- The Hard Numbers: Breaking Down the True Cybersecurity Breach Cost in Australia
- Industry-Wise Benchmarks of Cybersecurity Breach Impact on Australian Enterprises: 2025–2026 Insights
- The Ripple Effect: Hidden and Long-Term Costs for Enterprises
- Current Threat Landscape in Australia: What the OAIC Data Actually Shows
- Key Vulnerability Drivers: Human Error vs. Emerging Technology Risks
- The Tranche 2 Privacy Act Reforms and Data Breach Penalties in Australia
- Why Cybersecurity Investment Is Now a Board-Level Financial Strategy
- Cost vs Investment: What Enterprises Spend vs What They Lose
- Key Cybersecurity Investments That Deliver the Highest ROI
- How AI Is Reshaping Breach Prevention and Cost Reduction
- A Step-by-Step Framework to Reduce Data Breach Impact in 2026
- The Future Outlook: Cyber Risk as a Core Business Metric
- Why Partner with Appinventiv for Cybersecurity Transformation
- FAQs
Key takeaways:
- The average cybersecurity breach cost in Australia has reached AUD 2.55 million in 2025, and that figure understates the true exposure for regulated industries when regulatory penalties, class litigation, and long-tail customer attrition are included.
- Data breach penalties in Australia have fundamentally changed. The maximum penalty for serious or repeated breaches is now AUD 50 million, or 30% of adjusted turnover, whichever is greater.
- Prevention investment is two to four times more cost-efficient than breach response. Organisations with tested incident response programmes and AI-assisted detection resolve incidents faster, at substantially lower total cost.
- Cyber resilience implementation for Australian enterprises is now a board-level governance obligation, a commercial necessity for supply chain participation, and a factor in cyber insurance viability.
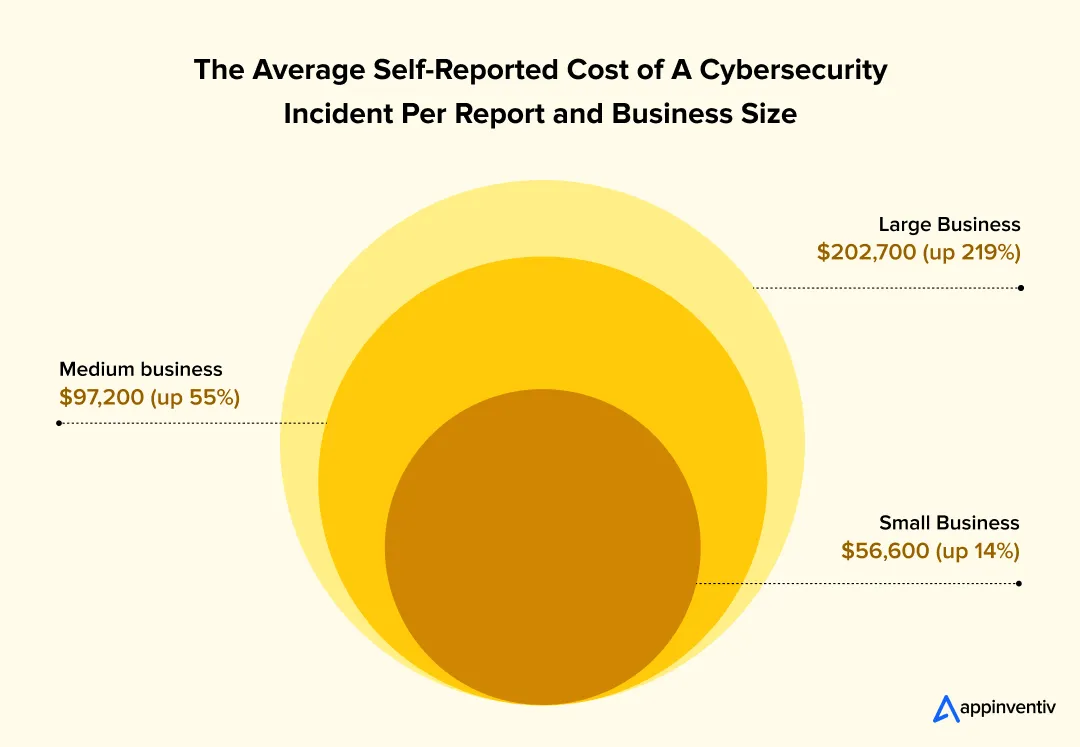
The Australian Signals Directorate and the Annual Cyber Threat Report 2024–2025 from the Australian Cyber Security Centre (ACSC) reveal an unsettling baseline: Australian organisations face a cybercrime report roughly every six minutes. For large businesses, the self-reported financial cost of a cybersecurity incident has skyrocketed by 219% to reach an average of $202,700 per incident, not including long-term reputational damage or regulatory penalties.
