- Why Are Businesses Investing in Cybersecurity Services?
- A Comprehensive View of the Costs Involved in Cyber Security Implementation
- Service-Wise Cybersecurity Cost and Hourly Rate Breakdown
- Key Factors That Influence Cyber Security Implementation Cost
- Enterprise TCO: A Realistic View of Cyber Security Cost
- ROI Breakdown of Cyber Security Investment
- Hidden Costs of Cybersecurity Implementation
- Ways to Optimize Cybersecurity Costs
- Turn Cybersecurity into a Strategic Investment with Appinventiv
- FAQs
Key Takeaways
- Cybersecurity cost scales with risk, infrastructure size, and compliance requirements, not just tools.
- Enterprise implementation can range from $50,000 to $2,000,000+ based on complexity.
- Ongoing operations, such as monitoring and response, drive long-term cybersecurity expenses.
- Industry, geography, and service model significantly influence overall pricing.
- A risk-based approach helps optimize spending while maintaining strong security coverage.
How much is enough to ensure cyber security for a business? The problem is that security costs do not grow linearly. With growth comes more risk, more regulation and more complexity. What starts as a manageable cost can grow rapidly when you include operational monitoring, response, governance and other costs. That’s where the cyber security services cost moves from a one-off implementation cost to an ongoing investment in business continuity and risk mitigation.
Realistically, how much cybersecurity implementation costs varies by maturity and complexity. A basic setup may start around $50,000 to $150,000, while mid-level programs typically fall between $150,000 and $400,000. Complex infrastructures that support real-time detection and compliance monitoring can cost $400,000 to $900,000+; and enterprise ecosystems can cost $900,000 to $2,000,000+.
This includes not just the tools, but the integration, monitoring and response capabilities. This is critical to assessing the total cost of ownership, where initial set-up is just the starting point for a bigger, ongoing commitment to security operations and resilience.
Let’s have a deeper look at all the essential breakdowns!
Talk to our cyber experts to build a resilient, future-ready security strategy.
Why Are Businesses Investing in Cybersecurity Services?
Cybersecurity spending is on the rise as the cost of security breaches continues to grow. The global end-user expenditure on information security will grow to $213 billion in 2025 and is likely to increase to $240 billion in 2026. Meanwhile, According to the Cost of a Data Breach Report 2025, the average global cost of a data breach remains at $4.4 million, despite a 9% decrease due to quicker detection and response.
These figures show that the cost of cybersecurity is no longer optional spending but a necessary investment to reduce larger financial exposure and business disruption.
The report also outlines the new risks associated with emerging technologies. Some 97% of businesses say they have experienced a security incident involving AI, but do not have AI access controls in place.
Again, Shadow AI increases breach risk by introducing unmonitored tools and data flows that bypass established security controls.

This illustration above discusses how it impacts organizations across data compromise, operational disruption, rising security costs, and reputational damage.
This suggests an imbalance between the pace of technology deployment and governance. Consequently, more money is being spent on prevention, monitoring and incident response activities, which continues to drive overall cybersecurity costs across industries.
A Comprehensive View of the Costs Involved in Cyber Security Implementation
The implementation of cyber security is not a one-off deployment activity. It constitutes an ongoing coordination of systems, users, infrastructure and policies with changing threats. Cost structure is pushed by visibility, control, response capability and compliance readiness as opposed to the simple acquisition of tools.
At an enterprise level, the cyber security cost indicates the extent to which the organization has integrated controls into its infrastructure, the speed of threat detection and containment, and the ability to comply with regulatory requirements.
Breakdown of the Costs by Detail as Per Complexity Levels
Security complexity is based on the size of the infrastructure, the number of endpoints, cloud migration, the presence of regulatory exposure, and the level of monitoring and response. The cost of cybersecurity increases as organizations evolve to real-time detection and automated response instead of preventive controls.
| Complexity level | Description of the scope | Cost estimate |
|---|---|---|
| Minimal Security Installation | Antivirus, firewall, minimal endpoint security, marginal monitoring | $50,000 – $150,000 |
| Intermediate Security Program | Endpoint detection, IAM, network security, basic SIEM and limited cloud security | $150,000 – $400,000 |
| State-of-the-art Security Architecture | Zero trust, cloud, SIEM/SOAR, threat intelligence, compliance controls | $400,000 – $900,000+ |
| Enterprise Security Ecosystem | Full SOC, automation, AI-driven detection, multi-cloud security, regulatory alignment | $900,000 – $2,000,000+ |
On a fundamental level, security is concerned with prevention and fundamental visibility. With the rise in complexity, systems need to process real-time detection and automated response and integrate distributed environments. Enterprise-grade systems with AI-powered cybersecurity add continuous monitoring, auditability and resilience, which adds high cost and engineering effort.
