgeting against what the work takes.
Build secure, scalable biometric software with pipelines designed to resist deepfakes, spoofing, and model-level vulnerabilities from day one.
Steps to Develop Biometric Software the Way Production Teams Actually Ship It
Most failed projects do not collapse at the algorithm layer. They fail because compliance, hardware variance, and threat modeling were treated as late-stage concerns. Here is the sequence our engineering teams follow on every biometric system development engagement.
Step 1: Define the Identity Use Case and Risk Tier
Verification (1:1) and identification (1:N) are different problems with different accuracy tolerances. A bank logging in a known user can accept a different false match rate than a stadium scanning a crowd against a watchlist. Pin this down before any architecture conversation.
Types of Biometric Software and How to Choose the Right Modality
There is no universally best biometric. Each modality balances accuracy, cost, user friction, and spoof resistance differently, and the types of biometric software an enterprise selects shape every downstream architecture decision.
| Modality | Best For | Strengths | Trade-offs |
|---|---|---|---|
| Fingerprint | Mobile auth, workforce access, payments | Mature sensors, low cost, fast match | Wear and moisture degrade accuracy |
| Facial | Onboarding, KYC, airport boarding, device unlock | Contactless, scales via existing cameras | Bias risk, requires strong liveness |
| Iris | High-security access, border control, healthcare | Extremely high accuracy, lifelong stable | Hardware cost, user positioning required |
| Voice | Call center auth, hands-free workflows | Works over phone, no special hardware | Background noise, synthetic voice spoofing |
| Behavioral | Continuous auth, fraud scoring, banking | Passive, runs in background, hard to mimic | Requires ML training, longer enrollment |
| Vein / Palm | Hospitals, government, contactless payments | Hard to spoof, hygienic | Specialized hardware, less ubiquitous |
Across U.S. fintech and healthcare engagements, the highest-performing rollouts our team has shipped are almost always lean multimodal.
This trend strongly aligns with the broader evolution of cybersecurity in fintech, healthcare, and other sensitive industries where layered defenses outperform single-point authentication.
Face plus a behavioral signal works well for banking apps; fingerprint plus a device-bound cryptographic factor fits enterprise access.
Single-modality designs remain valuable for lower-risk, high-volume use cases like attendance tracking or device unlock.
Step 2: Select Modalities and a Liveness Strategy
Choose primary and fallback modalities based on user environment, hardware availability, and acceptable friction. Pair every modality with active or passive liveness detection. Without liveness, the system is one printed photo away from being bypassed.
Step 3: Map the Compliance Surface Early
Decide where templates live, who can access them, how long they are retained, and how a user revokes consent. These are not legal afterthoughts. They shape the data model. The U.S. compliance landscape gets a dedicated section further below.
Step 4: Build or Integrate the Core Engine
This is where build-versus-buy lands. Off-the-shelf SDKs from NEC, Innovatrics, Neurotechnology, AWS Rekognition, and Azure Face API accelerate time-to-market but lock teams into vendor accuracy curves and pricing.
Custom biometric software development is the right call when proprietary models, on-device inference, or modality combinations that no vendor offers as a single product become requirements.
Step 5: Engineer for Edge and Network Conditions
On-device inference reduces latency and keeps templates off the network. Server-side matching scales for large identification queries. Most production systems teams run a hybrid: feature extraction on-device, matching against a hashed template index in a secure backend.
Step 6: Build Audit, Monitoring, and Override Paths
Every match decision should log a confidence score, a model version, and a manual override path for moments when biometrics fail — and they will, for accessibility, injury, or environmental reasons. Auditors and regulators will ask for this. Build it on day one.
Step 7: Test Adversarially Before Launch
Red-team the system with printed photos, silicone fingers, voice clones, and deepfake video. NIST FRVT and IBeta PAD certifications are useful external validations, but internal adversarial testing against the actual deployment context is non-negotiable.
What Biometric Software Development Actually Involves
A biometric platform is engineered to capture, process, match, and store unique human identifiers, including fingerprints, faces, irises, voices, and behavioral patterns, then verify or identify a person in real time.
The work is rarely a single SDK drop. A production-grade system spans capture hardware abstraction, liveness detection, template extraction, encrypted storage, matching algorithms, decisioning logic, and audit-grade logging.
Every system, regardless of vendor or modality, runs on the same four-stage pipeline:
- Enrollment, where a user’s raw biometric is captured and converted into a mathematical template.