Behind those numbers are boards scrambling for answers, CISOs defending budget decisions, and executive teams suddenly accountable in ways the governance frameworks of five years ago never anticipated.
The cybersecurity breach cost in Australia is no longer a line item debated in IT steering committees. It sits alongside capital expenditure decisions, board risk registers, and audit committee agendas. The conversation has shifted; not because of panic, but because the numbers have become impossible to ignore.
This blog approaches this discussion from a delivery and advisory standpoint. The objective is not to quantify losses in isolation, but to build a full business case. One that reflects how the cost of cybersecurity breach in Australia compares against proactive investment decisions, how the regulatory terrain has hardened, and why waiting is becoming the most expensive option for enterprises operating at scale.
Contact Appinventiv’s enterprise architecture team to schedule a deep-dive cyber resilience and risk mitigation assessment tailored to your industry and regulatory obligations.
The Hard Numbers: Breaking Down the True Cybersecurity Breach Cost in Australia
The cost of cybersecurity breach in Australia has moved well past the realm of IT liability. For most enterprises, a single incident now triggers a cascading financial event that spans regulatory exposure, operational disruption, legal proceedings, and long-term customer attrition, all running simultaneously.
Global vs Regional Cost Trends
The global average breach cost in 2025 sits at approximately $4.44 million, according to IBM’s Cost of a Data Breach Report; a figure that has actually moderated slightly from the prior year, partly due to AI-assisted containment capabilities maturing in mature markets. Australia, however, does not sit at that average.
The average cost of a data breach in Australia has reached AUD 2.55 million in 2025, and that figure understates the exposure for regulated industries. The Medibank breach, affecting 9.7 million Australians and the Optus incident, which exposed the private data of nearly 10 million customers to cyber theft, are no longer cautionary footnotes. They are the real world examples of cyber breach cases that regulators and plaintiff lawyers now cite routinely.
Enterprise-Level Cost Breakdown
Understanding the cybersecurity breach impact on Australian enterprises requires disaggregating what “breach cost” actually encompasses.
- Direct Expenses: Retaining external legal counsel, public relations crisis management firms, and third-party forensic audit teams.
- Operational Loss: Loss of high-value client accounts, along with statutory penalties for disrupted or unavailable services.
- Technical Remediation: Reconstructing cloud environments, rotating compromised certificates, and re-issuing credentials.
Visualising the Financial Impact
The distribution of expenses across an incident timeline follows a standard pattern. Costs peak during the discovery and escalation phases and decrease once containment and notification procedures take effect.
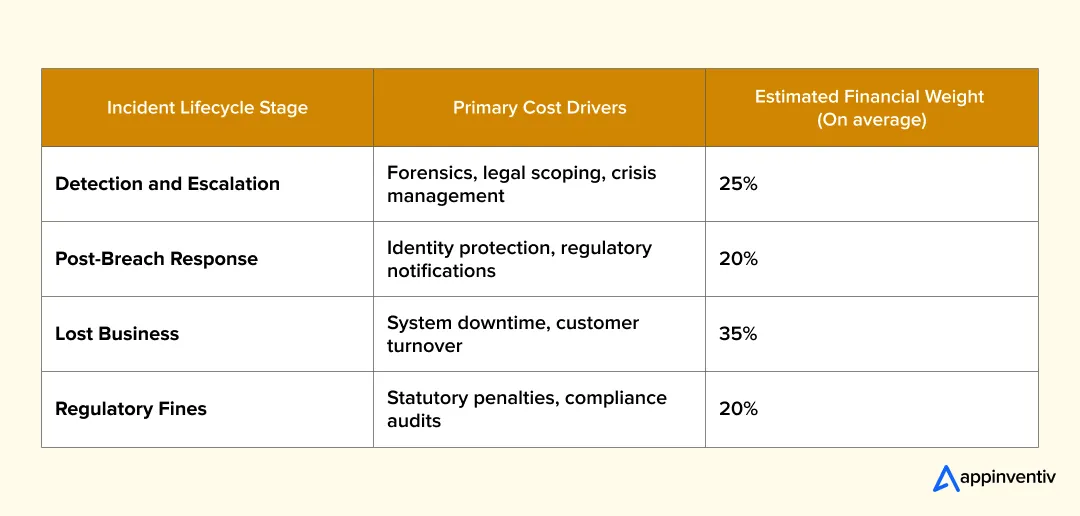
Illustrative allocation based on IBM Cost of a Data Breach Report 2024 and OAIC Notifiable Data Breaches statistics. Actual distribution varies significantly by sector, breach scope, and regulatory overlay.