Breakdown of the Costs as per Implementation Stages
Implementing cyber security is in phases. In contrast to typical IT projects, subsequent phases, including monitoring and response, have a continuous operational burden, which directly translates to the overall cybersecurity costs.
| Implementation Phase | Scope Focus | Cost Covers |
|---|---|---|
| Assessment & Planning | Risk analysis, asset discovery, vulnerability assessment, compliance gap analysis | 10% – 15% |
| Security Architecture Design | Control selection, zero trust design, identity and network planning | 15% – 20% |
| Deployment & Configuration | Tool configuration, endpoint protection, Implementation of IAM, Firewall configuration | 20% – 25% |
| Integration & Testing | SIEM integration, log aggregation, threat simulation and validation testing | 15% – 20% |
| Monitoring Setup (SOC) | Alerts, dashboards, incident operations, response plan, books of knowledge | 15% – 20% |
| Continued Operations and Improvement | Threat hunting, patching, updates, compliance audits, optimization | 15% – 25%/year |
Early stages can be intensive, involving the IT and security teams. The testing is highly vigorous because it requires robustness to withstand actual attacks. In the long run, operational expenses prevail as monitoring, response and compliance keep on changing.
Breakdown of Costs by Region
Labor rate differences affect regional cost variation, but hourly pricing differences seldom have as great an effect as expertise in security architecture, IT regulations, and compliance frameworks. This balance directly influences the overall cyber security services cost.
| Region | Mean Hourly Rate | Estimated Cost Range |
|---|---|---|
| North America | $100 – $220/hour | $300,000 – $2M+ |
| Western Europe | $80 – $160/hour | $250,000 – $1.5M+ |
| Eastern Europe | $40 – $90/hour | $150,000 – $800,000 |
| India & South Asia | $20 – $60/hour | $80,000 – $500,000 |
| Southeast Asia | $25 – $70/hour | $100,000 – $600,000 |
Although offshore areas help decrease initial expenses, lapses in sophisticated threat identification, compliance proficiency, or cloud application security may result in rework. The location determination would impact the cost-effectiveness and risk exposure.
Industry-Wise Cybersecurity Implementation Cost
The cost of cybersecurity implementation is huge in different industries. The differences are influenced by regulatory pressure, data sensitivity, exposure to threats and operational complexity. Financial cybersecurity, personal healthcare data, and critical infrastructure are sectors that typically require more controls, ongoing monitoring, and stricter compliance validation.
The table below shows a systematic view of cost differentiation at the industry level.
| Industry | Scopes Focus | Estimated Cost Range |
|---|---|---|
| Financial Services | Payments, fraud, identity, regulatory (PCI DSS, SOX) | $300,000 – $2,000,000+ |
| Healthcare | Data protection of patients, EHR systems, and security of devices, HIPAA compliance | $200,000 – $1,500,000+ |
| E-commerce & Retail | Payment gateways, protection of customer data, monitoring frauds, PCI compliance | $150,000 – $800,000+ |
| Manufacturing | OT/ICS security, supply chain protection, endpoint and network security | $200,000 – $1,000,000+ |
| Technology & SaaS | Cloud security, API protection, identity access management, DevSecOps | $250,000 – $1,200,000+ |
| Government & Public Sector | National security systems, protection of citizen data, frameworks that are compliance-heavy | $500,000 – $3,000,000+ |
| Education | Protection of data of students, access control and network monitoring | $80,000 – $400,000 |
| Logistics & Transportation | Fleet systems, IoT security and real-time tracking protection | $150,000 – $700,000+ |
The cyber security charge per sector is not only based on the quantity of tools applied but also on the risk tolerance and the state of compliance maturity. The focus of a retail business can be on transaction security and fraud detection, but a healthcare provider has to guarantee end-to-end data protection and regulatory compliance.
Awareness of these industry-specific cost patterns assists organizations in benchmarking their costs and designing cybersecurity risk management programs that are aligned with risk exposure and business goals.
Service-Wise Cybersecurity Cost and Hourly Rate Breakdown
Cybersecurity is not a monolithic service. It is a combination of roles that cover the spectrum of risks, including prevention, detection and recovery. The costs depend on the complexity, speed and expertise of the services. Companies frequently purchase a range of services, so knowing the cost range for each helps to assess the budget for multiple services.
| Cybersecurity Service | What it Does | Average Hourly Cost |
|---|---|---|
| Threat Monitoring and Detection | Continuous network monitoring, anomaly detection, and early warning systems to detect potential threats | $100 – $150 |
| Incident Handling and Recovery | Containment of attacks, isolation of systems, recovery strategies, restoration of systems post-breach | $120 – $180 |
| Security Audits and Compliance Checks | Review of systems, policies, and controls to ensure compliance with regulations and identify security gaps | $90 – $140 |
| Identity and Access Control | Implementation of user authentication systems, role-based access, and privilege management for applications | $100 – $160 |
| Penetration Testing and Simulation | Simulated attacks to identify vulnerabilities in applications, networks and infrastructure | $120 – $170 |
| Cloud Security Management | Protection of cloud services, configuration reviews, and data security within multi-tenancy environments | $110 – $160 |
| Digital Investigation and Analysis | Review of logs, user activity and system events to trace incidents and detect patterns of attack | $110 – $150 |
These are approximate figures and can vary based on the service provider’s skillset, location, and time sensitivity. Services that are highly complex or require immediate attention tend to be on the higher end.
A Practical Formula to Estimate Cybersecurity Implementation Costs
Estimating cybersecurity spend is rarely straightforward. The numbers shift with the size of the environment, how reachable those systems are, and the kind of data they handle. A simple hourly rate does not hold up once these factors come into play. A structured model gives a clearer baseline for planning.