- Storage, where templates are encrypted and held on-device, in a secure enclave, or inside a hardened server-side vault — never as raw images.
- Matching, where a fresh capture is compared against the stored template using a similarity score and a calibrated threshold.
- Decisioning, where score, liveness signals, and contextual risk factors merge into an authentication or identification verdict.
The hard part is not any single stage. It is making all four resilient against spoofing, deepfakes, presentation attacks, and degraded capture conditions while staying under sub-second latency for consumer-grade UX.
This is where cybersecurity measures for businesses become foundational, not optional, particularly when biometric data is involved.
Technologies Powering Modern Biometric Software Development
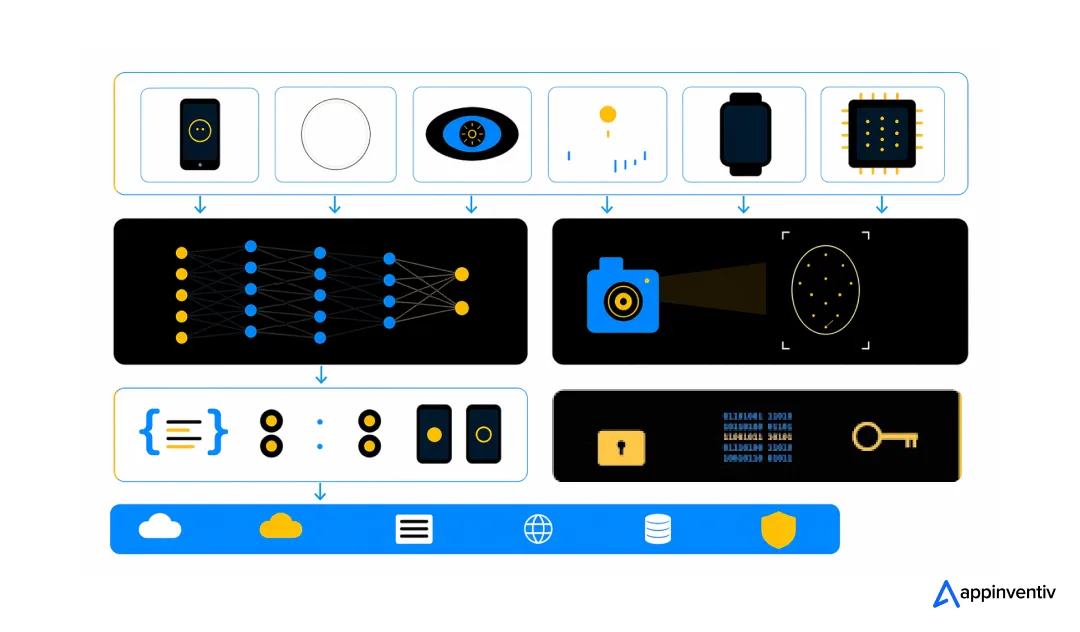
The modern stack is, fundamentally, an AI stack. The technologies showing up across every serious engagement our team has led include the following.
- Artificial intelligence and machine learning: Deep convolutional networks for face and fingerprint feature extraction; transformer-based models are increasingly used for cross-modal fusion and behavioral signal scoring.
- Computer vision: At a broader level, computer vision is shaping the future of biometric systems by enabling more accurate, context-aware identity verification. Image preprocessing, alignment, quality scoring, and presentation attack detection across varied lighting and pose conditions.
- Edge computing: On-device inference using Apple Neural Engine, Qualcomm Hexagon, or specialized NPUs keeps templates local and meets latency budgets without cloud roundtrips.
- APIs and SDKs: Native iOS and Android biometric SDK development, plus REST and gRPC APIs for server-side matching and policy decisioning.
- Cryptographic template protection: Cancelable biometrics, homomorphic encryption, and FIDO2-style key binding ensure templates can be revoked and never expose raw biometrics, even server-side.
- Cloud and hybrid infrastructure: AWS, Azure, and GCP with HIPAA-eligible services for healthcare workloads; FedRAMP-aligned environments for government deployments.
AI has fundamentally changed how these systems handle edge cases over the past three years. The same shifts driving AI in fintech — real-time anomaly detection, behavioral risk scoring, continuous decisioning — are now standard ingredients in authentication pipelines, particularly for banking apps that need session-long protection rather than just login-time checks.