Also Read: SIEM for App Security in Australia: Protecting Modern Apps
Industry-Wise Benchmarks of Cybersecurity Breach Impact on Australian Enterprises: 2025–2026 Insights
The cost of cyber attacks in Australia varies substantially by sector, reflecting differences in data sensitivity, regulatory obligations, customer relationship complexity, and systemic risk profiles.
Healthcare and MedTech
Healthcare systems in Australia carries the highest breach cost of any other sector, driven by the sensitivity of clinical data, mandatory NDB scheme reporting, and the fact that patient records retain value on criminal markets far longer than financial credentials.
The OAIC’s statistics for January to June 2025 show healthcare accounting for 18% of all reported data breaches – the highest of any sector. Compliance obligations under My Health Record legislation add jurisdictional complexity that amplifies both remediation cost and regulatory exposure.
Banking and Financial Services
Finance accounts for 14% of OAIC breach notifications. The financial services sector in Australia faces a dual exposure: the direct cost of fraud losses triggered by credential compromise, and the regulatory cost of APRA’s CPS 234 requirements, where demonstrated governance failures post-breach compound the penalty calculus significantly. The combination of statutory fines, civil liability, and APRA enforcement creates a regulatory stack that has no practical ceiling.
This was highlighted in 2026 by the Federal Court ordering FIIG Securities to pay $2.5 million in civil penalties for cybersecurity failures that allowed 385GB of confidential client data to be compromised.
Also Read: How to Develop a Secure FinTech App in Australia in 2026
Retail and E-commerce
Retail breaches carry a different cost profile. The direct financial loss is often lower at first measure, but customer lifetime value erosion drives the real damage. Australian consumers are demonstrably privacy-aware, and research across the sector consistently shows high switching rates within six months of a disclosed breach. For retailers with thin margins and high acquisition costs, the economics of customer churn post-breach can be more damaging than the incident response bill.
Government and Critical Infrastructure
The 2025 year-end review from Sparke Helmore noted that approximately 85% of Australian enterprises suffered a materially impactful cyberattack in 2025, with 41% hit more than once. Government agencies and critical infrastructure operators face costs beyond the financial: the Cyber Security Act 2024 now mandates incident reporting within 72 hours for critical infrastructure, with non-compliance carrying its own penalty exposure.
Comparative Cost Reference of Cybersecurity Breach in Australian Enterprises across Industries
| Sector | Avg. Incident Cost (AUD) | Primary Cost Driver | Regulatory Overlay |
|---|---|---|---|
| Healthcare | AUD 9.3M+ | Sensitive data, My Health Record | Privacy Act, NDB, OAIC |
| Financial Services | AUD 7.1M+ | Fraud losses, APRA CPS 234 | APRA, ASIC, OAIC |
| Retail / E-commerce | AUD 3.8M+ | Customer churn, notification costs | Privacy Act, NDB |
| Government / Critical Infrastructure | AUD 5.5M+ | Systemic disruption, political exposure | Cyber Security Act 2024, SOCI Act |
| Telecommunications | AUD 8.0M+ | Volume of PII, class litigation risk | ACMA, OAIC, Privacy Act |
Figures represent estimated total incident costs inclusive of direct, indirect, and regulatory components based on sector benchmarks and OAIC data.
The Ripple Effect: Hidden and Long-Term Costs for Enterprises
The hidden costs of cybersecurity data breaches in Australia receive far less attention than the headline fine or the forensic invoice. This is where enterprise financial modelling consistently falls short and where the true argument for prevention investment sits.
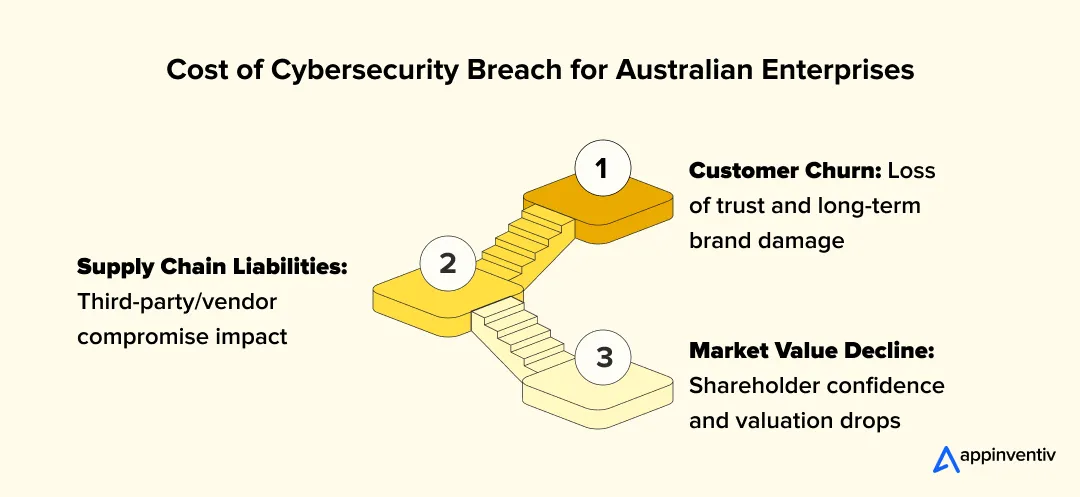
Customer Churn and Brand Damage
The hidden costs of cybersecurity data breaches in Australia include the loss of brand equity and customers’ trust. Australian consumers have demonstrated through repeated surveys and post-breach behavioural data that they will exit relationships with organisations they believe mishandled their data. A single breach notification email, required under the NDB scheme, triggers a churn event that may take two to three years to fully work through the revenue ledger.
