- Why Data Sovereignty Has Become a Strategic Risk in Australia?
- Data Residency vs Data Sovereignty vs Data Localisation: The Critical Difference Most Businesses Miss
- Australian Data Sovereignty Regulations You Cannot Ignore in 2026
- Where Most Australian Organisations Fail and Why Audits Catch Them?
- The Hidden Cost of Inaction: What Non-Compliance of Data Sovereignty Really Costs Australian Businesses?
- Australian Data Sovereignty Audit Framework for 2026
- How to Build a Sovereignty-First Architecture Without Slowing Innovation?
- How Much Does It Cost to Achieve Data Sovereignty Compliance in Australia?
- When to Conduct a Data Sovereignty Audit?
- How Appinventiv Helps Enterprises Achieve Compliance with Australian Data Sovereignty Laws?
- FAQs
Key takeaways:
- Data sovereignty in Australia directly impacts contract eligibility, regulatory compliance, and enterprise risk exposure beyond basic cloud or infrastructure decisions.
- Residency is only the first step. True sovereignty ensures Australian laws, not foreign warrants, govern your enterprise’s sensitive data.
- With OAIC penalties reaching $50 million or 30% of turnover, non-compliance is now a critical threat to corporate capital reserves.
- Lack of data visibility, offshore vendor dependencies, misconfigured cloud environments and weak contractual safeguards cause data sovereignty failure in Australia
- Integrating governance into your architecture reduces implementation costs by up to 3x compared to reactive, emergency migrations.
Many Australian enterprises only discover gaps in data sovereignty when a deal is at risk, an audit is underway, or a regulator asks questions that current systems cannot clearly answer. At that point, the issue is no longer technical. It becomes commercial, legal, and reputational, often at the same time.
Data sovereignty in Australia is now tightly linked to contract eligibility, especially across government, financial services, healthcare and mining sectors. Yet, a common pattern continues to surface. Organisations assume that hosting data locally or using a major cloud provider is enough. It rarely is. Once data flows, vendor access, and cross-border dependencies are examined, gaps start to appear.
The pressure is increasing under the Privacy Act 1988, with upcoming reforms expected to further tighten accountability around how data is handled beyond Australian borders. What is changing is not just the regulation, but the expectation that enterprises can demonstrate control, not just intent.
This creates a practical challenge. Leadership teams are being asked to validate compliance without always having clear visibility into how their systems actually behave under audit conditions.
This blog quantifies the cost of non-compliance with data sovereignty in Australia, identifying where organisations typically fail during audits, and working through a checklist that reflects how these issues are evaluated in practice.
Don’t wait for a regulatory notice to identify jurisdictional gaps in your cloud stack. Align your infrastructure with the Privacy Act and ASD frameworks today.
Why Data Sovereignty Has Become a Strategic Risk in Australia?
Data sovereignty in Australia is a dire requirement that sensitive data is governed exclusively under Australian law, regardless of where it is stored, processed, or accessed. It extends beyond data residency to include jurisdictional control, vendor exposure, and cross-border data flows.
The shift toward mandatory data localisation is driven by a maturing understanding of systemic risk. Reliance on hyper-scale cloud providers has created a paradox where data is physically local but legally reachable by foreign entities.
This has caught the attention of regulators like the Australian Prudential Regulation Authority (APRA) and the Office of the Australian Information Commissioner (OAIC), who are increasingly concerned about “step-in rights” and the ability of Australian firms to maintain data integrity during international legal disputes.
Key Drivers of the Sovereign Shift
- Heightened Regulatory Enforcement: The OAIC has transitioned to a litigious posture, backed by penalty increases where serious interferences with privacy can cost an entity up to $50 million or more.
- Sector-Specific Mandates: For those in financial services, APRA’s CPS 234 continues to set a high bar for data environment control, while the Australian Signals Directorate (ASD) provides increasingly stringent guidance for “Sovereign Cloud” adoption.
- Indigenous Data Sovereignty: There is a growing recognition of indigenous data sovereignty in Australia, focusing on the rights of Aboriginal and Torres Strait Islander peoples to govern the collection and use of data that impacts them. Adhering to indigenous data sovereignty principles in Australia is becoming a core component of ESG frameworks for leading enterprises.
- Supply Chain Transparency: B2B contracts now frequently include “Right to Audit” clauses specifically targeting data flow transparency, making sovereignty a “must-have” for vendor qualification.
A Shift from Compliance to Competitive Advantage
Recent industry analysis suggests that strong data governance in Australia is becoming a differentiator. Organisations that can clearly demonstrate data sovereignty for Australia are:
- Moving faster through procurement cycles
- Reducing compliance friction
- Building stronger trust with regulators and clients
The risk, therefore, is not just regulatory. It is commercial.
Data Residency vs Data Sovereignty vs Data Localisation: The Critical Difference Most Businesses Miss
Confusing these three terms is the most common point of failure during a data audit.