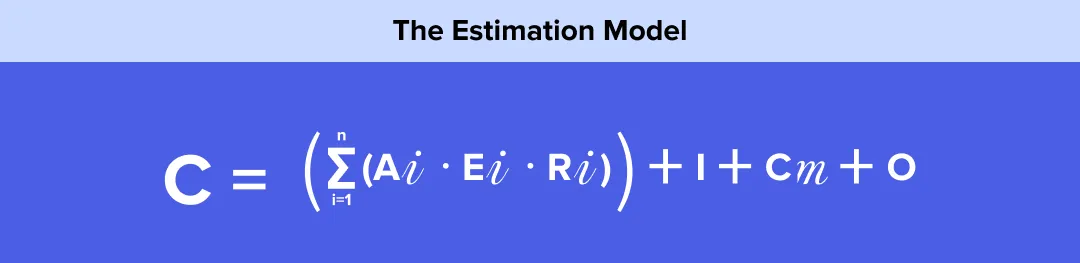
This isolates the work that is involved in the securing of assets and the additional workload in the form of tools, regulatory work and its continued operations.
What Each Component Represents
1. Asset Scope (Aᵢ)
This is the number and variety of systems in extent. It consists of endpoints, servers, APIs, cloud workloads, and user identities. With an increase in the size of the environment, coordination effort and coverage requirements also increase.
2. Exposure Level (Eᵢ)
This indicates the accessibility of each group of assets. The exposure of systems to the internet, remote access systems, and third-party connections augments this value. Increased exposure normally entails stricter controls and more testing.
3. Risk Weighting (Rᵢ)
This takes into consideration the effect of a possible breach. Payments, medical data, or core business operation systems are more weighty. The more serious the impact, the more stringent the controls and validation processes.
Additional Cost Layers
4. Infrastructure Cost (I)
This includes the tools and platforms that are necessary to implement security. Common products are monitoring systems, endpoint protection, access control and network defenses.
Much of this expense, or the actual cost of cybersecurity implementation, is seen early in this program.
5. Compliance Overhead (Cₘ)
This involves the effort required to comply with regulatory and audit requirements. It includes documentation, control mapping, internal reviews and external audits. The industries that are highly regulated will experience a rapid growth in this portion.
6. Operational Cost (O)
This is the struggle to maintain security. It involves oversight, handling incidents, period review, and updating. In the long run, this turns into a consistent and oftentimes prevailing cost.
Get a customized estimate aligned with your business and security priorities.
The Quick Rundown of Time and Effort Estimates
Implementation schedules are based on infrastructure size, level of integration and monitoring maturity, not just on the use of tools. Such timelines have a direct impact on the overall cyber security cost because rollouts are expensive, with long rollouts that raise operational overheads.
| Project Type | Project Life Span (Duration) | Project Effort Intensity |
|---|---|---|
| Minimal Security Implementation | 2-4 months or less | Small group, few controls |
| Intermediate Security Program | 4-8 months | Medium-sized team, several systems |
| Advanced Security Deployment | 8-14 months long | Large team, multi-layered controls |
| Enterprise Security Transformation | 12-24+ months | Multi-team, ongoing monitoring and compliance |
In practice, timelines are stretched by the process of iterative testing, the need to adjust threat models, and progressive departmental rollout. The effort is frequently hidden in the field of monitoring configuration, incident response configuration, and end-user training, which further supports the idea that cyber security is an activity, not a one-off technical implementation.
Key Factors That Influence Cyber Security Implementation Cost
The cost of cyber security is determined by the extent to which it requires integration into infrastructure, the level of complexity of the threat environment, and the number of systems that need to be monitored and managed in real time. A detailed perspective of the key cost drivers is presented below.
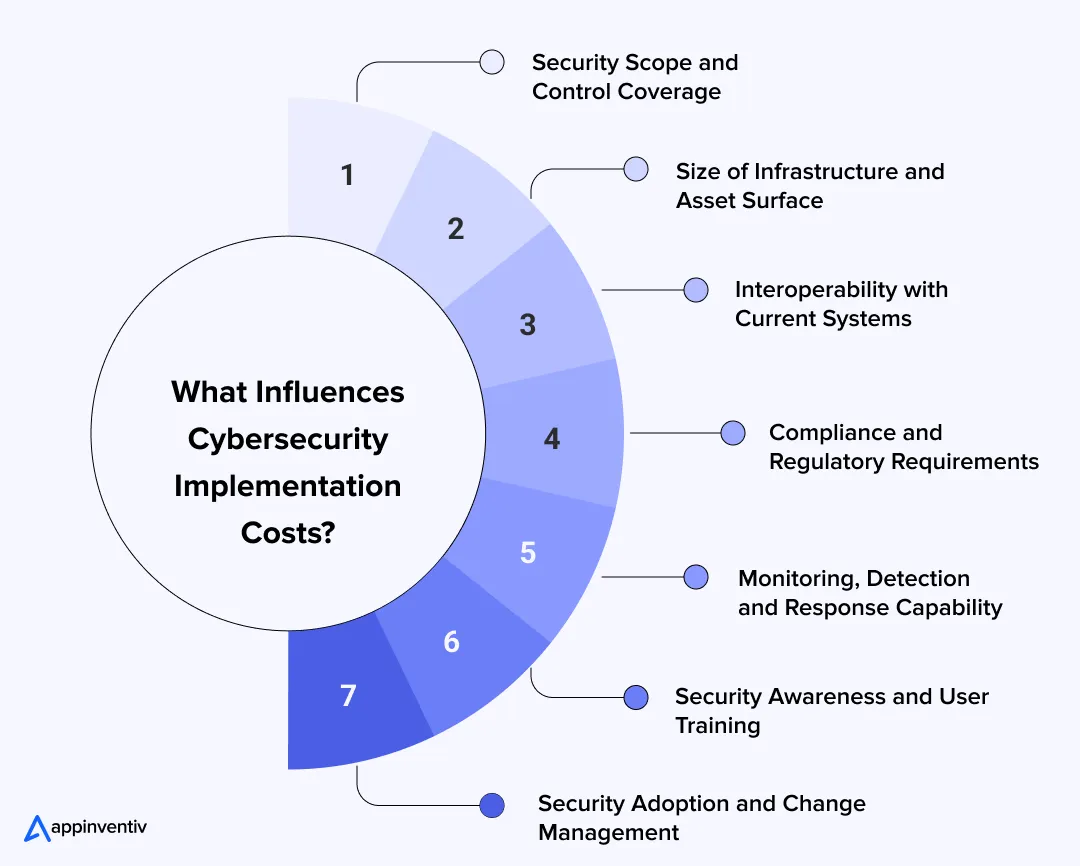
1. Security Scope and Control Coverage
The level of implementation effort is determined by the number of layers of security implemented in endpoints, network identities and cloud systems. It is usually where organizations begin by asking themselves how much does cyber security cost but the scope depth is rapidly varying.
- Simple configuration (antivirus, firewall, simple endpoint protection): $50,000 to $120,000.
- Mid-level controls (IAM, endpoint detection, network security): 120,000-300,000.