Biometric SDK and API Integration in Mobile and Web Apps
Most biometric app development projects do not start from scratch; they integrate. SDK selection and API hygiene determine how easily a team can swap engines later, support new devices, or add modalities without ripping out the foundation.
What a Production-Grade SDK Should Expose
- Capture APIs that abstract device hardware (front camera, fingerprint sensor, microphone) with automatic quality scoring.
- In advanced implementations, facial recognition in software development is increasingly paired with behavioral and device-level signals for stronger identity assurance.
- Liveness detection callbacks are separated from match decisions, so thresholds can be tuned independently.
- Template export in standard formats (ISO/IEC 19794, ANSI/NIST-ITL) to avoid vendor lock-in.
- On-device matching mode for privacy-sensitive flows, plus encrypted template upload for server-side identification.
- Versioned model artifacts so the team can roll forward and back without breaking enrolled users.
Integration Patterns That Hold Up in Production
For mobile-first products, expert teams typically wrap the chosen SDK in a thin native layer and expose a single authenticate() call to the app that returns a signed assertion, never a raw template.
The backend verifies the assertion against a policy engine that can enforce step-up requirements based on transaction risk. This pattern keeps biometric API integration testable, swappable, and aligned with FIDO and WebAuthn standards.
U.S. Compliance Requirements for Biometric Systems
Biometric compliance in the United States is fragmented, and the fragmentation is a risk. There is no single federal biometric privacy law. Instead, every deployment manages a stack of state laws, sector regulations, and federal standards, each with different consent, retention, and breach notification rules.
| Regulation | Scope | What It Requires |
|---|---|---|
| BIPA (Illinois) | Any biometric data on Illinois residents | Written consent, public retention policy, statutory damages per violation |
| CCPA / CPRA (California) | Personal info of CA residents | Disclosure, opt-out, sensitive personal info handling for biometrics |
| HIPAA | PHI in healthcare | Encryption, access controls, BAA with vendors, audit logs |
| NIST SP 800-63 | Federal identity guidelines | Assurance levels (IAL/AAL), liveness, presentation attack detection |
| FTC Act Section 5 | All consumer-facing biometrics | No deceptive practices; FTC has actively enforced against biometric misuse |
| State laws (TX, WA, NY) | Biometric data of state residents | Notice, consent, and reasonable security controls |
| GDPR (if EU users) | EU residents’ biometric data | Explicit consent, DPIA, Article 9 special category protections |
BIPA has produced the largest U.S. settlements in this space, including nine-figure outcomes against major tech platforms. Any product touching Illinois residents must run explicit, written, auditable consent flows. The standard practice is to treat BIPA as the floor, not the ceiling.
For healthcare-adjacent systems, HIPAA layers on top: a biometric template linked to a patient identifier is PHI, full stop.
This overlap becomes critical in telehealth security, where biometric authentication must align with strict patient data protection requirements. That triggers Business Associate Agreements with every vendor in the pipeline, end-to-end encryption, and access controls mapped to the HIPAA Security Rule.
NIST SP 800-63-3, with the in-progress 800-63-4 revision, is the de facto reference for assurance levels. Federal contracts require alignment, and most enterprise procurement teams now ask for it even outside government.
Appinventiv ships HIPAA- and BIPA-compliant biometric systems that hold up against real-world deepfakes.
Security Considerations and Data Privacy Risks
Biometrics raise the stakes of a breach. A leaked password is replaceable. A leaked raw fingerprint template is not. According to IBM’s Cost of a Data Breach Report 2025, U.S. breaches now average $10.22 million, healthcare breaches average $7.42 million, and 97% of AI-related breaches occurred in organizations without proper access controls. Biometric systems sit at the intersection of all three risks.