In 2024, businesses globally lost an average of AUD 1.63 million in revenue due to churn and downtime attributable to breach incidents, per IBM’s global data. For Australian enterprises with concentrated customer books, the equivalent impact can be substantially higher.
Market Value Decline
Market value impact for listed Australian companies has been consistently documented. The pattern is well established globally and the Australian market has replicated it: share prices for publicly listed entities dip materially within the two weeks following a disclosed breach, and the recovery timeline correlates closely with how decisively management is seen to respond. For unlisted enterprises, the equivalent damage manifests in debt facility conditions, investor sentiment, and partner confidence.
Supply Chain Liabilities
Supply chain liability has escalated materially. The OAIC’s January to June 2025 statistics documented a significant increase in third-party-sourced breaches, with human error accounting for 37% of all notifications. When a vendor compromise triggers your own NDB obligation, you own the regulatory exposure regardless of where the breach originated. Contractual indemnity provisions help, but they do not neutralise the reputational consequences or the regulatory attention.
Case in Action – 1
A financial services client in Australia engaged Appinventiv after a third-party processor suffered a breach that exposed 11,000 of their customers’ records – data that had been forwarded to a subcontractor the client had never formally assessed. The contractual indemnity recovered a portion of the direct costs. It recovered none of the OAIC engagement cost, none of the reputational damage, and none of the pipeline losses that followed the public disclosure.
Current Threat Landscape in Australia: What the OAIC Data Actually Shows
Regulatory reporting highlights a steady increase in enterprise network intrusions. Here is a data breach statistics of Australia ecosystem to help technology leaders plan their defense budgets.
OAIC Reporting Analysis
Data from the OAIC Notifiable Data Breaches Report for January to June 2025 shows that malicious or criminal attacks account for 59% of notifications. Cyber attacks continue to target enterprise endpoints and digital infrastructure, often resulting in large volumes of compromised information.
Primary Attack Vectors
Threat actors focus on both technical vulnerabilities and human error. Misdirected emails, weak credential management, and third-party software errors remain the main points of entry for network intrusions across the Australian market.
- Phishing & Social Engineering: Attackers manipulate staff to gain internal network access.
- Compromised Credentials: Stolen user passwords used to target external systems.
- Third-Party Disclosures: Vulnerabilities introduced by third parties managing data.
Contact Appinventiv for a complete review of your digital workspace defenses.
Key Vulnerability Drivers: Human Error vs. Emerging Technology Risks
Human error remains the most persistent and underappreciated attack surface in Australian enterprise environments. But shadow AI has introduced a new category of risk that most organisations have yet to adequately price into their threat models.
The Human Factor
Internal staff remain the primary mechanism through which threat actors gain enterprise network access; not primarily through sophisticated technical exploits, but through social engineering, credential misuse, and misdirected data handling.
The OAIC’s increase in human-error notifications to 37% in the first half of 2025 is not an anomaly; it reflects the structural reality that technical perimeter controls have improved faster than employee security awareness programmes have kept pace.
Technology leaders must address these human vulnerabilities through secure system design, multi-factor authentication, and regular access audits.
Shadow AI Risks
Uncontrolled enterprise use of generative AI tools in Australia introduces major security risks. Employees often paste proprietary business data and software code into external LLMs. This practice creates vulnerabilities by exposing data to external training models. Organisations must deploy internal AI sandboxes and establish clear governance policies to prevent such leaks.
Case in Action – 2
Appinventiv’s security engineering engagements include an AI governance assessment as a standard component for enterprise clients. In a recent deployment for an Australian professional services firm, the assessment identified that 34% of staff were regularly using at least one unapproved AI tool in their work, and that three of those tools had terms of service that explicitly permitted training on user-submitted data.