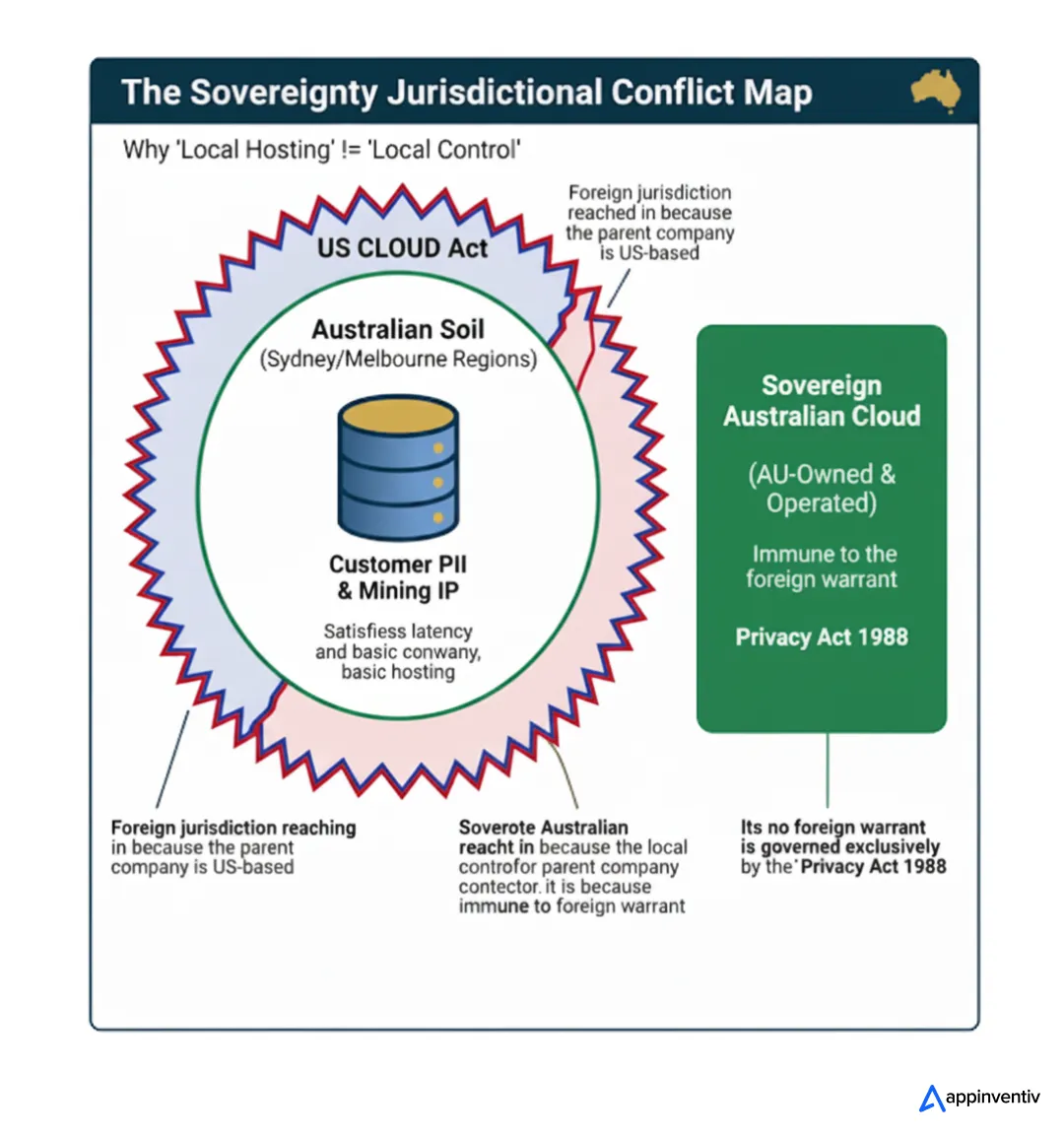
Data residency is merely a geographical designation, specifying that data is stored in a facility within Australian borders, typically for latency or performance reasons. However, residency does not provide legal immunity from foreign warrants if the service provider is headquartered overseas.
Data sovereignty is the critical layer above residency. It mandates that data is subject to the exclusive legal jurisdiction of Australia. For a business, this means ensuring that no foreign power can compel a service provider to hand over data stored on Australian soil.
Data localisation is a stricter regulatory requirement, often seen in the health or government sectors, which legally mandates that certain data types must remain and be processed entirely within the country.
Key Differences Between Data Residency, Data Sovereignty and Data Localisation:
| Aspect | Data Residency | Data Sovereignty | Data Localisation |
|---|---|---|---|
| Primary Goal | Performance and Latency | Legal Jurisdiction and Control | Strict Regulatory Compliance |
| Legal Scope | Geographic location only | Protected from foreign laws | Restricted to local processing |
| Typical Risk | Low regulatory protection | Jurisdictional overreach | High (Mandatory for specific sectors) |
Understanding these nuances is vital for data sovereignty for Australia because it dictates the selection of a technology partner. Storing data in a Sydney-based data centre owned by a US-based entity may satisfy residency, but it frequently fails the sovereignty test under the US CLOUD Act.
Remember, storing data in Australia does NOT guarantee sovereignty compliance.
Australian Data Sovereignty Regulations You Cannot Ignore in 2026
The regulatory burden for Australian businesses has reached a new peak, shifting from voluntary compliance to a mandate of proactive accountability. Governance is no longer just about preventing a breach; it is about demonstrating local control over the entire data lifecycle.
