- How to Convert CDS 2027 into System Requirements
- How Existing Identity Systems Fail CDS 2027 Requirements
- How to Select the Right Age Verification Model
- Reference Architecture for Age Verification Systems
- How to Implement Age Verification Across Systems
- Fraud Detection and Bypass Prevention
- Data Privacy and UAE Compliance Requirements
- How to Roll Out CDS-Compliant Age Verification
- Performance and Cost Trade-offs
- Common Implementation Mistakes
- Are You CDS 2027 Ready?
- What Comes After CDS 2027
- How Appinventiv Implements Age Verification Systems for UAE CDS 2027
- Frequently Asked Questions
Key takeaways:
- UAE CDS 2027 age verification compliance mandates real-time, auditable systems integrated into identity, access control, and enforcement layers across platforms.
- Effective compliance requires risk-based, multi-layered verification combining biometrics, Emirates ID checks, device intelligence, and behavioral signals.
- Legacy KYC systems fail CDS expectations; enterprises must implement continuous verification with dynamic risk scoring and re-validation mechanisms.
- Scalable architecture demands API-driven orchestration, SDK integration, and enforcement at the gateway level with UAE-hosted data and audit logs.
- Enterprises that align verification, fraud detection, and compliance early reduce regulatory risk, control costs, and accelerate CDS 2027 readiness.
Age verification API integration in the UAE has moved out of the product layer and into regulated infrastructure.
Child digital safety UAE regulations, set for full enforcement in January 2027 under the UAE Child Digital Safety framework, expect platforms to prove control over who accesses what at any point in time. A simple date-of-birth field or checkbox no longer meets that standard.
Platforms must now block minors from restricted content in real time, as 97% of children in the UAE already use digital devices. Each decision must be recorded, with clear logs that show how the system verified age and why access was allowed or denied.
This creates a direct link between verification systems and regulatory audits. The challenge extends beyond verification, as one in three children in the UAE is exposed to unknown contacts online.
Systems must detect and stop bypass attempts. Fake IDs, VPN masking, device spoofing, and synthetic identities already appear across high-traffic platforms in the region. Without controls to detect these patterns, verification loses its value.
This shift changes ownership inside the enterprise. Age verification now sits with engineering, identity, and risk teams. It becomes part of core system design, tied to access control, consent, identity verification workflows, and compliance reporting across the platform.
If your platform relies on any of the following, it will fail CDS audit checks:
- One-time KYC with no re-validation
- Age checks only during signup
- No enforcement at the API layer
- Missing logs for verification decisions
This guide shows how to fix these gaps at the system level.
UAE regulators are already monitoring thousands of platforms. Delay puts your system at immediate compliance risk. Identify gaps in your age verification system before regulators do.
How to Convert CDS 2027 into System Requirements
Legal clauses must convert into system behavior that can be measured, tested, and audited inside UAE-hosted environments.
How “Effective Age Verification” Works in Practice
The law expects verifiable proof tied to trusted identity signals within the UAE digital identity ecosystem.
Under CDS 2027, age verification must stand up to audit checks by local regulators such as the Telecommunications and Digital Government Regulatory Authority, which is already monitoring over 4,000 digital platforms. A simple date-of-birth field has no evidentiary value. Systems must rely on signals that can be traced and validated.
Verification must link to a trusted source. In the UAE context, this includes identity federation through UAE Pass, telco-backed identity linked to SIM registration, or verified KYC datasets used by banks and fintech platforms in DIFC and ADGM zones.
Each verification decision must produce a record. This record must show:
- What signal was used
- When verification occurred
- What decision was made
- Why was access granted or denied
These records must remain available for inspection, especially for platforms operating in regulated sectors such as media, gaming, and financial services.