An AI acceptable use policy and internal AI sandbox were implemented within six weeks. The client’s cyber insurer subsequently confirmed the governance update as a positive underwriting factor in their annual renewal.
The Tranche 2 Privacy Act Reforms and Data Breach Penalties in Australia
The Australian Privacy Act Reforms introduce stricter penalties and compliance obligations for data governance. The proactive adherence to these legal standards protects enterprises against heavy statutory fines.
Regulatory Context
Australia has updated its data privacy framework to address emerging technology risks, as detailed in the Australian Privacy Act reforms. The framework shifts the compliance focus from simple policy reviews to strict operational accountability.
This update introduces a tiered civil penalty regime that allows courts to fine organizations based on the severity of an incident. It also enforces new obligations for handling consumer data and processing personal information.
Statutory Fines and APP 11 Requirements
Australian Privacy Principle (APP) 11 requires organisations to take reasonable steps to protect personal information from misuse or unauthorized access. Failing to meet these standards leads to severe financial and regulatory penalties.
- Tiered Penalties: Fines scale according to the operational impact and scope of the failure.
- Statutory Tort: Individuals can pursue compensation for serious invasions of privacy.
- Mandatory Assessments: The OAIC can demand proof of how data is processed in your environment.
Automated Decision-Making Transparency
Organisations that use automated decision-making must update their privacy policies to explain how personal information is used. As outlined in the 2025 Privacy Reform Explainer, transparency is now mandatory for these processes.
[Proving ‘fair and reasonable’ use of data] is not an insignificant responsibility on the shoulders of entities who are going to be processing data, they won’t be able to cover their back with a consent-based approach.
— Carly Kind, Australian Privacy Commissioner
Why Cybersecurity Investment Is Now a Board-Level Financial Strategy
The framing of cybersecurity as an IT cost centre belongs to a governance model that Australian regulators, institutional investors, and advisory frameworks have collectively rejected. What has replaced it is an enterprise risk lens that places cybersecurity alongside treasury, legal, and operational risk in terms of board accountability.
Shift from IT Expense to Risk Asset
The shift is partly driven by regulation. The Cyber Security Act 2024, the Privacy Act amendments, and the Security of Critical Infrastructure Act collectively create personal accountability implications for directors.
The Corrs Chambers Westgarth regulatory overview for 2026 is explicit: directors must act in their company’s best interests, and taking reasonable steps to avoid foreseeable harm from cyber risk is now part of that duty.
CFO and CISO Alignment Trends
The relationship between financial and technical leaders ensures that security budgets match operational risks. Financial models now treat security spending as an investment that prevents significant capital losses rather than a sunk cost.
- Risk Quantification: Measuring the financial impact of potential operational disruptions.
- Vendor Consolidation: Reducing security tool complexity while improving network protection.
- Capital Allocation: Directing funds to high-ROI controls such as identity management and automation.
Cost vs Investment: What Enterprises Spend vs What They Lose
The prevention-versus-recovery economics are not subtle. The financial modelling across Australian enterprises consistently shows that prevention investment is two to four times more cost-efficient than breach response; yet most organisations are still underinvested relative to their actual risk exposure.
Australian enterprise cybersecurity budgets typically represent 5–8% of total IT spend for organisations with mature security programmes, and 2–4% for those still building baseline capability. The gap between those two cohorts becomes visible immediately following an incident: organisations with tested incident response plans and mature detection capability resolve breaches faster, with demonstrably lower total costs.
The cost of cyber attack in Australia is not a fixed event; it is a function of dwell time, data volume, and response maturity. Enterprises that invest in detection and response capability are not just buying faster recovery; they are structurally limiting the financial magnitude of the incident when it occurs.
| Investment Category | Typical Annual Cost (AUD) | Breach Cost Offset (Estimated) |
|---|---|---|
| AI-Driven Threat Detection | AUD 250,000–800,000 | AUD 2.2M+ reduction |
| Incident Response Retainer | AUD 80,000–200,000 | 35% reduction in total breach cost |
| Security Awareness Training | AUD 50,000–150,000 | Significant reduction in human-error breaches |
| Zero Trust Architecture Implementation | AUD 500,000–2M (over 3 years) | Structural reduction in lateral movement post-breach |
| Third-Party Risk Management Platform | AUD 100,000–400,000 | Supply chain breach exposure containment |
The Economic Insight
Underinvesting in security, leads to higher expenses during incident response. While advanced tools require significant upfront capital, they minimise operational downtime, avoid regulatory fines, and protect enterprise data.