The core regulations governing data sovereignty laws Australia wide include:
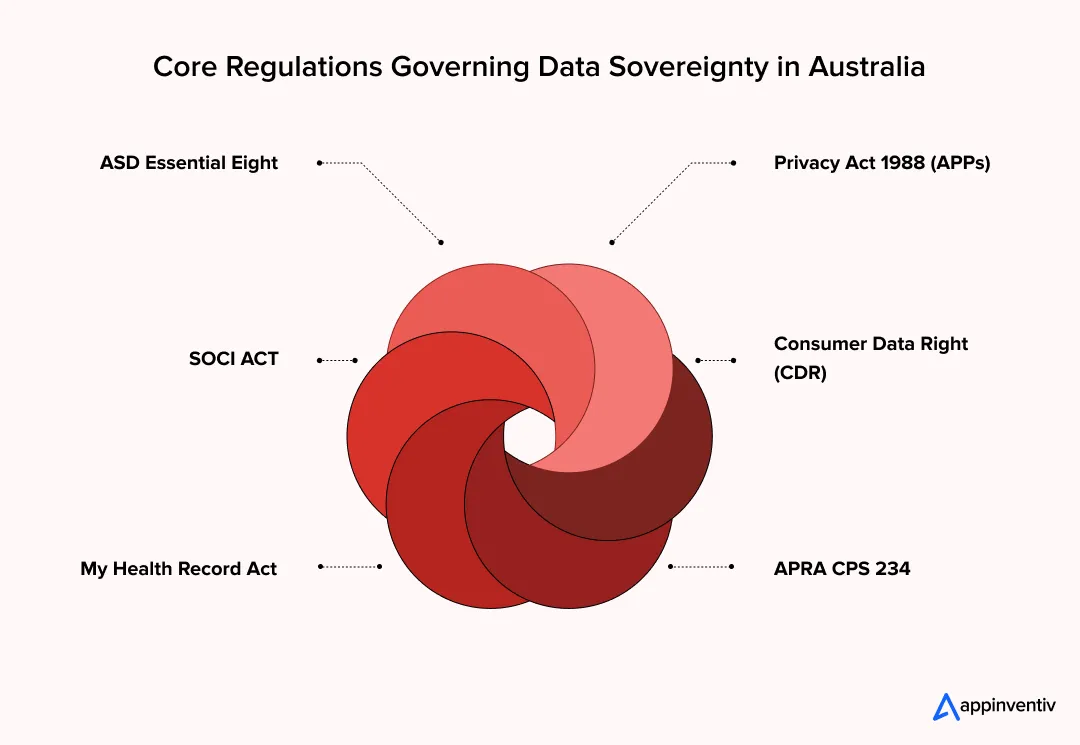
Privacy Act 1988 (2026 Reforms): The foundational pillar now includes a “fair and reasonable” test for data processing and stricter Australian Privacy Principle (APP) requirements regarding cross-border disclosures.
APRA CPS 234: Essential for financial services, this mandate requires boards to take direct responsibility for the security and sovereignty of data managed by third-party cloud vendors.
My Health Record Act & Health Records Acts: These state and federal laws impose strict localisation on clinical data, often prohibiting any form of offshore processing or storage.
Consumer Data Right (CDR): Expanding across banking, energy, and telecommunications, this requires granular data mapping to ensure consumer information remains under Australian legal jurisdiction.
ASD Essential Eight: While traditionally a cyber-defence framework, the Essential Eight is now a mandatory baseline for many Australian government suppliers. Meeting “Maturity Level Three” often requires sovereign data controls to ensure that backups and restricted administrative privileges are not exposed to foreign jurisdictional risks.
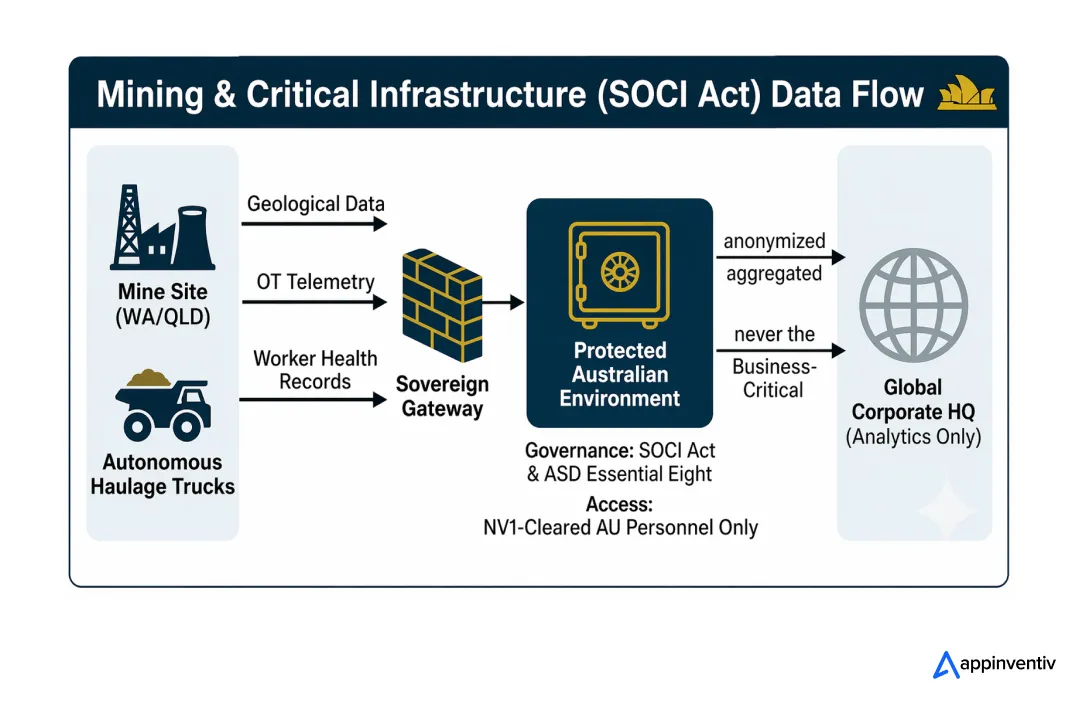
Security of Critical Infrastructure (SOCI) Act: This requires operators of essential services like mining to report on data storage arrangements, ensuring that offshore dependencies do not threaten national resilience.
Failing to align with these frameworks invites more than just fines; it creates a “compliance debt” that can stall digital transformation and disqualify firms from lucrative tier-one and government contracts.
Where Most Australian Organisations Fail and Why Audits Catch Them?
Despite significant investment in cybersecurity in Australia, many enterprises fail audits because they mistake cloud accessibility for legal control. The most common failures stem from a lack of visibility into the sub-processor layer. While a primary vendor might be Australian, their underlying support services, automated backup routines, or analytics engines often route data through jurisdictions with conflicting privacy laws.
