- Why Vulnerability Assessment and Penetration Testing Must Move Beyond Annual Checklists
- Vulnerability Assessment vs Penetration Testing: What Actually Sets Them Apart
- The Enterprise VAPT Lifecycle: How Organizations Identify, Validate, and Reduce Real Risk
- Prioritization in Practice: How Enterprises Decide What to Fix First
- Common Enterprise Pitfalls That Undermine VAPT Effectiveness
- Metrics That Demonstrate Real Risk Reduction in VAPT
- How to Choose the Right VAPT Services Partner
- The Future of VAPT in Enterprise Security
- Why Partner with a Cyber Security Services Company Like Appinventiv
- FAQs
Key Takeaways
- Vulnerability assessment finds weaknesses. Penetration testing proves exploitability. You need both to understand real exposure.
- Annual testing isn’t enough. Enterprise environments change too fast for checklist-driven security.
- Severity scores don’t equal business risk. Prioritization must factor in exploitability, exposure, and impact.
- Security value comes from remediation, not reports. If findings aren’t fixed and retested, risk remains.
- Mature VAPT programs reduce attack paths over time. The goal isn’t more findings, it’s less exploitable surface.
Most security failures don’t start with something dramatic. They start quietly. A server that wasn’t patched. An API was left exposed longer than it should have been. A permission setting that made sense six months ago but no longer does. Enterprises today operate across cloud platforms, mobile apps, SaaS tools, remote endpoints, and partner integrations. It’s a lot to manage. Without a disciplined way to test those environments, gaps stay invisible until someone exploits them. That’s where vulnerability assessment with penetration testing comes in, not as compliance paperwork, but as a practical way to see your organization the way an attacker would.
There’s still confusion around vulnerability assessment vs penetration testing, and that confusion often leads to underestimating risk. A vulnerability assessment tells you what’s potentially weak. A penetration test shows you how those weaknesses could be chained together to cause real impact. The difference between vulnerability assessment and penetration testing (VAPT) isn’t just technical detail. It determines how seriously findings are treated, how quickly teams act, and how leadership understands exposure.
The pressure is only increasing. Cyber risk is no longer limited to isolated IT functions. It now intersects with broader cyber risk management strategies that influence governance, compliance, and operational resilience across the enterprise. According to the Allianz Risk Barometer 2026, cyber incidents remain the number one global business risk, cited by 42% of respondents, ahead of supply chain disruption and natural catastrophes. That tells you something important. Security risk is no longer an IT issue sitting in the background. It is a boardroom concern.
In this guide, you’ll read how enterprises approach vulnerability assessment and penetration testing services in a structured way, how they identify weaknesses across complex environments, how they prioritize what truly matters, and how they fix security gaps before they turn into expensive, public incidents.
Get a structured vulnerability assessment and penetration testing strategy that reveals real exposure across cloud, apps, and infrastructure before it becomes a breach.
Why Vulnerability Assessment and Penetration Testing Must Move Beyond Annual Checklists
In many companies, vulnerability assessment with penetration testing follows a familiar routine. The engagement is booked months ahead. Teams prepare documentation and testing runs. A report is delivered, and meetings are held. Some issues are fixed quickly, others are deferred, and eventually, attention shifts back to product deadlines and operational targets.
No one ignores security on purpose. The process feels responsible. The challenge is that the environment being tested does not remain static long enough for that model to remain effective.
Think about how often your infrastructure changes in a typical month. A new cloud environment is created for a campaign. An API is opened for a partner. Permissions are adjusted to allow a team to move faster. A quick configuration tweak goes live to solve a performance issue. None of those changes wait for the next scheduled assessment. By the time a yearly review finishes, parts of the landscape it evaluated may already look different.
This is why a compliance-driven approach struggles to keep up. The answer is not simply to test more often. The answer is to treat pen testing and vulnerability assessment as part of broader cybersecurity measures for businesses that move with the organization instead of trailing behind it.
In practical terms, that shift means a few things:
- Infrastructure is assumed to change constantly, so visibility is maintained continuously rather than captured once a year.
- Findings are judged by their impact on revenue, data, and operations, not just by technical severity scores.
- Automated scanning provides coverage, but structured penetration testing vulnerability assessment confirms which weaknesses could realistically be exploited.
- Regulatory testing requirements are incorporated into broader vulnerability assessment & penetration testing services that guide ongoing decisions.
- Success is defined by fewer realistic attack paths over time, not just by a completed report.
When leaders understand the difference between vulnerability assessment and penetration testing, they stop focusing on whether the organization “passed” an engagement. The more useful question becomes whether exposure has actually decreased since the last cycle. That shift in thinking is what turns testing from a scheduled activity into a meaningful layer of protection.
Vulnerability Assessment vs Penetration Testing: What Actually Sets Them Apart
In many enterprise discussions, VAPT is used as if they mean the same thing. They don’t, and they answer two very different questions.
A vulnerability assessment asks: What weaknesses exist across our systems? A penetration test asks: Can someone actually exploit those weaknesses to get access or cause damage?
Both are necessary. One gives visibility across a large environment. The other proves whether those weaknesses can realistically turn into an attack.