How Regulation Maps to System Capabilities
Each clause in CDS translates into a specific system control that must run in production.
| Regulatory Requirement | System Capability |
|---|---|
| Restrict minor access | Real-time access control checks at the API and content layer |
| Verify age | Multi-step verification pipeline using identity, device, and behavioral signals |
| Apply protections | Policy enforcement engine aligned with content classification rules |
| Maintain accountability | Immutable audit logs stored in UAE-compliant infrastructure |
In practice, this means age verification cannot sit as a front-end check. A real-time age verification API must operate at the API gateway, content delivery layer, and identity service. Systems must evaluate age status each time a user attempts to access restricted features, not just at onboarding.
This is where most platforms in the Middle East will face gaps. Their systems verify identity once, then trust it indefinitely. CDS 2027 requires continuous enforcement, backed by logs that regulators can review at any time.
This means your system must enforce age checks at the API and service layer, not only at the user interface.
How Existing Identity Systems Fail CDS 2027 Requirements
Most identity stacks confirm identity once. CDS expects ongoing control tied to risk and access context.
Most platforms in the UAE rely on one-time KYC checks linked to onboarding. These checks, common across DIFC fintech and ADGM-regulated systems, do not update as user behavior changes. There is no link between session activity and verification level. A user verified once can access all flows without re-evaluation.
Systems lack defenses against spoofing, synthetic identities, and VPN masking, which are common across high-traffic GCC platforms. Verification does not adjust based on content type or risk level. CDS 2027 requires continuous validation, not static identity confirmation.
If your system verifies users once and trusts that state, it does not meet CDS requirements.
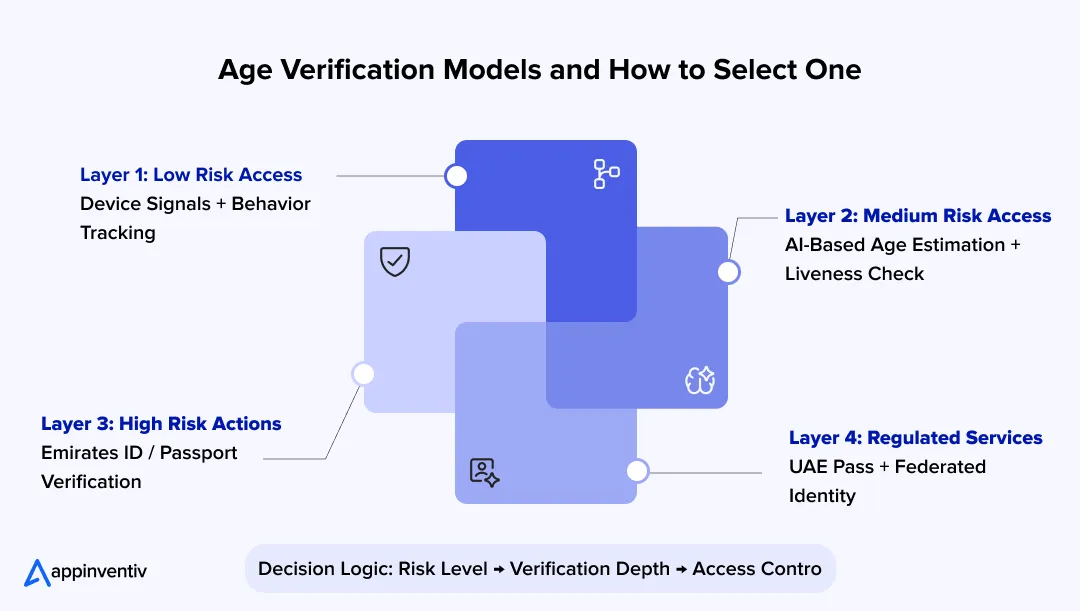
How to Select the Right Age Verification Model
Most compliance failures in the UAE come from poor integration, not missing tools. Systems often verify age but fail to enforce or share that decision across services.
The steps below show how to implement age verification API integration in the UAE so identity, APIs, and content systems act on the same decision in real time.
No single method meets CDS 2027 requirements. Enterprises must combine multiple signals to reach verifiable age assurance.
Types of Age Checks
Each method balances accuracy, cost, and user friction. Enterprises in the UAE typically rely on three core methods. Each serves a different role in the verification flow.