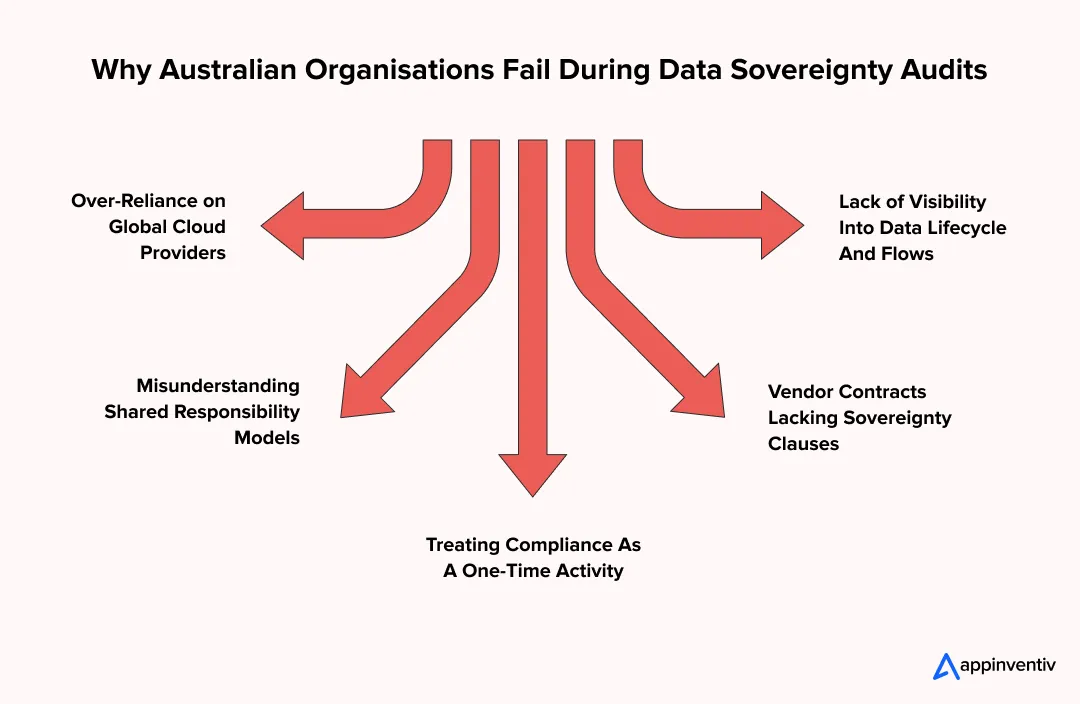
Operational gaps typically identified in audits include:
- Over-reliance on Shared Responsibility Models: Businesses often assume their cloud provider manages sovereignty, whereas providers only manage the infrastructure. The “data layer” governance remains entirely the client’s legal burden.
- Shadow Data Flows: Automated system logs, metadata, and diagnostic telemetry are frequently exfiltrated to offshore headquarters for “service improvement,” often in direct violation of data sovereignty for Australia.
- Static Compliance Checklists: Treating sovereignty as a “set and forget” task rather than a continuous engineering requirement leads to drift as systems scale or undergo updates.
- Inadequate Vendor Contracts: Many agreements lack specific “Sovereignty Clauses” that explicitly prevent the transfer of data to foreign jurisdictions under administrative warrants.
Addressing these failures requires a shift from superficial compliance to deep architectural transparency. Without a clear map of every data touchpoint, including third-party APIs and offshore support access, an organisation remains perpetually audit-vulnerable.
Appinventiv Insight
Based on Appinventiv’s work with regulated enterprises across Australia, common sovereignty failures are not infrastructure-related but stem from vendor misalignment, shadow data flows, and a lack of audit visibility.
The Hidden Cost of Inaction: What Non-Compliance of Data Sovereignty Really Costs Australian Businesses?
The cost of non-compliance with data sovereignty in Australia rarely surfaces in isolation. It unfolds across regulatory exposure, commercial setbacks, and operational disruption. What appears as a compliance gap at the system level often translates into measurable financial and reputational loss when audits, incidents, or procurement reviews begin.
The drastic impact is categorised into three distinct layers:
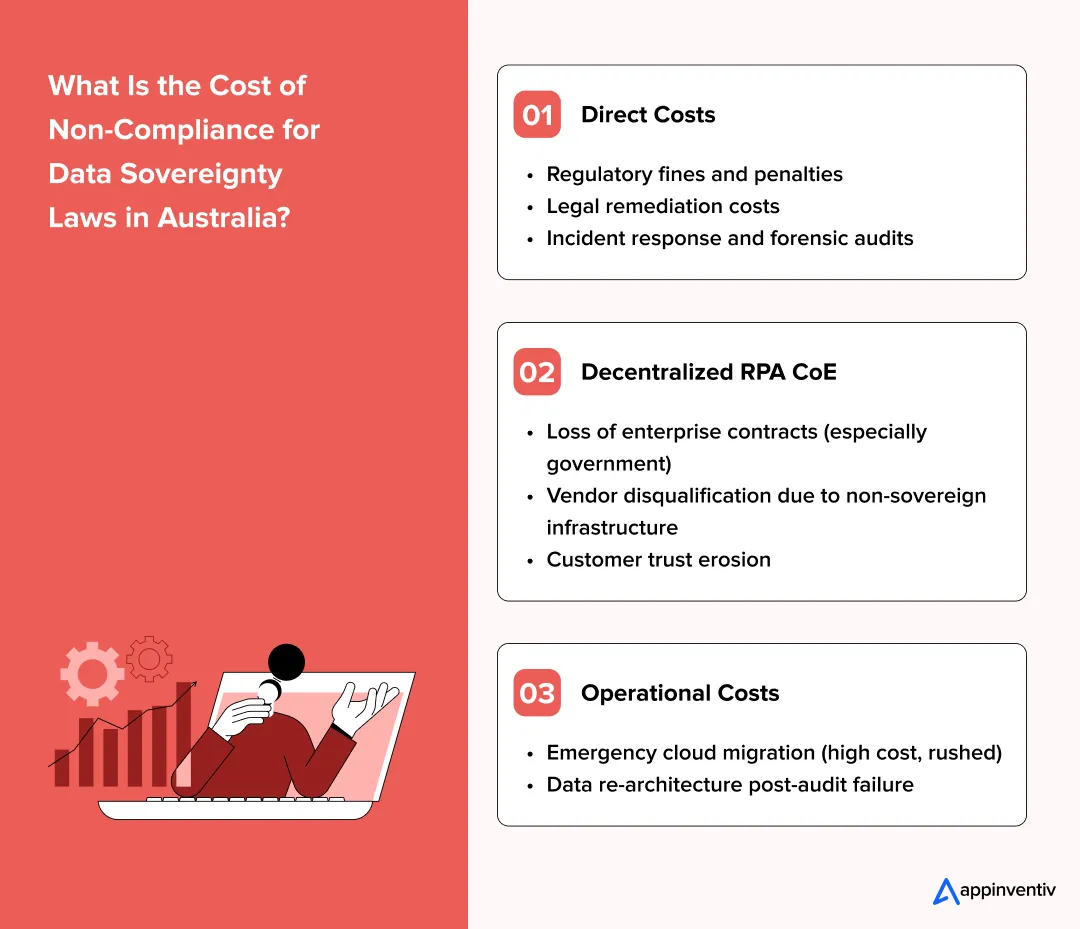
Direct Costs: Regulatory and Legal Exposure
Legislative changes have exponentially increased the stakes for serious interferences with privacy.