- Elaborate controls (zero trust, SIEM, cloud security, threat intelligence): $300,000 and above.
One of the significant drivers of costs is scope expansion. The cost of adding new systems or extending coverage during the project can add 25-40% to the overall cost.
2. Size of Infrastructure and Asset Surface
Implementation and monitoring effort is directly dependent on the number of users, devices, applications and cloud workloads. This is where the average cost of cyber security services starts to have a broad variance among organisations of equal size with varying architectures.
- Small environment (limited endpoints and users): $20,000 – $80,000.
- Mid-scale infrastructure (several systems and departments): $80,000 – $250,000.
- Enterprise surface, large (distributed systems, multi-cloud): $250,000 to $600,000 and above.
Costs scale non-linearly. Monitoring complexity and alert management overhead increase many times with the growth of asset volume.
3. Interoperability with Current Systems
The enterprise application security systems need to be integrated with the current IT infrastructure, such as legacy applications, cloud environments and third-party services. The fragmentation of the modernity of the current stack is one of the most important factors that determines the cost of cyber security solutions.
- Simple integration (standard APIs, small systems): $10,000 – $30,000.
- Moderate (integration, log aggregation, IAM connection): $30,000 – $90,000.
- Complex integration (legacy systems, custom connectors, multi-cloud): $90,000 – $200,000 or more.
Delay in integration is usual. Normalization of the log, compatibility, and testing cycles tends to increase time and cost.
4. Compliance and Regulatory Requirements
Security programs should be in line with industry regulations and data protection standards prior to implementation. Much of the cyber security audit cost is pegged on validation, documentation and certification preparedness.
- Basic compliance configuration (baseline policies, access controls): $10,000 – $30,000.
- Regulated environment (GDPR, HIPAA, SOC 2 alignment): $30,000 – $80,000
- High compliance (Multi-region, audit-intensive environments): $80,000- $200,000+
Compliance is ongoing. It is generally a 15-30 percent contributor to the overall cybersecurity expenses because of auditing, reporting, and ongoing validation.
5. Monitoring, Detection and Response Capability
Real-time tracking and incident response characterize the power of a security system and are among the highest ongoing costs. It is also in this context that the cyber security risk assessment cost tends to rise over time as a result of constant assessment and readiness to respond.
- Basic monitoring (log tracking, alert setup): $15,000 – $50,000
- Managed detection (SIEM, alert correlation, partial automation): $50,000 – $150,000.
- Basic SOC operations (24/7, SOAR, threat intelligence): $150,000- $500,000+/year.
There is an increase in operational costs. It needs to be staffed, tuned and incidents handled to provide continuous monitoring.
6. Security Awareness and User Training
The role of human factors is extremely important in security effectiveness. Training will make sure that users engage in safe practices and react appropriately to threats, which has a direct impact on the cyber security cost in the long run.
- Basic awareness training (policy introduction, basic modules): $5,000 – $15,000.
- Formal education (programs, role plays): $15,000 – $40,000.
- Programs on an enterprise-wide level (continuous training, rollout across multiple locations): $40,000- $100,000+.
Lack of awareness exacerbates risk. Human error security incidents tend to cause greater remediation and recovery expenses.
7. Security Adoption and Change Management
Implementation of security alters the way in which teams get access to systems and the handling of data. This transition is crucial to manage in order to prevent disruption and limit the overall cyber security services cost.
- Simple change management (communication, preliminary rollout): $5,000- $20,000.