For security leaders, understanding the distinction helps determine where to invest effort. Scanning alone creates awareness. Penetration testing brings clarity about real risk.
| Aspect | Vulnerability Assessment | Penetration Testing |
|---|---|---|
| Main Purpose | Discover security weaknesses across infrastructure, applications, and networks | Attempt to exploit those weaknesses the way an attacker would |
| Testing Style | Mostly automated scanning supported by configuration checks | Manual, hands-on testing performed by experienced security professionals |
| Scope | Wide coverage across many systems and environments | Narrower focus on critical systems or high-risk attack paths |
| Testing Depth | Identifies potential vulnerabilities based on known patterns | Demonstrates how those vulnerabilities can be abused in practice |
| Frequency | Often continuous or scheduled weekly/monthly | Conducted periodically or after major releases or infrastructure changes |
| Typical Output | List of vulnerabilities with severity ratings and affected assets | Detailed report showing attack paths, proof-of-concept exploits, and impact |
| Risk Insight | Highlights potential weaknesses across the environment | Shows which weaknesses can realistically lead to compromise |
| Tools Commonly Used | Network scanners, dependency scanners, and configuration analysis tools | Exploitation frameworks, custom scripts, and manual attack techniques |
| Operational Value | Maintains ongoing visibility into the organization’s attack surface | Helps security teams prioritize what truly needs urgent remediation |
When both approaches are used together, the picture becomes much clearer. Vulnerability assessments show the size of the problem. Penetration testing reveals which doors actually open.
That combination is what makes a VAPT program useful for enterprise security. It moves the conversation away from raw vulnerability counts and toward something that matters more: real exposure.
The Enterprise VAPT Lifecycle: How Organizations Identify, Validate, and Reduce Real Risk
When done properly, vulnerability assessment with penetration testing is not a single activity. It’s a structured lifecycle. Mature enterprises don’t just “run scans” and hope for the best. They build a repeatable system that connects discovery, validation, prioritization, remediation, and verification into one continuous loop.
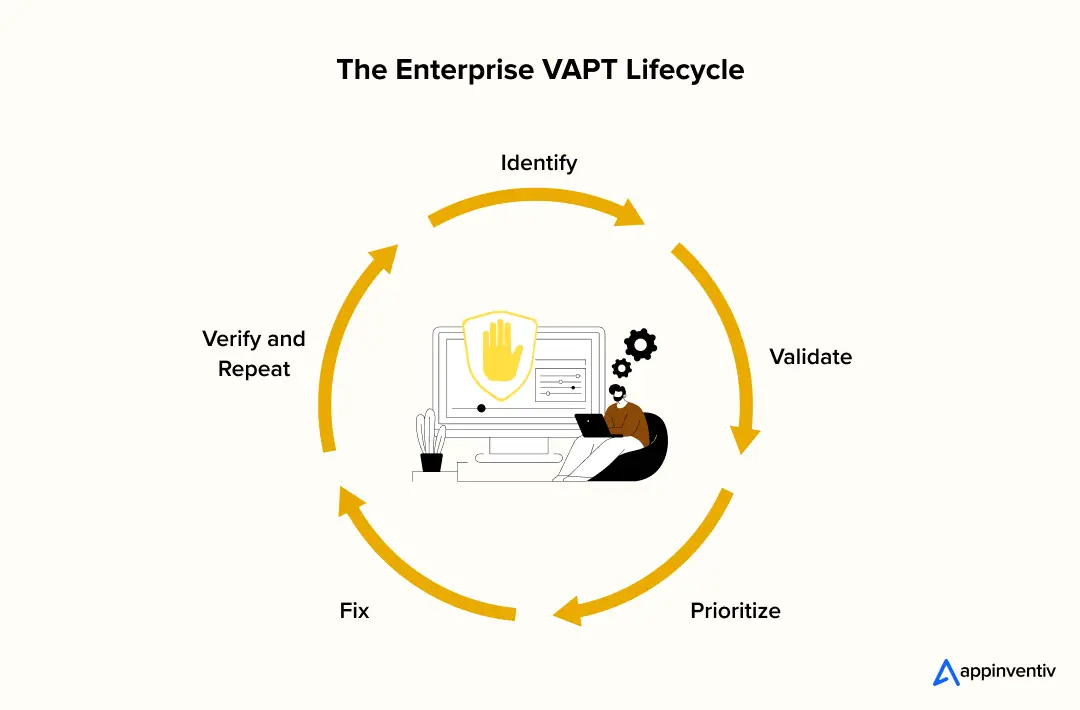
1. Identify: Build Real Visibility Before You Test Anything
Before running any scanner, the first question is simple: Do we even know what we own?
In most enterprises, the attack surface is larger than expected. Shadow SaaS accounts, forgotten staging servers, legacy APIs still reachable from the internet, and over-permissioned service accounts are common realities.
A strong vulnerability assessment program begins with:
- Authoritative asset inventory
- On-prem infrastructure (servers, network devices, databases)
- Cloud accounts (AWS, Azure, GCP subscriptions and roles)
- Containers and Kubernetes clusters
- Internet-facing APIs and subdomains
- Third-party integrations and vendor access paths
- Exposure mapping
- Identifying externally accessible assets
- Enumerating open ports and services
- DNS and subdomain discovery
- API endpoint discovery
- Configuration and identity review
- IAM role overprivileging
- Misconfigured storage buckets
- Excessive admin access
- Service account sprawl
This is where vulnerability assessment tools play a critical role. Automated scanners analyze infrastructure for known CVEs, outdated libraries, insecure protocols, and misconfigurations. But without an accurate asset context, even the best tools produce incomplete results.