The Threat Model Worth Defending Against
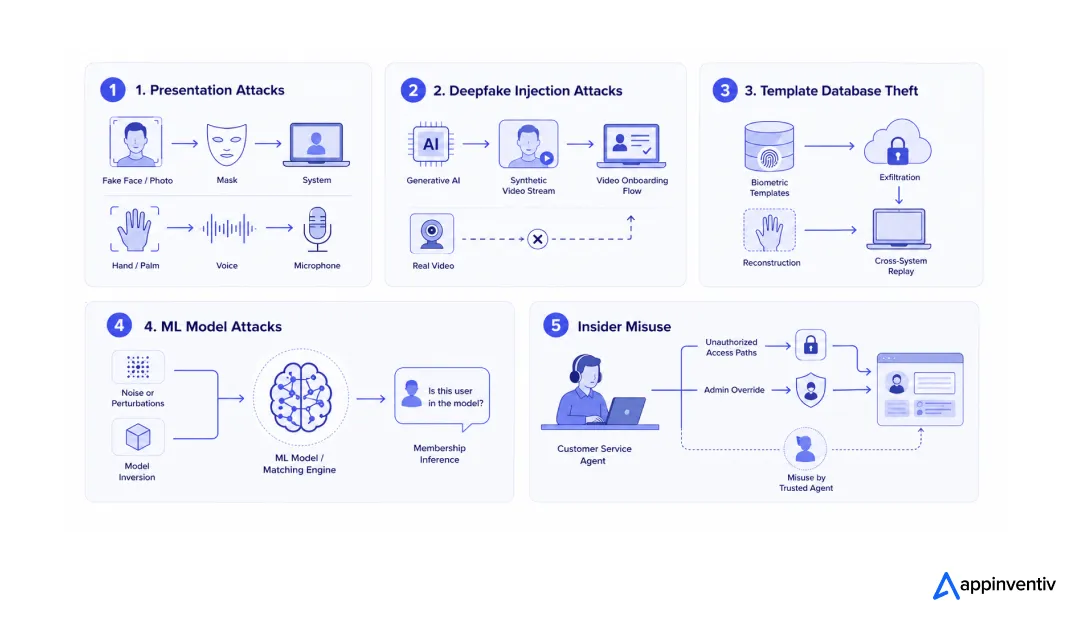
- Presentation attacks: printed photos, masks, silicone fingerprints, voice replays.
- Deepfake injection attacks against video onboarding flows are now industrialized through generative AI.
- Template database theft, where attackers attempt reconstruction or cross-system replay.
- Model inversion and membership inference attacks against the matching ML model itself.
- Insider misuse, especially through customer service and admin override paths.
Defenses That Actually Reduce Risk
- Store cancelable templates, never raw biometrics, and use per-user salts so the same finger produces different templates across services.
- Bind authentication to device-resident cryptographic keys (FIDO2, secure enclaves) so a stolen template cannot be replayed elsewhere.
- Layer passive liveness with active challenge-response, particularly on remote onboarding flows.
- Instrument every match decision with confidence scores and model versions for forensic traceability.
- Run continuous adversarial evaluation against the live model, not just at launch.
“In regulated environments, the security architecture has to assume the model itself will be probed. We design biometric pipelines so that even a complete compromise of the matching layer doesn’t expose raw user data, because the templates were never in raw form to begin with.”
Custom Biometric Software Development Cost: A Realistic Breakdown
Biometric software development cost varies more than almost any other software category our delivery team quotes. The spread between integrating a commercial SDK and building a custom multimodal engine is enormous. The ranges below reflect projects scoped or delivered over the past 24 months.
| Project Type | Typical Cost (USD) | Timeline | Best Fit |
|---|---|---|---|
| SDK integration into existing app | $40K – $90K | 8 – 14 weeks | Mobile fingerprint or face login |
| Mid-complexity app (single modality + backend) | $90K – $180K | 4 – 6 months | Workforce auth, KYC onboarding |
| Enterprise multimodal system (face + behavioral + admin) | $180K – $400K | 6 – 10 months | Banking, insurance, fintech |
| Custom-built with proprietary ML and certification | $400K – $1M+ | 9 – 18 months | Healthcare networks, government, identity platforms |
| Continuous SDK + multi-tenant API platform | $600K – $1.5M+ | 12 – 24 months | Identity-as-a-service products |
The variables that move the number most are the number of modalities, on-device versus server-side architecture, regulatory scope (HIPAA and BIPA add real engineering hours), accuracy targets at low false match rates, and certification needs like NIST FRVT or IBeta PAD.
Our scoping process maps these explicitly so the budget reflects the actual risk surface, not a generic SDK quote.
These are the same kinds of cost drivers often discussed when healthcare development budgets or fintech costs are planned, where compliance and risk directly shape engineering effort—making it essential to scope biometric projects against their actual risk surface rather than rely on generic SDK estimates.