- Civil Penalties: Under Section 13G of the Privacy Act, corporations face fines of up to $50 million, three times the value of any benefit obtained, or 30% of adjusted turnover during the breach period, whichever is greater.
- Breach Mitigation: The record average cost of a data breach for Australian organisations reached $4.26 million AUD in 2024, representing a 27% increase since 2020.
Indirect Costs: Market and Trust Erosion
The most significant long-term impact is often felt through the loss of business opportunity and brand equity.
- Contractual Disqualification: Tier-1 financial institutions and government agencies now mandate sovereignty as a non-negotiable procurement requirement. Failing an audit leads to immediate exclusion from lucrative RFP processes.
- Customer Churn: Industry research indicates that large businesses in Australia saw a 219% increase in the cost of cyber incidents, often driven by the loss of customer trust and subsequent attrition.
Operational Costs: Technical Debt and Remediation
Fixing a sovereignty gap after an audit failure is significantly more expensive than proactive implementation.
- Emergency Cloud Migration: Rushed repatriation of data to Australian soil often carries a 3x to 5x premium due to urgent engineering requirements and service downtime.
- Re-architecture Expenditure: Diverting R&D teams to fix compliance debt slows product roadmaps and delays time-to-market for new innovations.
Here is a brief table outlining the cost of non-compliance for data sovereignty laws in Australia
| Risk Area | Estimated Impact (AUD) | Strategic Consequence |
|---|---|---|
| Regulatory Penalties | $50M+ or 30% Turnover | Direct capital depletion |
| Average Breach Cost | $4.26 Million | Immediate operational loss |
| Large Business Incident Cost | $202,700 (Avg per incident) | Incremental bottom-line impact |
Australian Data Sovereignty Audit Framework for 2026
Most organisations believe they are prepared for a data sovereignty review until they are asked to evidence it. This checklist reflects how audits are actually conducted across Australian enterprises, focusing on verifiable control rather than stated intent. The objective is simple. Can your systems demonstrate compliance under inspection, not just in documentation?
| Audit Area | What to Validate | Why It Matters |
|---|---|---|
| Data Storage | Confirm whether sensitive and regulated data is stored within Australian regions | Reduces jurisdictional exposure |
| Data Flow Mapping | Identify and document all cross-border data transfers, including APIs and analytics tools | Surfaces hidden data movement |
| Cloud Configuration | Validate that backups, failover systems, and DR environments remain within AU boundaries | Prevents silent non-compliance |
| Vendor Risk | Review third-party and subprocessor access, including support teams and offshore operations | Addresses indirect exposure |
| Access Controls | Ensure role-based access is enforced, logged, and restricted by geography where required | Strengthens accountability |
| Encryption | Validate encryption standards at rest and in transit, including key ownership location | Minimises breach impact |
| Incident Response | Confirm breach detection, reporting workflows, and alignment with Australian obligations | Ensures regulatory readiness |
| Regulatory Alignment | Map controls to APRA, ASIC, and broader governance expectations | Demonstrates audit preparedness |
How This Checklist Is Used in Practice
This framework should be integrated into your quarterly risk reviews. For enterprises outsourcing digital platform engineering services in Australia, this checklist serves as the baseline for the “Definition of Done” in any cloud migration or system upgrade. Effective implementation often requires a joint effort between Legal, Security, and Engineering teams to ensure that technical configurations match contractual obligations.
What Auditors Actually Look For
The checklist itself is not the challenge. Evidence is.
Auditors expect:
- Documented data flow diagrams that reflect current system behaviour
- Clear ownership of data across systems and vendors
- Traceability of access, including who accessed data and from where
- Alignment between stated policies and actual system configuration
Where organisations struggle is not in defining controls, but in demonstrating that those controls are consistently applied.
- Identify sovereignty gaps before regulators do
- Align with Privacy Act and ASD frameworks
- Build AU-compliant, future-ready infrastructure
How to Build a Sovereignty-First Architecture Without Slowing Innovation?
Building for data sovereignty is not about restricting innovation. It’s about designing systems where compliance is built-in, not bolted on later. The most effective approach follows a structured path, starting with visibility and moving toward continuous enforcement, ensuring your teams can scale without regulatory friction.