- Organized implementation (rollout, feedback): $20,000- $50,000.
- Company-wide change (coordination of multiple teams, constant support): $50,000- $120,000+.
Adoption has a direct influence on ROI. Resistance or misalignment may cause a long timeline, reconfiguration, and higher operational costs.
Enterprise TCO: A Realistic View of Cyber Security Cost
Enterprise cyber security cost cannot be considered as a one-time investment. It is based on a total cost of ownership model where the initial implementation is just a small portion of the expenditure in the long term. The cost of infrastructure growth, constant monitoring, compliance, and talent is slowly gaining the top positions.
In the case of most organizations, to see how budgets change over time, it is essential to get a clear picture of the initial investment and current cyber security services pricing, depending on the maturity of operations.
Total Cost of Ownership Components
Enterprise cyber security TCO is distributed across multiple layers:
| Cost Element | Scope | Cost Contribution |
|---|---|---|
| Preliminary Implementation | Tools, architecture configuration, deployment | 25% -35% |
| Security Operations (SOC) | Incident response, monitoring, alerting | 20% -30% |
| Infrastructure and Cloud security | Hosting, scaling, workload protection | 10% -20% |
| Compliance & Audits | Certifications, reporting, governance | 10% -15% |
| Maintenance & Optimization | Patching, tuning, updates | 10% – 15% |
| Training & Awareness | Training of employees, simulations | 5% -10% |
Although the initial build seems important, operation and constant improvement are the key factors that determine the cyber security services cost in the long term.
CapEx vs OpEx in Cyber Security
One feasible method of measuring TCO is to divide expenditure into capital and operation expenditure.
CapEx (Initiating or Upfront Expenses)
- Security rights and licenses
- Infrastructure setup
- Implementation and integration
- Initial compliance setup
Estimated range: $100,000 – $800,000+
OpEx (Annual Costs)
- SOC monitoring and activities
- Incident response and threat intelligence
- Cloud security management
- Audits and compliance renewals
Estimated range: $150,000 – $1,000,000+ annually
The operating expenses generally surpass the initial expenditure over a 3 5 year span, but they have a great influence on the overall cost of cyber security.
3-Year Enterprise Cyber Security TCO Example
| Year | Cost Type | Estimated Spend |
|---|---|---|
| Year 1 | Implementation + Operations | $300,000 – $900,000 |
| Year 2 | Operations + Optimization | $200,000 – $700,000 |
| Year 3 | Operations + Scaling | $250,000 – $800,000 |
Total 3-Year TCO: $750,000 – $2,400,000+
This difference indicates the disparity in the size of infrastructure, regulation exposure, and maturity of monitoring.
See how we help you manage and optimize enterprise TCO.
ROI Breakdown of Cyber Security Investment
Cyber security ROI is not achieved by means of direct revenue generation. It is quantified in terms of loss prevention, continuity of operations and the mitigation of financial and regulatory risk. Plan ROI breakdown helps quantify where the investment delivers value over time.
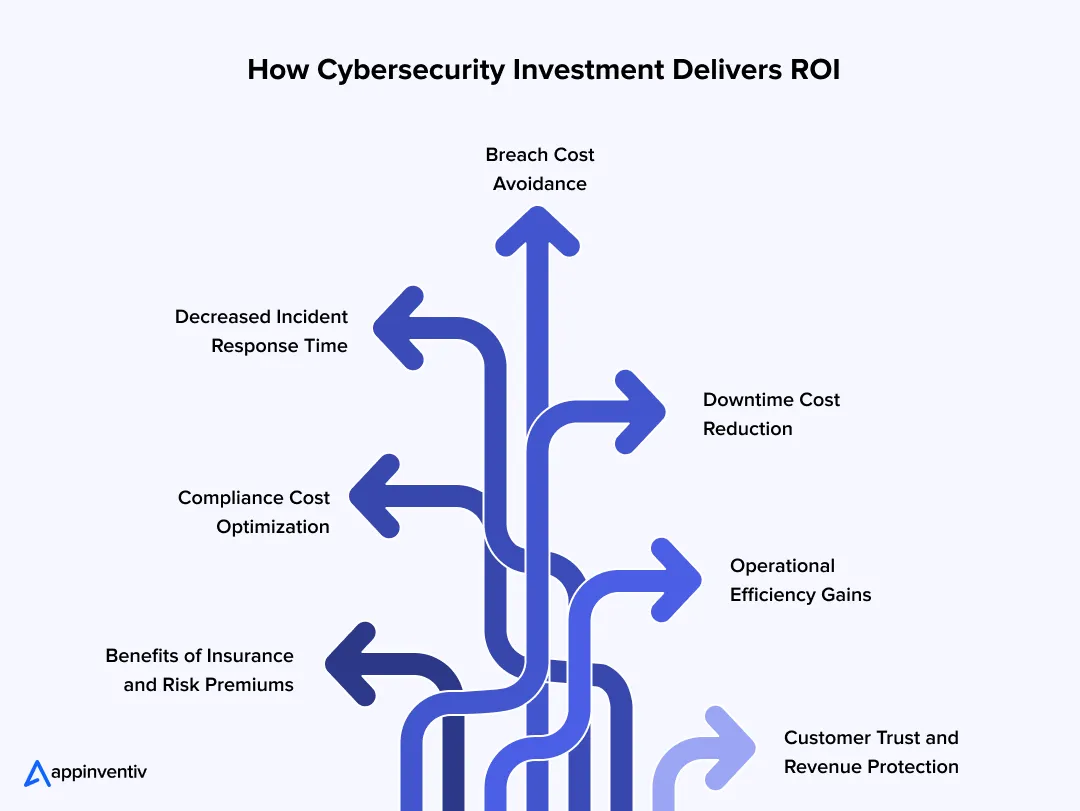
Breach Cost Avoidance
The first payback is avoiding security incidents that are usually the costliest events that an enterprise can incur. When evaluating how much does cyber security costs, this is the benchmark most organizations use for comparison.