Biometric Software Development Trends Shaping 2026
Five shifts are reshaping how systems are designed and shipped right now. None of them is speculative; each has crossed from research into production deployments over the past 18 months, and each carries a measurable data signal.
1. Generative AI Defense Is Now a First-Class Requirement
Deepfake injection attacks against remote onboarding have crossed from novelty to industrialized fraud. According to Entrust’s 2025 Identity Fraud Report, a deepfake attempt occurred every five minutes in 2024, and digital document forgeries jumped 244% year-over-year.
The Resemble AI Q1 2025 Deepfake Incident Report logged more than $200 million in deepfake-enabled fraud losses in a single quarter, with 38% of incidents originating in North America. Liveness detection is no longer optional, and pixel-domain liveness alone falls short. The new bar is multi-signal liveness combining sensor, network, and behavioral telemetry.
2. Passwordless and FIDO-Bound Biometrics Are Reaching Mainstream
Enterprises are retiring passwords in favor of passkeys, where biometrics unlock device-bound cryptographic credentials. The FIDO Alliance’s 2025 World Passkey Day research confirms that passkeys are now supported by 48% of the world’s top 100 websites, more than double the 2022 figure, and that 75% of consumers globally are now aware of the technology.
The FIDO Passkey Index, drawing on data from Amazon, Google, Microsoft, PayPal, Target, and TikTok, reports a 93% sign-in success rate with passkeys versus 63% for traditional passwords. This pattern eliminates the credential phishing surface entirely while keeping biometric data on-device.
3. Continuous and Behavioral Authentication Are Going Mainstream
Banks and high-value SaaS platforms are augmenting one-time login with continuous behavioral biometrics, including keystroke cadence, touch pressure, and gait, all scored quietly during a session.
A report found that 83% of fraud management professionals have already integrated biometric checks and 81% plan to expand them, with one in twenty verification attempts in 2024 flagged as fraudulent. Continuous authentication is the response to a threat surface that no longer ends at login.
4. Privacy-Preserving Biometrics Are Leaving the Lab
Homomorphic encryption and secure multi-party computation are moving into production deployments where matching happens on encrypted templates, and the matcher never sees the underlying biometric.
Adoption is being pulled forward by AI-related risk, since IBM’s 2025 Cost of a Data Breach Report found that 63% of organizations lack any AI governance policy and breaches involving shadow AI added an average of $670,000 to incident cost. Cancelable templates and encrypted-domain matching close the most expensive failure mode in this category.
5. Multimodal Fusion at the Edge
On-device chips are now powerful enough to fuse face, voice, and behavioral signals locally. The MarketsandMarkets Biometric System Market forecast identifies the contactless segment as the fastest-growing through 2030, driven by edge-capable hardware that collapses latency, reduces network exposure, and shifts the architecture toward zero-trust patterns by default.
Biometric vs Facial Recognition: Settling the Confusion
This question surfaces in nearly every discovery call, and the confusion costs companies real money in misaligned RFPs. Facial recognition is a single biometric modality. Biometrics is the broader category. The distinction matters because each answers different business questions and carries different regulatory weight.
| Dimension | Biometrics (Broad Category) | Facial Recognition (Specific Modality) |
|---|---|---|
| Scope | Any unique physiological or behavioral identifier | Facial geometry only |
| Modalities | Fingerprint, iris, voice, vein, behavioral, face | Subset of biometrics |
| Hardware | Sensor depends on modality | RGB camera, often paired with IR or depth |
| Best Use | Layered security, multi-factor flows | Frictionless verification at scale |
| Regulatory Heat | Varies by modality and jurisdiction | Highest scrutiny, BIPA and city-level bans |
| Spoof Risk | Modality-specific (e.g., latex prints) | Deepfakes, photo and video replay |
In practical terms, when a product team needs one-tap login on a mobile app, facial recognition typically wins on UX. When the goal is auditable, defensible access to PHI inside a hospital network, the right answer is a layered biometric system in which facial recognition is one factor among several.