At this stage, you are not exploiting anything. You are building clarity.
2. Validate: Move From Theoretical Weakness to Real Exploitability
This is where vulnerability assessment vs penetration testing becomes meaningful. A vulnerability assessment identifies weaknesses. A penetration test attempts to exploit them.
For example:
- A scan may reveal an outdated library with a CVSS rating of 9.0.
- A penetration test will determine whether that library is reachable, exploitable, and whether it can be chained with another flaw to escalate privileges.
In enterprise environments, validation often includes:
Exploit chaining
- Low-privilege access → misconfigured IAM → lateral movement → data access
Privilege escalation analysis
- Local privilege escalation paths
- Token theft or session hijacking
Business logic abuse
- Manipulating workflows in financial or healthcare applications
- Bypassing rate limits in APIs
Cloud attack path simulation
- Compromised instance → metadata service access → role takeover
This is where the difference between vulnerability assessment and penetration testing becomes operationally clear. One lists possible entry points. The other tests whether those entry points lead anywhere meaningful.
Without validation, organizations waste time fixing issues that are technically severe but practically irrelevant.
3. Prioritize: Risk Is More Than a CVSS Score
Here’s where many programs struggle. Most reports rank findings by CVSS. But CVSS measures technical severity, not business urgency.
A mature VAPT integrates multiple signals
before assigning remediation priority:
Exploitability
- Is the vulnerability being actively exploited?
- Does public exploit code exist?
Exposure
- Internet-facing or internal?
- Behind authentication?
Business impact
- Does it touch regulated data, particularly in sectors such as cybersecurity in healthcare, where data exposure can trigger severe compliance consequences?
- Does it impact revenue systems?
Compensating controls
- WAF protection
- Network segmentation
- Monitoring in place
For example:
- A medium-severity flaw in an internet-facing payment API may demand faster remediation than a critical flaw in an isolated internal lab server, especially in cybersecurity in banking environments where financial exposure is immediate.
This is why understanding the difference between penetration testing vs vulnerability assessment is crucial. Penetration testing adds context that helps prioritize intelligently instead of mechanically.
4. Fix: Remediation is Where Programs Succeed or Fail
Security testing has value only if findings are fixed. Enterprises that treat remediation as an afterthought often accumulate what’s known as “security debt.” Reports get archived. Tickets get delayed, and the risk quietly grows.
Effective vulnerability assessment & pen testing vapt programs integrate directly into engineering workflows:
- Structured remediation intake
- Findings converted into actionable tickets
- Clear ownership assigned
- Business risk context included
- SLA-driven remediation
- Critical internet-facing issues: days, not months
- Internal high-risk issues: defined timelines
- Executive visibility for overdue items
- Engineering alignment
- Integration with Jira, ServiceNow, or DevOps boards
- CI/CD checks to prevent reintroducing fixed flaws
- Regression validation testing
This is also where high-quality documentation of vulnerability assessments, including penetration testing reports, matters. Reports must provide reproducible steps, proof-of-concept evidence, and clear remediation guidance, not just screenshots and severity labels.
5. Verify and Repeat: Security Is a Loop, Not a Line
Once patches are applied, the job is not done.
Retesting ensures:
- The vulnerability is fully resolved.
- No side effects introduced new weaknesses.
- Exploit paths are truly closed.
Over time, organizations measure:
- Mean time to remediate
- Recurring vulnerability patterns
- Teams with repeated configuration drift
- Reduction in exploitable attack paths
This is how web application vulnerability assessment with penetration testing has matured from periodic testing into continuous exposure reduction.
When enterprises internalize the full lifecycle of pen testing and vulnerability assessment, the conversation shifts. It’s no longer about “passing the test.” It becomes about shrinking the real, exploitable surface that attackers can use.
Implement VAPT services that integrate with engineering workflows and, over time, reduce exploitable attack paths.
Prioritization in Practice: How Enterprises Decide What to Fix First
If there’s one place where VAPT programs either succeed or quietly fail, it’s prioritization.
Most organizations don’t suffer from a lack of findings. They suffer from too many of them.
After a full vulnerability assessment & pen testing VAPT cycle, it’s common to see hundreds or even thousands of entries in a report. Some are genuinely dangerous. Some are edge cases. Some will never be exploited in the real world. The challenge isn’t finding issues. It’s deciding what truly deserves immediate attention.
This is where the conversation around vulnerability assessment vs penetration testing becomes practical rather than theoretical.
1. Why Severity Alone Is Not Enough
Many teams still rely heavily on CVSS scores. A vulnerability labeled “critical” automatically jumps to the top of the queue. But experienced security leaders know this approach is incomplete.
Consider this:
- A critical vulnerability on an internal development server with no external exposure.
- A medium-severity authentication bypass on a public-facing customer portal.
Technically, the first issue may score higher. Operationally, the second one could be far more damaging.