Key Cybersecurity Investments That Deliver the Highest ROI
The cybersecurity breach prevention strategy for Australian enterprises should be built around investment decisions that generate compounding returns. The following categories have demonstrated consistent ROI across Australian enterprise deployments.

Zero Trust Architecture eliminates the assumption of implicit trust inside the network perimeter. For Australian enterprises with hybrid workforces and multi-cloud environments, Zero Trust reduces the blast radius of credential compromise, which remains the leading initial access vector, by requiring continuous authentication and least-privilege access enforcement.
AI-driven threat detection reduces mean time to detect (MTTD) from the industry average of 194 days to something operationally manageable. The gap between detection and containment is where breach costs compound most aggressively. MTTD reduction is not a nice-to-have metric; it is the primary financial lever in breach cost management.
Cloud Security Posture Management (CSPM) is particularly relevant for Australian enterprises running significant workloads in AWS, Azure, or Google Cloud. Misconfiguration remains a leading cause of data exposure, and CSPM tools provide continuous visibility into configuration drift that manual audit cycles simply cannot match.
Third-party risk management platforms address the supply chain vulnerability that the OAIC’s 2025 reporting flagged as a growing breach category. Organisations handling sensitive data through third-party processors need structured vendor security assessment programmes that go beyond annual questionnaires.
Security automation and SOAR compress response timelines, reduce analyst fatigue, and ensure consistent playbook execution during high-pressure incident scenarios. For Australian enterprises that lack the internal headcount to staff a 24/7 SOC, automation is the practical alternative.
How AI Is Reshaping Breach Prevention and Cost Reduction
Artificial intelligence implementation in Australia has simultaneously expanded the attack surface available to threat actors and provided defenders with tools that materially change the economics of breach prevention. For Australian enterprise security leaders, the question is not whether to deploy AI in security operations; it is how quickly they can do so effectively.
Predictive Threat Detection
Predictive analytics tools process large volumes of threat intelligence to identify attacks before they affect internal networks. This capability allows teams to block threat actors before they access the environment. By processing historical attack data, these models help security teams adapt to new threats and improve their defence posture.
Automated Incident Response
Security orchestration, automation, and response (SOAR) platforms isolate compromised endpoints and terminate suspicious user sessions automatically. This reduces the time needed to contain an incident, limiting potential data exposure. Automated operations reduce human error during emergencies and lower overall recovery costs.
Reduced Mean Time to Detect and Respond
Using AI engines drops the mean time to detect (MTTD) and mean time to respond (MTTR). This quick action limits the operational downtime caused by network attacks. Lower MTTD and MTTR values reduce business disruption and prevent significant financial losses.
Contact the Appinventiv technical team in Australia to integrate AI-driven threat intelligence into your operations.
A Step-by-Step Framework to Reduce Data Breach Impact in 2026
The cybersecurity breach prevention strategy for Australian enterprises should follow a sequenced implementation logic; not a checklist. Each step builds on the preceding one, and skipping steps creates the gaps that attackers exploit.
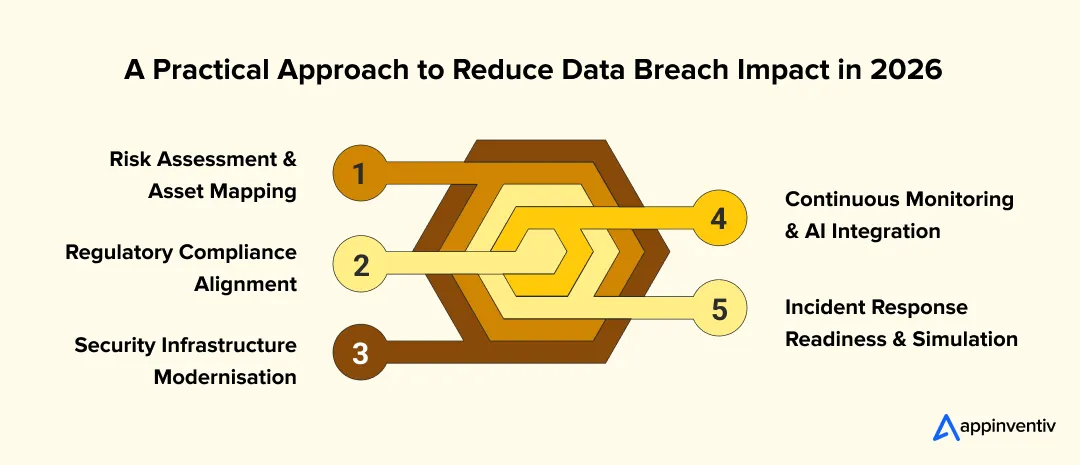
Step 1: Risk Assessment and Asset Mapping
Identify all critical data assets and endpoints. Review the security posture of third-party systems connected to the network to isolate potential vulnerabilities before external threat actors exploit them.