Real-World Use Cases of Custom Biometric Software Development
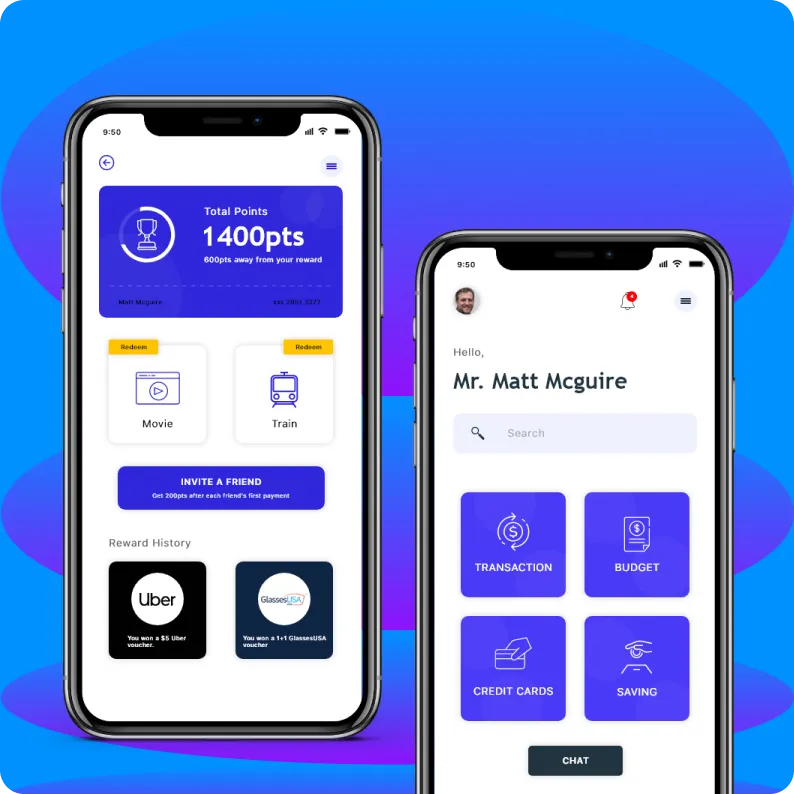
Banking and Financial Services
Mobile banking apps lean on facial recognition for login and high-value transaction approval, while behavioral biometrics, central to biometrics tech in digital banking, run continuously in the background to flag account takeover attempts. Voice biometrics are quietly replacing knowledge-based authentication in call centers, cutting handle time by 30 to 60 seconds per call in deployments our team has audited.
Healthcare
Patient identification at registration, clinician access to EHRs, and controlled-substance dispensing increasingly run on biometric authentication. The HIPAA-driven requirement for non-repudiation makes this an operational necessity, not a UX upgrade.
Hospitals modernizing their access stack typically pair authentication with broader healthcare software development initiatives, since EHR integration, role-based access, and audit logging all need to move together.
Travel and Aviation
U.S. airports have rolled out facial recognition at TSA checkpoints and boarding gates through programs like CBP Biometric Exit. Major carriers are integrating the same systems into mobile apps for off-airport bag drop and lounge access.
Enterprise Security and Workforce
Physical access control, time and attendance, and privileged access management are converging around unified biometric platforms. The shift to hybrid work has accelerated demand for remote workforce verification with strong identity assurance.
Retail and Payments
Pay-by-face and palm-vein payments are scaling in pilots across major U.S. retailers. The technology is mature; the bottleneck is consumer trust and consent UX, both of which are engineering problems as much as marketing problems.
Connect with experts who can build an unbreakable wall between your product, and cyber attackers.
Choosing a Biometric Software Development Company
If a partner-led approach makes more sense than building entirely in-house, the criteria that matter for a custom biometric software development company are narrower than for general software vendors. Here is what we tell prospects to evaluate, including when they are evaluating us against alternatives.
- Regulated industry depth: Has the team shipped HIPAA, PCI-DSS, or FedRAMP-adjacent systems in production?
- ML and computer vision in-house: Or do they outsource the hard parts to a sub-vendor outside the engagement?
- Vendor-neutrality on SDKs: A partner who only sells one engine will recommend that engine for every problem.
- Adversarial testing capability: Can they red-team their own deliverable, or does that responsibility shift back to the client?
- Post-launch model operations: Biometric models drift; the right partner treats this as ongoing, not one-time.
How Can Appinventiv Help You Out
Biometric software development sits at the intersection of three things that are individually hard and exponentially harder together: applied AI, regulated-industry compliance, and security engineering.
Our team has spent over a decade building systems where all three converge, including HIPAA-aligned healthcare platforms, fintech applications with continuous behavioral authentication, and enterprise identity systems serving millions of users.