That’s why understanding the difference between vulnerability assessment and penetration testing matters at the prioritization stage. A vulnerability assessment highlights theoretical weaknesses. Penetration testing reveals whether those weaknesses can actually be exploited in your environment.
2. How Mature Enterprises Prioritize Findings
A well-run VAPT service typically evaluates findings across multiple dimensions, not just severity.
Here’s what mature prioritization models include:
- Exploitability in the real world
- Is there public exploit code?
- Is it being actively weaponized?
- Can it be chained with other weaknesses?
- Exposure level
- Internet-facing vs internal
- Requires authentication or not
- Protected by segmentation or WAF?
- Asset criticality
- Revenue-generating systems
- Regulated data (financial, healthcare, personal data)
- Executive or privileged access systems
- Ease of lateral movement
- Can this issue help pivot into more sensitive environments?
- Does it provide privilege escalation potential?
This is where penetration testing vulnerability assessment becomes far more valuable than automated scanning alone. When exploit paths are demonstrated, leadership can see risk in concrete terms rather than abstract severity ratings.
3. Turning Risk Into Actionable SLAs
Prioritization should translate into time-bound decisions. Without that, findings linger.
Enterprises often map findings into SLA tiers, such as:
- Emergency remediation
- Actively exploitable
- Internet-facing
- High business impact
- High priority
- Privilege escalation potential
- Access to sensitive data
- Standard remediation
- Internal exposure
- Lower business criticality
This structured approach reduces internal debate. It also ensures that VAPT services deliver measurable outcomes rather than static reports.
4. Bridging the Gap Between Security and Engineering
Another overlooked factor in prioritization is communication. Security teams often speak in terms of CVEs and exploit chains. Engineering teams speak in terms of deployment cycles, dependencies, and rollback risk. If those conversations are not aligned, even the best vulnerability assessment and penetration testing company will struggle to drive change.
Effective prioritization, therefore, includes:
- Clear technical proof of exploitability
- Business impact explanation in plain terms
- Practical remediation guidance
- Estimated effort for fixing the validation
That clarity reduces friction. It turns the differences between VAPT into action.
Why This Stage Determines Program Maturity
The difference between penetration testing and vulnerability assessment becomes most visible at this point. A vulnerability assessment may generate a long list. Penetration testing shows which of those entries are doors that actually open.
When prioritization is done right:
- Teams stop chasing low-risk noise.
- Leadership gains visibility into real exposure.
- Remediation cycles shorten.
- Security debt stops accumulating silently.
In the next section, we’ll move deeper into remediation execution, how enterprises fix vulnerabilities at scale without destabilizing production systems, and how they validate that risk has genuinely been reduced rather than temporarily suppressed.
Common Enterprise Pitfalls That Undermine VAPT Effectiveness
Most enterprises can confidently say they conduct vulnerability assessment with penetration testing. Calendars are blocked, and vendors are engaged. Reports are delivered. Yet when incidents occur, leadership is left asking the same question: How did we miss this?
The uncomfortable truth is that testing alone does not reduce risk, but execution does.
Below are the patterns that quietly weaken even well-funded VAPT service programs.
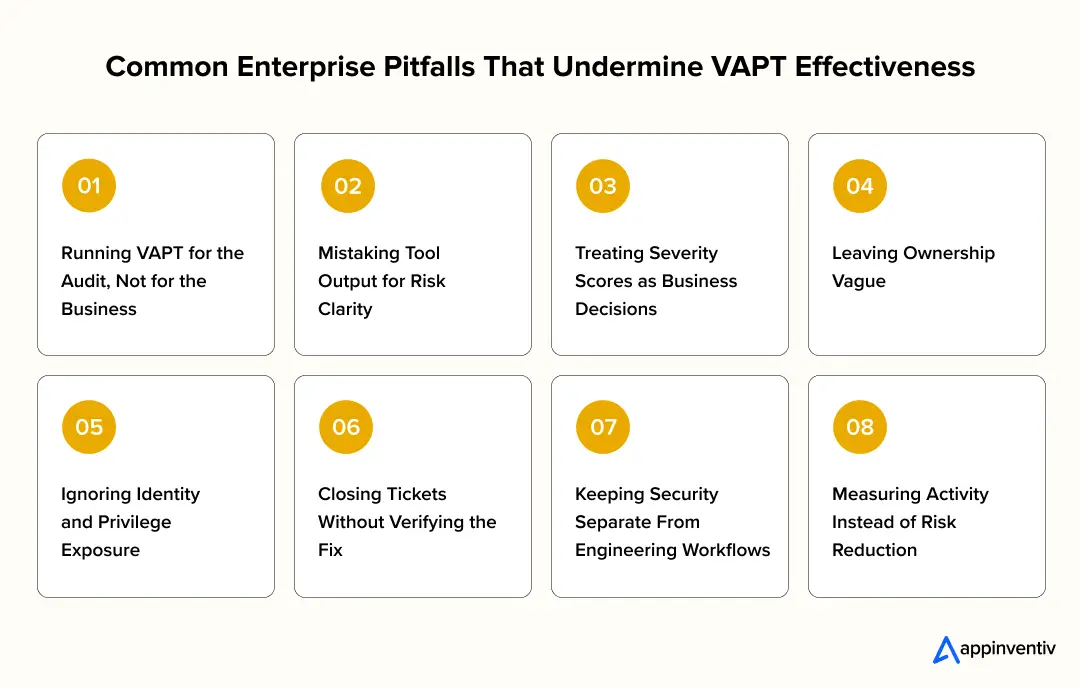
1. Running VAPT for the Audit, Not for the Business
This is more common than most leaders admit. When vulnerability assessment & pen testing VAPT is tied only to compliance deadlines:
- Testing becomes predictable.