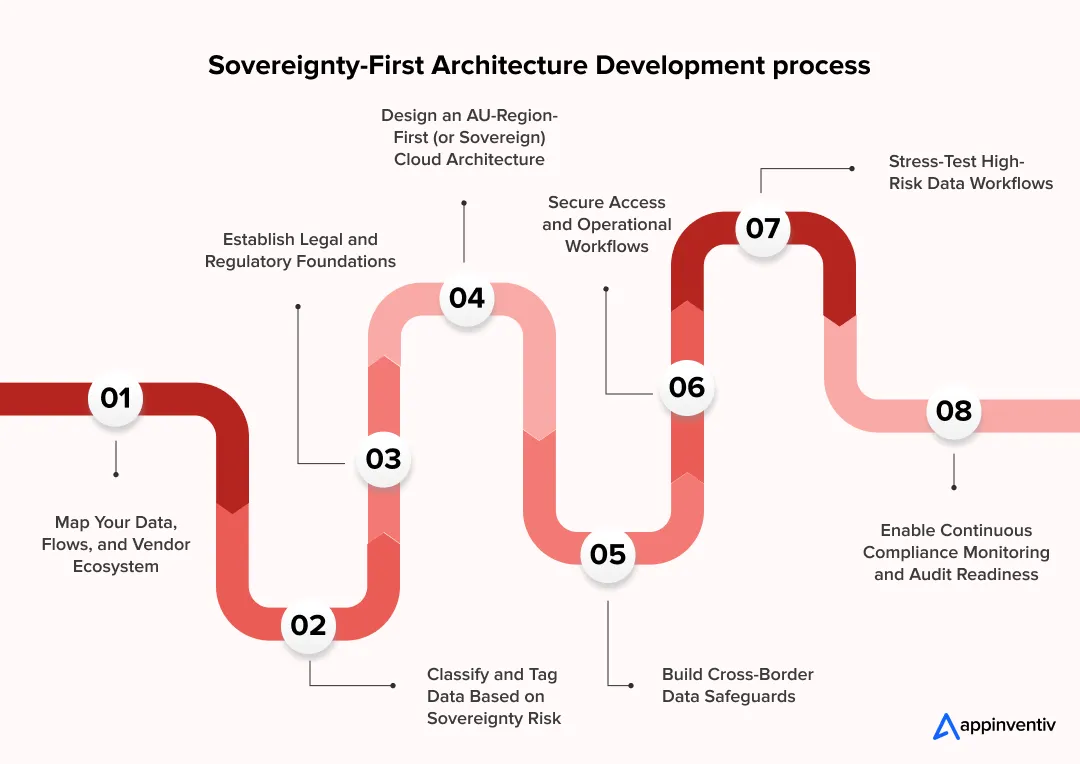
1. Map Your Data, Flows, and Vendor Ecosystem
Before controls can be enforced, visibility needs to be established across systems and third-party dependencies.
- Identify where data is created, stored, processed, and transferred
- Map cross-border flows across APIs, analytics tools, and integrations
- Document vendor and subprocessor access points
2. Classify and Tag Data Based on Sovereignty Risk
Not all data carries the same regulatory or commercial exposure. Classification enables targeted control.
- Segment data into regulated, sensitive, and operational categories
- Apply tagging across storage, pipelines, and applications
- Link classification to access, storage, and processing policies
3. Establish Legal and Regulatory Foundations
Architecture must reflect legal accountability, not just technical design.
- Align data handling with obligations under Australian privacy and sector regulations
- Define contractual controls for vendors and subprocessors
- Ensure clarity on jurisdictional exposure and liability
4. Design an AU-Region-First (or Sovereign) Cloud Architecture
Infrastructure decisions should minimise jurisdictional risk without restricting scalability.
- Anchor workloads, backups, and failover systems within Australian regions
- Evaluate sovereign cloud options for high-sensitivity environments
- Control where managed services process and replicate data
5. Build Cross-Border Data Safeguards
Some level of data movement is unavoidable. The focus should be on controlled exposure.
- Restrict and monitor cross-border transfers
- Implement contractual and technical safeguards for external processing
- Define clear approval mechanisms for any outbound data flow
6. Secure Access and Operational Workflows
Access is often where sovereignty risks materialise, especially in distributed teams.
- Enforce role-based access controls with geographic restrictions where required
- Monitor and log all access activity
- Limit offshore support or vendor access to controlled scenarios
7. Stress-Test High-Risk Data Workflows
Design assumptions often fail under real-world scenarios. Testing reveals hidden gaps.
- Simulate audit conditions and regulatory queries
- Validate how systems behave during incidents or peak load conditions
- Identify failure points in cross-border or vendor-dependent workflows
8. Enable Continuous Compliance Monitoring and Audit Readiness
Sovereignty is not static. Systems evolve, and controls must keep pace with it. Therefore, you must:
- Implement continuous monitoring of data movement and access
- Maintain audit-ready documentation aligned with system behaviour
- Schedule periodic reviews aligned with system and vendor changes
How Much Does It Cost to Achieve Data Sovereignty Compliance in Australia?
The cost of how to implement data sovereignty for Australian businesses varies significantly based on the maturity of your existing legacy systems and the complexity of your data ecosystem. It is essential to view these figures not as a “compliance tax,” but as an investment in market access.
In most enterprise scenarios, costs are distributed across four phases. Initial assessment, architectural changes, compliance upgrades and continuous governance operations.
| Component | Estimated Cost (AUD) | Operational Context |
|---|---|---|
| Data Audit & Assessment | 20,000 – 80,000 | Discovery of data flows, vendor mapping, and gap analysis. |
| Infrastructure Migration | 40,000 – 300,000 | Moving data to AU-only regions or certified sovereign clouds. |
| Security & Compliance Upgrades | 40,000 – 200,000 | Implementation of BYOK, IAM hardening, and encryption tools. |
| Ongoing Governance | 30,000 – 120,000 (Annual) | Continuous monitoring, quarterly audits, and policy updates. |
Key Strategic Insight
The total investment for a proactive sovereignty strategy is consistently lower than the cost of remediation following a breach or audit failure.
While a proactive approach allows for phased, budget-conscious implementation, a reactive “emergency migration” typically incurs a 3x premium due to the need for rapid re-architecture and the potential for service downtime.
That is where the benefits of data sovereignty for Australian businesses begin to outweigh the implementation cost.
When to Conduct a Data Sovereignty Audit?