When clients engage us for software development services for their biometric requirements, here is what they get:
- End-to-end ownership: Discovery, threat modeling, ML engineering, mobile and backend delivery, certification support, and post-launch model operations.
- Vendor-neutral architecture: We integrate the right SDK or build a custom engine based on the client’s problem, not on vendor relationships.
- Regulated-industry expertise: BIPA, CCPA, HIPAA, NIST 800-63, and GDPR experience baked into our delivery process, not bolted on at the end.
- Adversarial security testing: In-house red-teaming against presentation attacks, deepfakes, and model-level threats.
- Production-grade ML operations: Model versioning, drift monitoring, and continuous evaluation so accuracy curves hold up as the threat landscape evolves.
Recent work spans AI development services, mobile app development, and enterprise software development for regulated clients across BFSI and healthcare. To scope a biometric system, weigh build versus buy, or sign up for a compliance review, get in touch with our team for a working session with engineers who have shipped systems in your industry.
FAQs
Q. How do you develop biometric verification for mobile apps?
A. For low-stakes apps, just plug into Apple or Android’s native tools. But for real money or strict KYC, you need a hardened, third-party SDK. The golden rule: always handle extraction on the device itself and only send encrypted proof to your servers. Never let raw biometric data leave the phone.
Q. What compliances are required for biometric software development in the USA?
A. It’s a legal minefield. Illinois’ BIPA is the one that will bankrupt you if you mess up consent. California’s CCPA is right behind it. Touching healthcare? HIPAA applies. Doing federal work means adhering to NIST standards. And if even one EU user slips into your database, you’re dealing with the GDPR.
Q. Is biometric authentication safer than passwords?
A. Absolutely. Passwords are a disaster of reuse and phishing. Lock down a face or fingerprint scan to a physical device using FIDO2 standards, and you effectively kill the remote account takeovers that keep CISOs awake at night.
Q. How much does biometric software development cost?
A. Basic SDK integrations run $40K–$90K. A standalone app with its own backend is $90K–$180K. Enterprise, multi-modal systems hit $180K–$400K. If you want us to build proprietary machine learning models from scratch with full certifications, that’s a million-dollar conversation.
Q. How long does it take to build biometric software?
A. SDK integrations take 8 to 14 weeks. A single-modality app with a backend needs 4 to 6 months. True enterprise, multimodal systems take 6 to 10 months. Ground-up proprietary builds? Settle in for a 9 to 18-month grind.
Q. What technologies are used in biometric systems?
A. Deep learning handles the heavy feature extraction. We use edge computing locally on the phone so the actual biometric template never leaves the user’s pocket. It’s all tied together with standard APIs and hardcore cryptography like FIDO2 binding.
Q. How is AI used in biometric software development?
A. AI is the core engine. It extracts the identifying features and spots cheap presentation attacks—like someone holding a printed photo to the camera. Right now, we’re actively using AI to fight a security arms race against AI-generated deepfakes.
Q. What is the difference between biometric and facial recognition?
A. Biometrics is the massive overarching category covering any bodily authentication—fingerprints, voice, iris, vein patterns. Facial recognition is just one specific tool under that umbrella, but it’s the one that triggers the heaviest regulatory nightmares and public scrutiny.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

Compliance Automation Platform Development: Unifying SOC 2, ISO 27001, and NIST in One System
Key takeaways: Multi-framework compliance creates duplication unless controls are unified Compliance failures usually come from gaps between systems, not missing controls Automation shifts compliance from periodic audits to continuous monitoring A well-built platform connects controls, evidence, and workflows in one system Cost depends on integration depth and automation, not just features Most teams don’t fail…
Data Center Energy Management Software Development Guide: Architecture, Benefits & Costs
Key takeaways: Data center energy management software development starts with audits, architecture planning, and phased execution to ensure scale and reliability. Integration and testing connect real-time data and validate performance in live conditions. AI systems predict demand and adjust workloads and cooling for better efficiency. Costs depend mainly on energy usage, integration complexity, and scalability…
How to Build Workforce Management Software in Australia: What Businesses Should Know in 2026
Key takeaways: Custom workforce management software development in Australia is now a compliance and operational necessity for enterprises managing complex Modern Award structures. Award interpretation logic, integration architecture, and security posture aligned with the ASD Essential Eight are the three technical dimensions that distinguish audit-ready WFM platforms from basic scheduling tools. Total cost of ownership…