- Scope stays narrow to avoid operational disruption.
- Remediation urgency drops once the audit window closes.
Security becomes a reporting function. Teams can technically claim they perform pen testing and vulnerability assessment, but the effort is disconnected from real-world exposure. Attackers, meanwhile, don’t work on annual cycles.
2. Mistaking Tool Output for Risk Clarity
Automated scanners are powerful. They’re fast, scalable, and consistent. But they are also blind to context.
A common failure pattern in vulnerability assessment penetration testing programs is assuming that a vulnerability list equals understanding.
What tools often miss:
- How two low-severity issues can be chained together.
- Whether a “critical” flaw is actually reachable.
- Business logic abuse in complex applications.
This is where the difference between vulnerability assessment & pen testing becomes practical. A vulnerability assessment identifies potential issues. Penetration testing shows what can actually be exploited.
Without that validation layer, teams spend energy on noise while real attack paths remain open.
3. Treating Severity Scores as Business Decisions
CVSS scores are useful. They standardize technical severity. But they don’t know your business.
A medium-rated vulnerability in an internet-facing payment system may pose a greater real risk than a critical issue buried in a non-production environment.
When organizations blur the difference between penetration testing and vulnerability assessment, they often default to sorting by severity alone. The result?
- Engineering teams patch what looks urgent on paper.
- Security teams struggle to justify why something “lower severity” needs faster attention.
- Exposure remains misaligned with effort.
Mature VAPT services integrate exploitability, exposure, and business criticality, not just technical scoring.
4. Leaving Ownership Vague
Security findings without clear owners tend to age. It’s not negligence, it’s organizational friction.
Infrastructure thinks it’s an application issue. Application teams think it’s DevOps. DevOps assumes security will handle it. Meanwhile, the vulnerability sits.
Even the most detailed vulnerability assessment & penetration report cannot compensate for unclear accountability.
Effective programs assign:
- Named system owners.
- Defined remediation timelines.
- Escalation paths for overdue issues.
Without this structure, VAPT becomes documentation, not defense.
5. Ignoring Identity and Privilege Exposure
Many programs still focus heavily on infrastructure vulnerabilities while underestimating identity risk.
But modern breaches often pivot through:
- Over-permissioned cloud roles.
- Stale administrative accounts.
- Service accounts with excessive privileges.
- Weak authentication enforcement.
If web application vulnerability assessment & penetration testing do not evaluate identity paths and privilege escalation, they miss how attackers actually move through networks today, particularly in cybersecurity in manufacturing environments where IT and operational systems converge.
6. Closing Tickets Without Verifying the Fix
Another quiet failure: assuming remediation equals resolution. Patches get deployed, tickets get closed. Dashboards turn green.
But without retesting:
- The vulnerability may still be partially exploitable.
- A configuration tweak may have reintroduced exposure.
- An exploit chain may remain intact through a different path.
The difference between vulnerability assessment & pen testing matters again here. Retesting ensures exploitability has truly been removed, not just administratively marked as resolved.
7. Keeping Security Separate From Engineering Workflows
If findings from a VAPT company arrive as static PDFs disconnected from Jira boards, sprint planning, and CI/CD pipelines, remediation becomes friction-heavy.
Security feels like an external auditor. Engineering sees findings as interruptions.
Effective vulnerability assessment & pen testing programs integrate directly into development workflows, making security part of delivery rather than an afterthought.
8. Measuring Activity Instead of Risk Reduction
This is perhaps the most subtle pitfall. Organizations celebrate:
- Number of vulnerabilities discovered.
- Number of scans completed.
- Volume of tickets created.
But those metrics measure motion, not progress. Real maturity shows up differently:
- Fewer exploitable paths over time.
- Shorter exposure windows.
- Reduced recurrence of the same misconfigurations.
- Faster response to internet-facing critical issues.
When enterprises internalize the true difference between vulnerability assessment and penetration testing, and treat both as parts of a disciplined lifecycle, these pitfalls become avoidable. Testing alone doesn’t protect an organization. How findings are interpreted, prioritized, and operationalized does.
In the next section, we’ll look at the metrics that prove whether your VAPT program is genuinely shrinking attack surface or simply producing more reports.
Also Read: Cost to Develop a Penetration Testing Tool Like Kali Linux
Metrics That Demonstrate Real Risk Reduction in VAPT
It’s easy to measure how much testing you’re doing. It’s harder to measure whether you’re actually safer.
Many organizations running vulnerability assessment & pen testing focus on the number of findings discovered or scans completed. Those metrics show activity. They don’t show exposure reduction.
If VAPT services are effective, the metrics should reflect reduced exploitability, faster remediation, and fewer viable attack paths, not just growing reports.