A “set and forget” approach to compliance is the most common precursor to a regulatory breach. As your business scales, the complexity of your data flows increases, often leading to “sovereignty drift” where new microservices or vendor sub-processors inadvertently route data outside of Australian jurisdiction.
Professional practitioners at Appinventiv recommend triggering a formal data sovereignty audit during the following high-risk events:
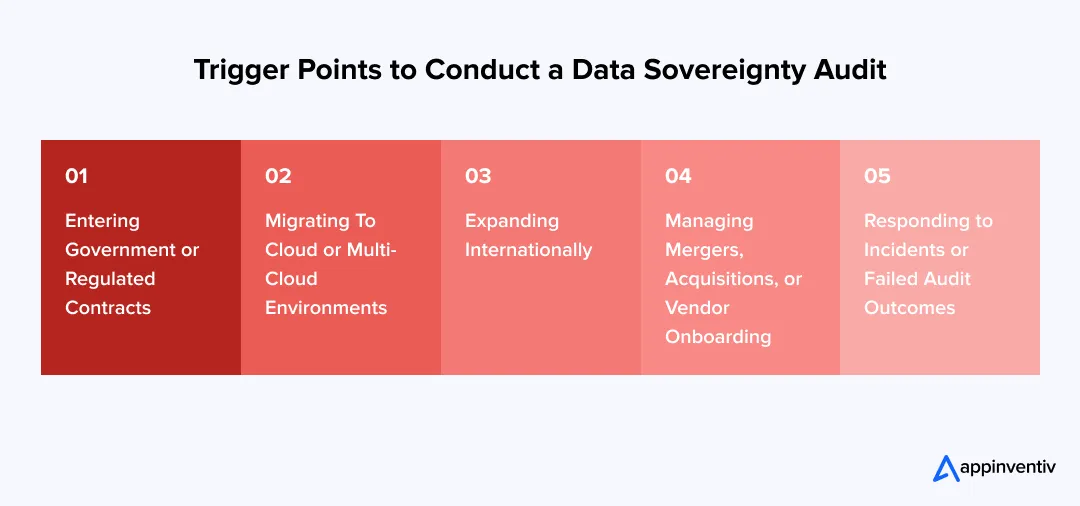
Tendering for Government or Tier-1 Contracts
Most Australian government RFPs and major banking contracts now mandate a certified “Sovereign Hosting” status. An audit ensures you can provide the necessary evidentiary artifacts to clear procurement hurdles.
Adopting Agentic AI or Automated Decision-Making
Under the December 2026 Privacy Act reforms, any system using personal data for automated decisions that significantly affect individuals requires transparent data mapping and a rigorous audit of the training data’s residency.
Migrating to cloud or multi-cloud environments
Shifting workloads between providers (e.g., AWS to Azure or into a Sovereign Cloud) often resets your jurisdictional profile. An audit ensures that while migrating to the cloud, secondary backups and DR sites remain within Australian borders.
Managing Mergers, Acquisitions, or Vendor Onboarding
Integrating a new entity’s tech stack brings unknown jurisdictional risks. A pre-acquisition audit prevents you from inheriting “compliance debt” or foreign legal exposure.
Expanding into New Markets or Cross-Border Operations
Moving into healthcare or financial services triggers immediate obligations under the My Health Record Act or APRA CPS 234, requiring a baseline sovereignty assessment.
Responding to Incidents or Failed Audit Outcomes
For entities managing critical infrastructure, the annual Risk Management Program (CIRMP) review is the mandatory window to validate that business-critical data storage arrangements remain compliant.
How Appinventiv Helps Enterprises Achieve Compliance with Australian Data Sovereignty Laws?
Achieving true data sovereignty in Australia requires more than a policy document. It requires a trusted provider of mobile app development services in Australia who understands the intersection of Australian law and complex cloud architecture.
At Appinventiv, we move beyond surface-level hosting to ensure your entire data lifecycle is engineered for jurisdictional resilience. Our team of 1600+ tech architects works alongside your leadership to transform compliance from a bottleneck into a competitive advantage, ensuring you are always audit-ready for the OAIC, APRA, or ASD.
Through our dedicated 5+ agile delivery centers in Australia, we provide the localised expertise necessary to navigate the unique challenges of the domestic market:
- Operational Excellence: We consistently deliver efficiency gains of 35% for Australian enterprises while maintaining 98% client retention rate and a 99.50% Security Compliance SLA (ISO, SOC2), ensuring your data remains protected under Australian law.
- Sovereignty-by-Design Engineering: We integrate compliance into the root of your CI/CD pipelines, ensuring that every deployment into the Australian region is automatically governed and mapped.