- Average cost of cyber security breaches: $1M-5M and above
- Probability reduction with mature security: 40% 60% annually
Estimated ROI impact: Preventing even one breach can pay off several years of the overall cyber security expenses and defend financial and reputation assets.
Decreased Incident Response Time
Quick detection and reaction shortens the magnitude and duration of attacks. Monitoring equipment, SOC activities, and automation investments directly affect cybersecurity costs by changing expenditures on recovery to defensive measures.
- Without structured monitoring: 100–200+ hours to detect incidents
- With SOC and automation: 10–40 hours
Estimated ROI impact: The decrease in response time will reduce the area of harm, minimize recovery costs, and facilitate a quicker recovery to regular operations.
Downtime Cost Reduction
Security attacks usually interfere with systems, putting business operations on hold and revenue streams at risk. The average cost of cyber security services is justifiable on average in terms of their effectiveness in averting such downtime scenarios.
- Typical downtime expenses: 5,000 -50,000 per hour (depends on industry)
- Strong control reduction: 30% -70%
Estimated ROI impact: The availability of the improved systems will avoid loss of revenue and continuity of operations in the most important business functions.
Compliance Cost Optimization
Compliance with regulations is a mandatory and cost center. Early investment in structured controls incurs lower cybersecurity risk assessment costs in the long term through the reduction of repeated audits, rework, and penalties.
- Regulatory penalties avoided: $50,000 – $500,000+
- Reduction in cost of audit preparation: 20%-40%
Estimated ROI impact: Compliance posture reduces legal exposure and streamlines the audit process, reducing overheads.
Operational Efficiency Gains
Automation and centralized monitoring enhance team productivity and reduce reliance on manual processes. Although the cyber security services cost might be high in the short term, this is evened out by the efficiency in operations.
- Lessening of manual security activities: 25%-50%
- Better team performance and response accuracy
Estimated ROI impact: Better use of resources reduces staffing strain and enables teams to focus on high-value security actions.
Benefits of Insurance and Risk Premiums
Insurers regard organizations that have stable security systems as less risky. This has a direct effect on the premiums and coverage terms, which are usually pegged to the general cost of cybersecurity posture.
- Premium reduction: 10% – 30%
- Reduced probability of claims and better coverage conditions
Estimated ROI impact: Less insurance premiums and greater financial security in the face of major incidents.
Customer Trust and Revenue Protection
The security posture has a direct impact on customer confidence, particularly in sectors that deal with sensitive information. In the long run, cyber security cost will help in sustaining trust and loss of revenue caused by breaches or exposure of data.
- Less churn because of security attacks
- Greater retention in security sensitive areas (finance, healthcare)
Estimated ROI impact: With such strong security, credibility is established, brand value is safeguarded, and long-term customer retention is secured.
Hidden Costs of Cybersecurity Implementation
Cybersecurity budgets typically cover tools and deployment, yet a range of expenses becomes evident later in operations. They are not usually picked up in the beginning planning and develop with size and experience.
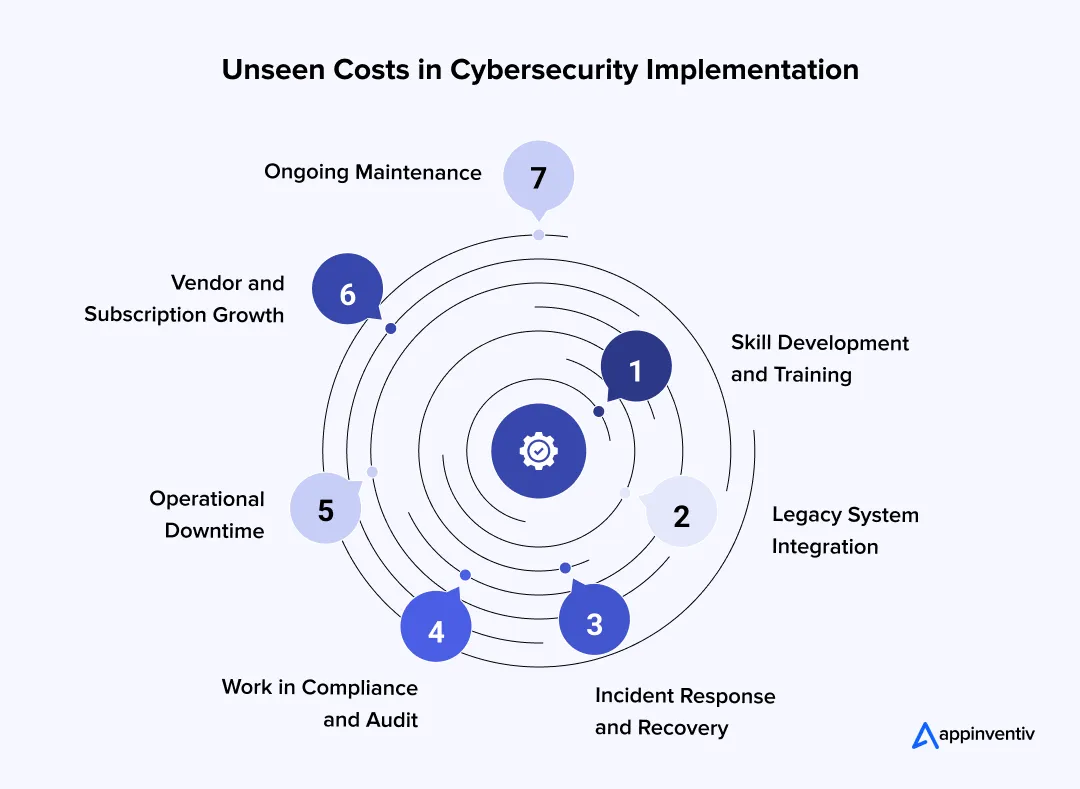
Skill Development and Training: Security equipment needs manpower. Teams must be upskilled continuously because platforms, threats, and compliance rules evolve. There is an external certification and workshops, which provide recurring costs.