Step 2: Regulatory Compliance Alignment
Update data handling workflows to satisfy the Privacy Act and the Security of Critical Infrastructure Act. Aligning internal processes with ACSC guidelines reduces legal risks and financial penalties.
Step 3: Security Infrastructure Modernisation
Deploy identity and access management controls along with cloud posture platforms to protect workspaces. Modernising the architecture ensures only authenticated users access the data environment.
Step 4: Continuous Monitoring and AI Integration
Combine machine learning tools with data pipelines to monitor internal networks in real time. Continuous visibility helps security teams detect unusual activity and contain threats before they escalate.
Step 5: Incident Response Readiness and Simulation
Establish an incident response playbook and hold regular tabletop exercises with the board. A tested framework reduces confusion and enables teams to respond under pressure.
Also Read: How to Build a Secure App in Australia | Best Practices 2026
Appinventiv’s data engineering teams have delivered cyber security frameworks across 35+ industries in Australia.
The Future Outlook: Cyber Risk as a Core Business Metric
Cyber resilience implementation for Australian enterprises is moving from project to programme – a continuous operational capability rather than a periodic audit exercise. The regulatory and commercial environment of 2026 makes this transition not just prudent but necessary.
The Australian Government’s 2023–2030 Cyber Security Strategy; backed by AUD 586.9 million in government funding, sets a clear horizon. Horizon 2, running from 2026 to 2028, focuses on strengthening resilience through international framework alignment, scaled national threat intelligence, and public-private collaboration. Enterprises that are building their cyber resilience posture now are aligning with the national direction; those that are not will face increasing friction in government procurement, critical infrastructure partnerships, and regulatory relationships.
Cyber risk is entering financial reporting frameworks. The expectation that material cyber risks are disclosed in investor-facing communications is already embedded in ASX corporate governance principles, and is tightening. Board-level cyber risk KPIs – MTTD, MTTR, control coverage metrics, third-party risk scores – are becoming standard reporting elements for governance-mature organisations.
Surfshark’s Q1 2026 analysis estimated that 1.1 million Australian accounts were exposed in the first three months of 2026 alone. Since 2004, the cumulative estimate for Australian account exposure stands at 207.2 million, for a country of 26 million people.
The mathematics of that gap reflects how long unaddressed historical data, weak access controls, and under-resourced security programmes compound over time. The enterprises that are addressing that compounding now are the ones that will not be explaining it in a regulatory inquiry later.
Why Partner with Appinventiv for Cybersecurity Transformation
As a digital product engineering company in Australia with more than a decade of APAC delivery experience, Appinventiv’s approach to cybersecurity is built on the same principle that governs our broader engineering practice: security that does not support the business case is security that will not be sustained.
As an approved supplier on the Queensland Government ICTSS and the Local Buy LGA procurement panels, Appinventiv supports Aussie organisations by:
- Designing Zero Trust and AI-driven security architectures
- Aligning systems with Australian regulatory frameworks
- Building enterprise-grade incident response readiness
- Delivering measurable ROI through reduced breach exposure
The focus is not just on preventing attacks but on engineering security as a long-term business advantage.
Our security engineering practice has:
- Deployed 3000+ secure digital platforms for Australian businesses, including Rapid Teachers, Multinail, Lite N’ Easy and so on.
- Maintained a 96% client retention rate across a portfolio spanning 35+ industries
- Delivered measurable efficiency gains averaging 35% in Australian enterprise operations
- Maintained 99.5% compliance SLA against ISO and SOC2 requirements
- Been recognised among APAC’s high-growth companies by Statista and the Financial Times for two consecutive years
We operate as a Cyber Security Services Company with hands-on delivery depth in regulated environments, healthcare, financial services, government, and critical infrastructure, where the stakes of getting security architecture wrong extend well beyond the technology team.
Our practice integrates AI-driven threat detection, Zero Trust architecture, compliance-aligned governance frameworks, and incident response readiness into a coherent programme that boards can report against and audit committees can assess. We do not deliver security in isolation from the business; we build it into the fabric of how your systems operate and how your organisation governs itself.
Talk to Appinventiv about building a cybersecurity investment programme that is commercially sound, regulation-aligned, and built to scale with your business. Contact our team today.
FAQs
Q. How much does a cybersecurity breach cost Australian enterprises in 2026?
A. The average cybersecurity breach cost in Australia sits at approximately AUD 2.55 million in 2025. However, that average masks significant sector variation. Healthcare and financial services enterprises have faced incidents well exceeding AUD 50 million in total costs when regulatory penalties, legal defence, forensic investigation, and customer attrition are aggregated over a 24–36 month window.