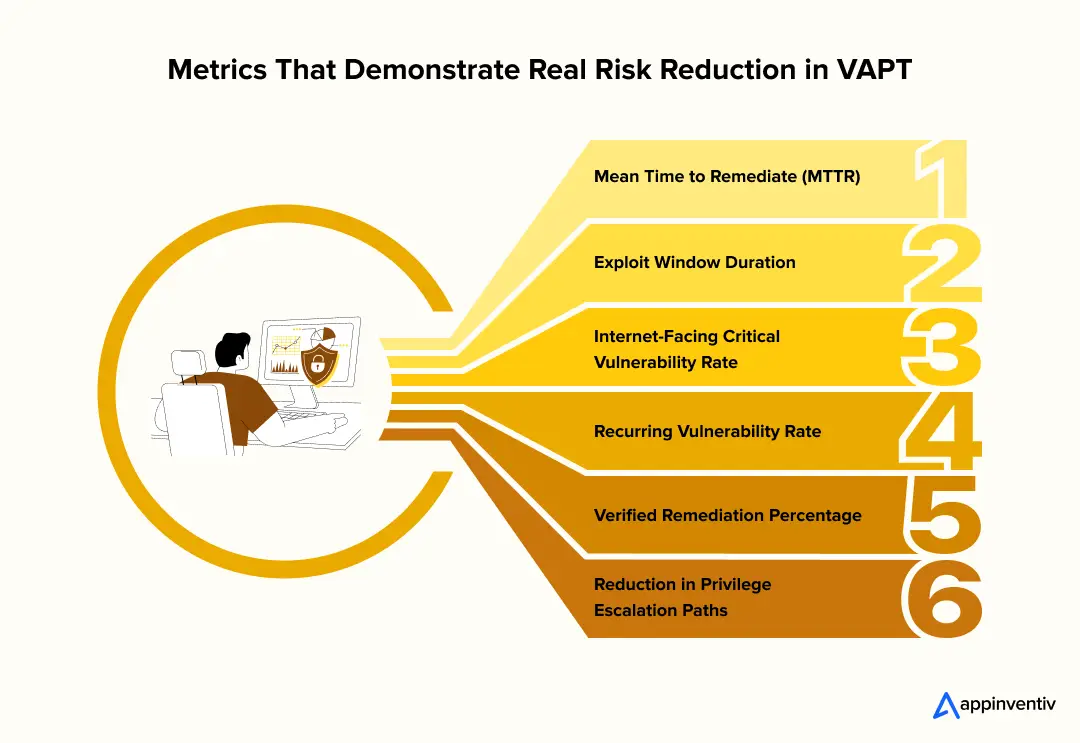
1. Mean Time to Remediate (MTTR)
MTTR measures how quickly critical vulnerabilities are resolved after they are discovered.
A mature pen testing and vulnerability assessment program will:
- Define SLAs by severity and exposure
- Track remediation timelines consistently
- Escalate overdue high-risk findings
A decreasing MTTR signals operational discipline. An increasing MTTR signals accumulating risk.
2. Exploit Window Duration
This metric captures the time between vulnerability discovery and verified closure.
It should include:
- Patch deployment
- Configuration updates
- Retesting validation
Understanding the difference between vulnerability assessment & pen testing is important here. Patching alone is not enough; validation confirms exploitability has been removed.
Shorter exploit windows mean fewer opportunities for attackers.
3. Internet-Facing Critical Vulnerability Rate
Tracking critical vulnerabilities on externally exposed systems provides direct insight into real attack surface risk. Strong vulnerability assessment & pen testing VAPT programs aim for:
- Rapid remediation of public-facing critical issues
- Consistent decline in high-risk exposure over time
A downward trend here reflects meaningful risk reduction.
4. Recurring Vulnerability Rate
Recurring findings indicate systemic weaknesses rather than isolated errors.
Monitoring recurrence helps identify:
- Incomplete root-cause fixes
- Configuration drift
- Weak development or deployment practices
Effective vulnerability assessment penetration testing programs reduce repetition by addressing process flaws, not just individual vulnerabilities.
5. Verified Remediation Percentage
This measures the percentage of findings that were retested and confirmed resolved.
It ensures that:
- Fixes are technically sound.
- Exploit paths are fully closed.
- Vulnerabilities are not administratively “closed” without validation.
The difference between penetration testing and vulnerability assessment becomes practical here; penetration testing verifies that the risk has genuinely been eliminated.
6. Reduction in Privilege Escalation Paths
Modern attacks often rely on chaining low-level access to higher privileges.
Tracking the reduction of:
- Lateral movement paths.
- Excessive IAM privileges.
- Over-permissioned service accounts.
is especially important in web application VAPT environments.
Fewer exploitable privilege paths directly translate into lower potential impact of a breach.
When these metrics consistently move in the right direction, VAPT services are doing what they are meant to do: reducing real exposure, not just generating documentation.
The goal is not to test more. It is to shrink risk measurably over time.
How to Choose the Right VAPT Services Partner
At some point, most enterprises face a practical decision: Do we build everything in-house, or do we engage a specialized vulnerability assessment and penetration testing company?
The answer depends on internal maturity, skill depth, regulatory requirements, and the environment’s complexity. But one thing is clear: the quality of your VAPT services partner directly impacts the effectiveness of your program.