Legacy System Integration: Older systems can hardly fit well with the contemporary security stacks. Bespoke integration, problem-solving patches and long-term testing drive more effort and budget than originally planned. Legacy system modernization, thus, adds to the overall costs.
Incident Response and Recovery: Handling of a breach includes the forensic examination, containment, system recovery, and legal assistance. These expenses are uncertain as well as costly in times of severe accidents.
Work in Compliance and Audit: Regulatory provisions require continuous audits, documents, and reporting. This can be costly; sometimes external consultants and internal resources are necessary.
Operational Downtime: Systems can be temporarily disrupted by security rollouts. Even a small downtime affects the revenue in sectors such as finance, retail, and logistics.
Vendor and Subscription Growth: The security ecosystem includes several vendors. The cost increases over time due to renewals, scaling usage, and other service layers.
Ongoing Maintenance: The operational cost remains constant with the size of the system due to continuous monitoring, patching, updating of rules, and managing logs.
Ways to Optimize Cybersecurity Costs
When risk is matched with investment, every system is simplified, and the security work is integrated into daily operations, making managing cybersecurity spending easy. It is aimed at eliminating inefficiency without compromising protection.
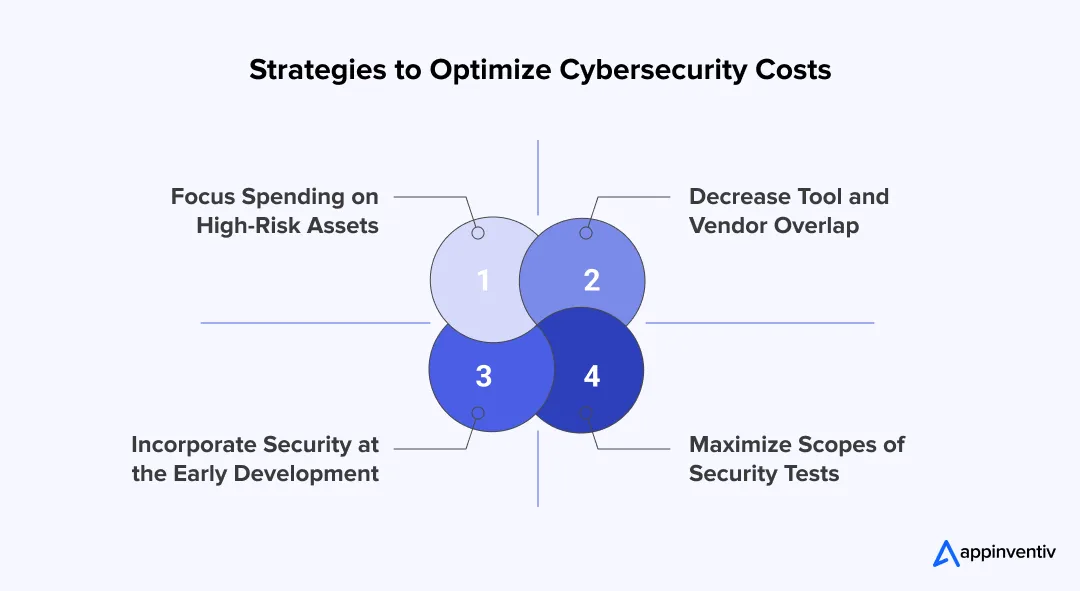
Focus Spending on High-Risk Assets
Budget should be allocated according to business risk and not equally. Systems like payment infrastructure and customer databases are more critical and require more controls, whereas less critical environments can be more lightly protected. This approach improves efficiency in cyber security services cost planning by avoiding unnecessary overinvestment.
Decrease Tool and Vendor Overlap
Most organizations end up having numerous security tools that can perform the same tasks. Integration of these systems minimizes duplication of licensing, integration effort and training. It also introduces enhanced management of the total cost of cyber security solutions.