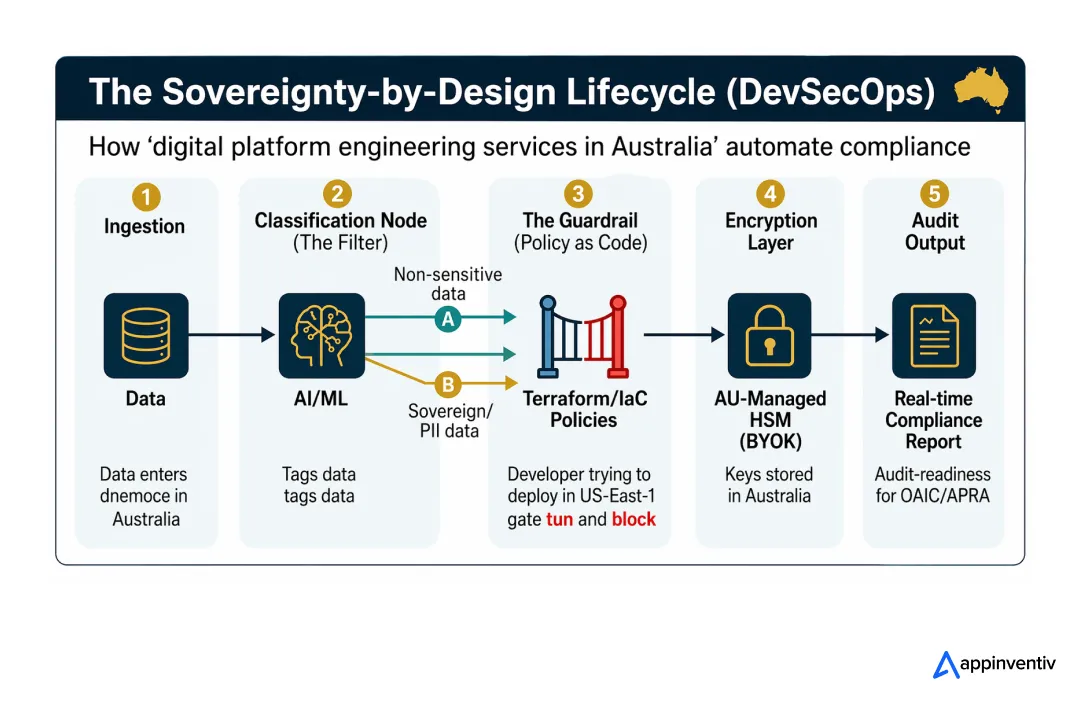
- Strategic Data Repatriation: For firms facing “compliance debt,” we manage the complex migration of data from offshore environments back to Australian sovereign clouds with zero downtime.
- Regulatory Alignment for Regulated Sectors: Our specialists ensure that your digital assets in Australia meet the strict requirements of the My Health Record Act and the Privacy Act 2026 reforms.
- End-to-End Governance Frameworks: We help you implement the indigenous data sovereignty principles in Australia, ensuring your ESG commitments and community data rights are technically enforced.
Is your data strategy audit-ready for Australia?
Identify sovereignty gaps before regulators do and align your infrastructure with the Privacy Act, APRA CPS 234, and the latest ASD frameworks. Get a data sovereignty assessment from Appinventiv today.
FAQs
Q. What is data sovereignty in Australia?
A. Data sovereignty in Australia refers to the requirement that data is governed by Australian laws, regardless of where it is stored or processed. It extends beyond location to include access, control, and jurisdiction, particularly under frameworks such as the Privacy Act 1988.
Q. Is storing data in Australia enough for compliance?
A. No. While physical residency (storing data in a Sydney or Melbourne data centre) is a prerequisite, it does not guarantee sovereignty. If the service provider is a subsidiary of a foreign corporation, they may still be compelled to provide access to that data under foreign laws, such as the US CLOUD Act, bypassing Australian privacy protections.
Q. What is the difference between data sovereignty and data residency in Australia?
A. Data residency is a geographical obligation, ensuring the “bits and bytes” physically sit on Australian soil.
Data sovereignty in Australia is a legal obligation, ensuring that those bits and bytes are only governed by Australian law. Residency is about the “where,” while sovereignty is about “who has the final legal say.”
Q. How much does it cost to achieve data sovereignty compliance in Australia?
A. Costs vary based on system complexity and current gaps.
- Small-scale environments: AUD 20K–100K (assessment and minor adjustments)
- Mid-sized platforms: AUD 70K–300K (infrastructure and control updates)
- Complex enterprise systems: AUD 300K–700K+ (re-architecture and governance layers)
Early alignment significantly reduces cost compared to reactive remediation.
Q. How long does it take to achieve compliance?
A. Timelines depend on architecture maturity and regulatory exposure.
- Initial audit and gap assessment: 2–6 weeks
- Implementation and remediation: 2–6 months
- Ongoing governance setup: continuous
Highly regulated environments may require longer validation cycles.
Q. How do you audit data sovereignty compliance in Australia?
A. A structured audit typically includes:
- Mapping data flows across systems and vendors
- Validating storage, processing, and access locations
- Reviewing vendor contracts and subprocessor exposure
- Assessing alignment with Australian regulatory expectations
- Verifying audit logs, access controls, and monitoring systems
The focus is on evidence, not documentation alone.
Q. What are the penalties for non-compliance?
A. Under the 2026 Privacy Act framework, the OAIC can pursue civil penalties for serious interferences with privacy. These fines can reach up to $50 million, three times the value of any benefit obtained, or 30% of the company’s adjusted turnover, whichever is greater.
Q. What is an example of data sovereignty?
A. A practical example of data sovereignty in Australia is when a healthcare provider stores patient records within Australian data centres and ensures that only locally authorised personnel can access or process that data. Even if a global cloud provider is used, controls are configured so that data is not transferred, accessed, or governed by foreign jurisdictions.
Q. Which industries in Australia are most affected?
A. While all businesses must comply with the Privacy Act, high-scrutiny sectors like financial services (APRA), healthcare (My Health Record), government vendors, and critical infrastructure (SOCI Act) face the most stringent localisation and sovereignty requirements.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

Key takeaways: The operating model determines survival. The code does not. Compliance under PDPL in the UAE and SDAIA in Saudi Arabia must be engineered into architecture, not added before launch. A serious build costs between AED 147,000 and AED 1,470,000 (USD 40,000 to USD 400,000), depending on scope. The single largest cost most operators…

Key takeaways: You don’t “add” Shariah later. In Shariah-Compliant platform development, the ledger, screening engine, and contracts are the product—not the UI. Start with scholars, not screens. Lock AAOIFI-aligned logic + SSB workflows before writing core APIs, or you’ll rebuild half the system. Build compliance as infrastructure. Product layer, screening layer, ledger, and governance all…
Mobile App Business Transformation in Qatar: How Can Experts Here Help You Grow?
You're considering mobile app business transformation in Qatar — and you're right to. Few markets in the region offer this combination: 100% internet penetration, the world's fastest mobile speeds, a cash-light economy compounding monthly through Fawran and QMP, and a government actively underwriting digital through Vision 2030 and the Digital Agenda 2030. The opportunity is…