Not all providers deliver the same depth, rigor, or business alignment.
Below is what enterprises should evaluate before selecting a VAPT service partner.
1. Do They Clearly Understand the Difference Between Vulnerability Assessment and Penetration Testing?
This sounds basic, but it matters. A credible partner should clearly explain:
- The difference between vulnerability assessment & pen testing
- When each is appropriate
- How do both complement each other
- How findings transition from discovery to exploit validation
If a vendor treats vulnerability assessment vs penetration testing as interchangeable, that’s a red flag. The value lies in how the two are structured together, not just bundled into a single acronym.
2. Depth of Technical Capability
Enterprise environments are not uniform. They include:
- Hybrid cloud architectures
- Containerized workloads
- API ecosystems
- Identity and access management systems
- CI/CD pipelines
Your provider should demonstrate experience in:
- Web application VAPT
- Cloud privilege escalation analysis
- API abuse testing
- Identity and access path exploitation
- Red team-style adversary simulations
Ask specifically about the tools used for vulnerability assessment & penetration testing, and more importantly, where manual testing complements automated tooling. Tools surface patterns. Skilled testers uncover logic flaws and exploit chains.
3. Reporting Quality and Business Context
A strong VAPT report should not feel like a scanner export.
It should include:
- Clear technical reproduction steps
- Proof-of-exploit evidence
- Business impact explanation
- Practical remediation guidance
- Risk prioritization context
If the report cannot be easily understood by engineering teams and summarized for executive leadership, it will slow remediation rather than accelerate it.
4. Integration With Your Operational Workflows
Security testing that operates in isolation often fails in execution.
An effective penetration testing vulnerability assessment provider should support:
- Integration into ticketing systems (Jira, ServiceNow, etc.)
- SLA-based tracking models
- Retesting validation processes
- Ongoing engagement models rather than one-off assessments
Testing should align with release cycles and DevOps velocity, not disrupt them unpredictably.
5. Methodology Transparency
Serious providers are transparent about:
- Testing scope
- Rules of engagement
- Exploit safety boundaries
- Data handling practices
- Retesting procedures
Ask how they approach the vulnerability assessment & penetration testing difference operationally. Do they validate exploit chains? Do they simulate lateral movement? Do they assess identity risks? Methodology clarity signals maturity.
6. Continuous Improvement Capability
Enterprise security is not static. Threat landscapes shift, and infrastructure evolves.
The right vulnerability assessment and penetration testing services partner should offer:
- Periodic reassessments
- Continuous exposure models
- Threat intelligence enrichment
- Program maturity recommendations
This moves the conversation from “Did we pass testing?” to “Are we improving each quarter?”
7. Alignment With Business Risk
Finally, testing must align with business priorities. A mature vulnerability assessment & penetration testing VAPT partner understands:
- Regulatory obligations
- Industry-specific risk profiles
- Operational uptime requirements
- Data sensitivity levels
They help translate technical findings into risk language that executives can act on. Choosing the right VAPT services partner is not just about vendor selection. It’s about building a long-term capability that continuously reduces exposure.
When the partnership is structured correctly, vulnerability assessment & penetration testing stop being reactive controls and become strategic risk-management assets.
The Future of VAPT in Enterprise Security
A few years ago, many companies treated enterprise vulnerability assessment and pen testing like a calendar event. Schedule it and run it. Review the report and repeat next year. That approach doesn’t hold up anymore.
Infrastructure changes too fast. Cloud resources spin up and down daily. APIs get exposed during product pushes. Development teams deploy multiple times a week. If testing only happens periodically, it’s always looking at yesterday’s environment.
That’s why enterprise vulnerability assessment and pen testing services are shifting from “projects” to ongoing capabilities.
What that shift looks like in practice:
- Continuous vulnerability visibility: Automated assessment runs regularly across cloud, applications, APIs, and identity systems to prevent blind spots from building up.
- Focused penetration testing where it matters most: Instead of testing everything superficially, enterprises pressure-test high-risk systems, critical APIs, and privileged access paths.
- Greater attention to identity and cloud risk: Over-permissioned roles, token misuse, and lateral movement are now central parts of modern vulnerability assessment & penetration testing VAPT efforts, especially in expanding cybersecurity in IoT deployments.
- Reporting that reflects exposure, not volume: Leadership conversations are moving away from “how many vulnerabilities did we find?” toward “how much have we reduced exploitable risk?”
The difference between vulnerability assessment and pen testing is becoming more practical in this model. Vulnerability assessment keeps the lights on across the environment. Penetration testing stress-tests the doors to see which ones actually open.
The future of pen testing and vulnerability assessment isn’t about running more tests. It is about integrating intelligence, including AI in cybersecurity initiatives, to anticipate exploit patterns before they are weaponized.
Partner with a cybersecurity services company that embeds vulnerability assessment and penetration testing into your operating model for long-term resilience.
Why Partner with a Cyber Security Services Company Like Appinventiv
Security testing should not feel disconnected from how your business builds and ships products. Too often, vulnerability assessment and pen testing are treated as external reviews that arrive, disrupt, and disappear. That model does not reduce risk in the long run. As a cybersecurity services company, Appinventiv treats security as part of the engineering lifecycle. We work alongside product, DevOps, and infrastructure teams so testing, validation, and remediation happen in sync with real delivery timelines.