Q. What cybersecurity measures should Australian enterprises prioritise after a breach?
A. The immediate priorities after a breach are containment, OAIC notification (within the NDB scheme’s applicable timeline), and forensic investigation to understand breach scope and entry point. Beyond that, enterprises should undertake a structured gap analysis against their current controls, remediate the specific vulnerabilities exploited, and implement continuous monitoring capability to detect recurrence. Engaging a tested incident response partner prior to an incident is significantly more cost-effective than sourcing one under pressure.
Q. What are the hidden business consequences of cybersecurity breaches?
A. The hidden costs of cybersecurity data breaches in Australia include customer lifetime value erosion through churn, increased cyber insurance premiums post-incident, ongoing regulatory monitoring obligations, third-party contract liability, and the opportunity cost of leadership time diverted to breach management. For publicly listed companies, share price impact adds a further dimension. These costs typically accumulate over 12–36 months and can exceed the direct incident response bill.
Q. How does the NDB scheme affect breach costs for Australian enterprises?
A. The Notifiable Data Breaches scheme requires mandatory notification to both the OAIC and affected individuals following an eligible data breach. Direct costs include communications management, identity monitoring services, and legal review of notification obligations. Indirect costs include the regulatory scrutiny that a formal notification triggers, and the class action risk that major breach notifications consistently generate. The scheme also creates a documented public record that plaintiffs’ lawyers and regulators use as a baseline for subsequent action.
Q. Is cybersecurity investment genuinely cheaper than breach recovery?
A. Consistently, yes. Prevention investment in detection capability, Zero Trust controls, and incident response readiness delivers a return that substantially outperforms reactive recovery economics. IBM’s research across the Australian context shows that AI and automation in security operations reduce breach costs by over AUD 2.2 million on average. An incident response plan that has been tested reduces total breach cost by approximately 35%. The prevention investment required to achieve those outcomes is a fraction of those savings. For Australian enterprises, the business case for cybersecurity investment has never been clearer.
Q. Why is cyber resilience implementation essential for Australian organisations in 2026?
A. Beyond the regulatory obligation, cyber resilience implementation for Australian enterprises is increasingly a commercial prerequisite. Supply chain partners, government procurement processes, institutional investors, and cyber insurers are all assessing security maturity as a condition of doing business. Organisations that cannot demonstrate tested, governed security capability are facing commercial friction that compounds over time and that friction is now growing faster than the threat landscape itself.
Q. How can Australian businesses prevent large-scale cyber attacks?
A. Australian businesses can prevent large-scale cyber attacks by implementing the Australian Cyber Security Centre (ACSC) Essential Eight mitigation strategies and establishing baseline governance. Key preventive actions include:
- Mandate Multi-Factor Authentication (MFA): Require secondary verification for all user accounts and remote access connections.
- Patch and Update Systems: Regularly update software, operating systems, and internet-facing services to close security gaps.
- Restrict Administrative Privileges: Limit the number of users with access to critical infrastructure and core network levels.
- Encrypt and Back Up Data: Maintain regular, offsite, and automated backups of critical files.
- Train Employees: Run routine cybersecurity awareness and phishing simulations to mitigate human error.
- Audit Third-Party Vendors: Ensure supply chain partners meet baseline cybersecurity standards.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.
Security for AI: Protecting Your Innovation in the Era of Intelligent Attacks
Key takeaways: AI security now covers models, prompts, data pipelines, agents, APIs, retrieval systems, and outputs. Prompt injection, data leakage, model theft, poisoned data, and unsafe agents are major enterprise risks. Secure AI starts early with threat modeling, access control, guardrails, vendor checks, and monitoring. RAG systems need permission-aware retrieval, so sensitive documents do not…

From Legacy Security to Zero Trust Architecture: Upgrading Enterprise Security in Australia
Key takeaways: Australian cybercrime now costs large businesses $202,700 per incident on average, making Zero Trust architecture a board-level financial imperative Zero Trust is a phased programme, not a product. Identity controls, microsegmentation, and ZTNA must be sequenced deliberately to avoid operational disruption. Full ZTA implementation in Australia ranges from AUD 70,000 to 700,000+, but…

Claude Mythos: The Hidden AI Security Risks in Enterprise Digital Transformation
Key takeaways: AI is expanding the attack surface inside workflows, not just infrastructure, making traditional security visibility incomplete. Claude Mythos highlights a shift where risk comes from model behavior, prompts, and integrations, not just system vulnerabilities. Most enterprise AI risks do not start as breaches, they begin as small gaps in prompts, access control, or…