Incorporate Security at the Early Development
Design and development-based security is much less expensive than post-deployment problems. Identification of vulnerabilities earlier saves on rework, exposure and enhances cost efficiency in the long term across systems.
Maximize Scopes of Security Tests
Security assessments ought to be risk-based and accurate, as opposed to being too general. Clear scope assists in managing effort and enhances the budgeting precision of the cyber security risk assessment cost, thus making the assessments practical and cost-efficient.
Get expert guidance to optimize your security investment.
Turn Cybersecurity into a Strategic Investment with Appinventiv
Cybersecurity is not a project but an investment that evolves in response to risk, complexity and regulation. Technological advancement, growth and complexity require enhanced controls, rapid response and monitoring. That’s where a structured approach by a security partner such as Appinventiv can help. Rather than piecemeal solutions and responsive patches, we begin to establish a security posture that grows with the company.
Our cyber security services are a combination of assessment, engineering and operational approach that makes security scalable, measurable, and aligned with real business risk.
For instance, we helped secure a marketplace developed with AI tools where poor defaults and weak controls were deployed, resulting in a breach. The consequences were serious, including data being exposed, requiring a shutdown and damaging trust.
Our experts performed a forensic investigation, re-engineered the system to adopt the zero-trust approach, enhanced payment processing and data security, and added real-time monitoring with automated threat detection and mitigation.
The results were clear. The system was back and protected. Post-relaunch, the number of users grew past 13,400, GMV (gross merchandise value) grew from $38K to over $214K per month, and ratings improved from 1.8 to 4.6. This example demonstrates that by doing cybersecurity right, you not only lower risk but also turn things around and regain confidence.
Reach out to a reliable cybersecurity consulting company like ours to make the smartest cybersecurity investment decisions. We will help you manage risks, prioritize security needs, and develop a cost-effective roadmap for cybersecurity in line with your business objectives.
FAQs
Q. What are the top cyber security services pricing models?
A. Here are some of the top cyber security pricing models:
- Fixed price model: Scope of work with a fixed price for services or projects
- Monthly/annual subscription: Regular payment for monitoring and support
- Pay-as-you-go model: Per-use, incident-based, or hourly charges
- Retainer model: Upfront payment for a block of hours or services for ongoing security support
- Enterprise model: Unique cyber security pricing model for large enterprises, risk and compliance
Q. How much does cyber security implementation cost?
A. The cyber security services cost for implementation varies by scale and complexity. Basic setups typically range from $50,000 to $150,000, while mid-level programs fall between $150,000 and $400,000. More complex setups with real-time monitoring and compliance controls range from $400,000 to $900,000+ and enterprise ecosystems are often $900,000 to $2,000,000+.
Q. How much should organizations allocate for cybersecurity?
A. Cybersecurity spending should be determined by risk, size of the IT infrastructure and regulatory requirements. Generally, firms allocate 5% to 12% of their total IT budget to security. Industries with high risk and regulatory compliance, like finance and healthcare, may spend more due to regulatory requirements and potential damages, while smaller companies will scale their cybersecurity budget according to their size and risk.
Q. What is the average cost of cybersecurity software for SMBs?
A. Cybersecurity software for SMBs typically ranges from $5,000 to $50,000 per year, depending on the number of users, endpoints and services needed. Basic tools such as antivirus and firewalls are on the lower end, with more complex offerings such as endpoint detection, identity and access management, and cloud security drive up the price.
Q. How much does it cost to hire a cybersecurity firm?
A. The cyber security services pricing for hiring a firm depends on service scope, expertise, and engagement model. Cyber security audit cost typically range from $100 to $200, project-based services range from $20,000 to $200,000+. Managed services or Security Operations Centers (SOCs) can cost between $5,000 to $50,000 monthly, based on the level of monitoring and response.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.
Security for AI: Protecting Your Innovation in the Era of Intelligent Attacks
Key takeaways: AI security now covers models, prompts, data pipelines, agents, APIs, retrieval systems, and outputs. Prompt injection, data leakage, model theft, poisoned data, and unsafe agents are major enterprise risks. Secure AI starts early with threat modeling, access control, guardrails, vendor checks, and monitoring. RAG systems need permission-aware retrieval, so sensitive documents do not…

From Legacy Security to Zero Trust Architecture: Upgrading Enterprise Security in Australia
Key takeaways: Australian cybercrime now costs large businesses $202,700 per incident on average, making Zero Trust architecture a board-level financial imperative Zero Trust is a phased programme, not a product. Identity controls, microsegmentation, and ZTNA must be sequenced deliberately to avoid operational disruption. Full ZTA implementation in Australia ranges from AUD 70,000 to 700,000+, but…

Claude Mythos: The Hidden AI Security Risks in Enterprise Digital Transformation
Key takeaways: AI is expanding the attack surface inside workflows, not just infrastructure, making traditional security visibility incomplete. Claude Mythos highlights a shift where risk comes from model behavior, prompts, and integrations, not just system vulnerabilities. Most enterprise AI risks do not start as breaches, they begin as small gaps in prompts, access control, or…






