Our experience comes from working across 35+ industries, each with different compliance pressures, architectures, and threat models. We have designed and delivered 3000+ solutions, many in complex enterprise environments where security could not be an afterthought. We have also transformed 500+ legacy processes, strengthening aging systems without disrupting business continuity. That exposure gives us practical insight into what actually works when implementing vulnerability assessment and pen testing services at scale.
If you are evaluating a long-term security partner, choose a cybersecurity services company that focuses on reducing exploitable risk rather than just producing reports. At Appinventiv, we help enterprises embed VAPT into their operating model so that exposure steadily declines over time. Let’s work together to strengthen your security posture before the next incident tests it.
FAQs
Q. What is vulnerability assessment and penetration testing (VAPT)?
A. At its core, vulnerability assessment and pen testing are about seeing your systems the way an attacker would. A vulnerability assessment scans your infrastructure, applications, and cloud environment for known weaknesses and misconfigurations. Penetration testing goes a step further; it attempts to exploit those weaknesses to understand the real impact.
When combined as a vulnerability assessment and pen testing process, it gives you two things: visibility and validation. One shows you what might be wrong. The other shows what could actually be abused.
Q. What is the difference between vulnerability assessment and penetration testing?
A. The difference between vulnerability assessment and pen testing is often misunderstood. A vulnerability assessment is broad. It identifies potential flaws at scale. Penetration testing is focused and hands-on. It tests whether those flaws can be chained together to obtain real access.
In simple terms, vulnerability assessment vs penetration testing is about potential versus proof. One flags weaknesses. The other proves exploitability.
Q. What is the difference between penetration testing vs vulnerability assessment in enterprise environments?
A. In large environments, the difference between pen testing and vulnerability assessment becomes more operational.
Vulnerability assessment runs continuously to maintain awareness across a changing infrastructure. Penetration testing targets high-risk systems, customer-facing applications, privileged access pathways, and sensitive data environments to simulate real-world attacks.
Understanding the difference between vulnerability assessment and penetration testing helps enterprises allocate resources where impact is highest.
Q. How often should enterprises conduct vulnerability VAPT services?
A. There’s no universal schedule, but annual testing alone is rarely enough. Most organizations run ongoing vulnerability assessments to maintain visibility and conduct penetration testing after major changes, new applications, cloud migrations, and infrastructure redesigns.
Effective vulnerability assessment and penetration testing services are tied to how often your environment changes, not just to compliance deadlines.
Q. What tools are used for vulnerability assessment and penetration testing?
A. There are many tools used for VAPT, including network scanners, web application testing platforms, cloud configuration analyzers, and exploitation frameworks.
But tools alone don’t guarantee protection. Strong VAPT tools must be paired with human expertise. Automated scans identify patterns. Skilled testers uncover logic flaws and hidden exploit paths.
Q. What does a vulnerability assessment and penetration testing report include?
A. A useful vulnerability assessment and pen testing report does more than list findings.
It should clearly explain:
- What was discovered
- Whether it was exploitable
- What business systems were affected
- How to remediate effectively
Without context and prioritization, even detailed reports can overwhelm teams rather than guide them.
Q. What is web application vulnerability assessment and penetration testing?
A. Web application VAPT focus on internet-facing systems, login flows, APIs, session management, access controls, and business logic.
Because these systems are directly exposed to external users, they are often prime targets. A structured penetration testing vulnerability assessment approach ensures that both automated scanning and manual exploitation testing are applied where risk is highest.
Q. How do I choose a vulnerability assessment and penetration testing company?
A. When evaluating a vulnerability assessment and pen testing company, look beyond branding.
Assess whether they:
- Clearly explain the difference between vulnerability assessment and pen testing
- Demonstrate technical depth across cloud, APIs, and identity systems
- Provide actionable reporting
- Integrate findings into your engineering workflows
A mature partner delivering vulnerability assessment & pen testing VAPT should focus on reducing exploitable risk, not just generating documents.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

Vibe Coding Security Risks: Why Your AI-Generated App is a Ticking Time Bomb
Key takeaways: Vibe coding removes security checks, not just effort Working code doesn’t mean secure code AI speeds up vulnerabilities, not just development Human oversight is essential for safe systems Scaling AI apps requires expert-led security rebuilds [blog_faq] We need to talk about the elephant in the IDE. Everyone is obsessing over "vibe coding." You…

Cybersecurity Risk Management - Strategy, Framework, Implementation Plan
Key takeaways: Digital transformation is rapidly increasing attack surfaces, rendering annual risk assessments obsolete in as little as 90 days. Effective cybersecurity risk management has to be treated just as any other business risk: with executive-level accountability and ongoing monitoring. Breaches involving third-party vendors exceed 60%, underscoring the need for end-to-end supply chain risk management.…

How to Build a Robust Cybersecurity Strategy in Australia for Your Business?
Key takeaways: For most Australian businesses today, cybersecurity has become as crucial as finance or operations; there is no separating it from the bigger picture. The national 2023–2030 strategy is a great backdrop, but real protection depends on how each company applies it to their own systems. Proactive businesses are focusing on fundamentals - risk…