- Age estimation uses facial analysis models to predict age ranges. It works well for low to medium-risk flows but requires strong liveness detection to prevent spoofing.
- Document verification checks Emirates ID or passport data through KYC providers used across UAE banking and fintech systems. It offers high accuracy but adds friction.
- Combined assurance links device signals, behavior patterns, and identity data. This creates a stronger verification outcome than any single method.
Risk-Based Verification Model
Verification depth must match the level of risk tied to user activity.
| Risk Level | Verification Method |
|---|---|
| Low-risk browsing | Device fingerprinting and behavior signals |
| Medium-risk access | AI-based facial age estimation |
| High-risk actions | Emirates ID or passport verification |
| Regulated services | Federated identity via UAE Pass |
This model aligns well with UAE regulatory expectations, which follow a risk-based classification of digital platforms.
Verification depth must change during a session as risk changes, not remain fixed after login.
Choosing the Right Model
The business model defines how strict verification must be.
- Social and media platforms need adaptive checks that adjust based on content exposure and session behavior.
- Financial services operating under DIFC or ADGM rules require strict identity-backed verification at all critical steps.
- Marketplaces need mixed verification paths, where sellers and high-value transactions trigger stronger checks.
A fixed verification flow will not meet CDS 2027 expectations. Systems must adjust verification depth in real time based on risk signals.
Integration Methods Used in UAE Age Verification Systems
Enterprises in the UAE use multiple verification paths based on risk, user friction, and regulatory expectations.
Age verification in the UAE does not rely on a single method. Systems combine multiple integration paths depending on the use case and risk level.
- Document-Based Verification
The user uploads an Emirates ID or passport. The system uses OCR to extract the date of birth and validate document authenticity against known formats used in UAE KYC systems. This method provides high assurance but adds user friction. - Mobile Network Operator Data (MNO-Based Verification)
This method queries telecom providers such as Etisalat or du to confirm if the registered SIM owner meets an age threshold. It runs through standardized APIs such as CAMARA and offers a low-friction alternative to document checks. - Biometric Age Estimation
The system uses AI models to estimate age from a live selfie. Liveness detection ensures the input is not spoofed. This method works well as a first layer before triggering stricter verification. - UAE KYC Blockchain Platform
Financial institutions can access verified identity data through the national KYC blockchain network. This allows secure sharing of verified user data between banks and regulators, reducing repeated verification steps.
Reference Architecture for Age Verification Systems
A modular design gives control, traceability, and scale across UAE-hosted stacks and GCC traffic patterns.
Core Components
Each component handles a defined step in verification and enforcement.
- Verification orchestration engine: Routes requests, selects methods, and manages retries with SLAs under 300–500 ms at peak.
- Age estimation service: Runs face-age models with liveness checks at the edge or regional VPCs in UAE zones.
- Document verification module: Validates Emirates ID or passport via KYC rails used in DIFC and ADGM.
- Risk scoring engine: Combines device, IP, session, and behavior signals into a score per request.
- Policy enforcement layer: Applies access rules at the API gateway and content services.
- Audit logging system: Writes immutable logs to UAE-resident storage for regulator review.
System Flow
The system evaluates and acts within seconds.
- User attempts access
- The system assigns a risk level from the session and device signals
- Orchestrator selects verification path
- Services validate signals in parallel
- Decision and evidence are recorded
- Access is granted or blocked at the gateway
Design Principles
Design choices define compliance strength.
- Separate services for each verification step using microservices
- Store policies outside code for rapid rule updates
- Combine real-time checks with background re-validation jobs
- Store only required attributes, tokenize identity data, and keep biometrics off central storage where possible
One-time verification fails under risk-based regulation. Continuous validation must be built into your system core. Upgrade to continuous age verification at the API layer.
How to Implement Age Verification Across Systems
Age checks must run across identity, content, and payment layers, with enforcement inside UAE-hosted stacks. Enterprises looking to implement age verification in apps in the UAE must treat this as a backend control, supported by age verification system integration and age verification API integration across identity and access layers.
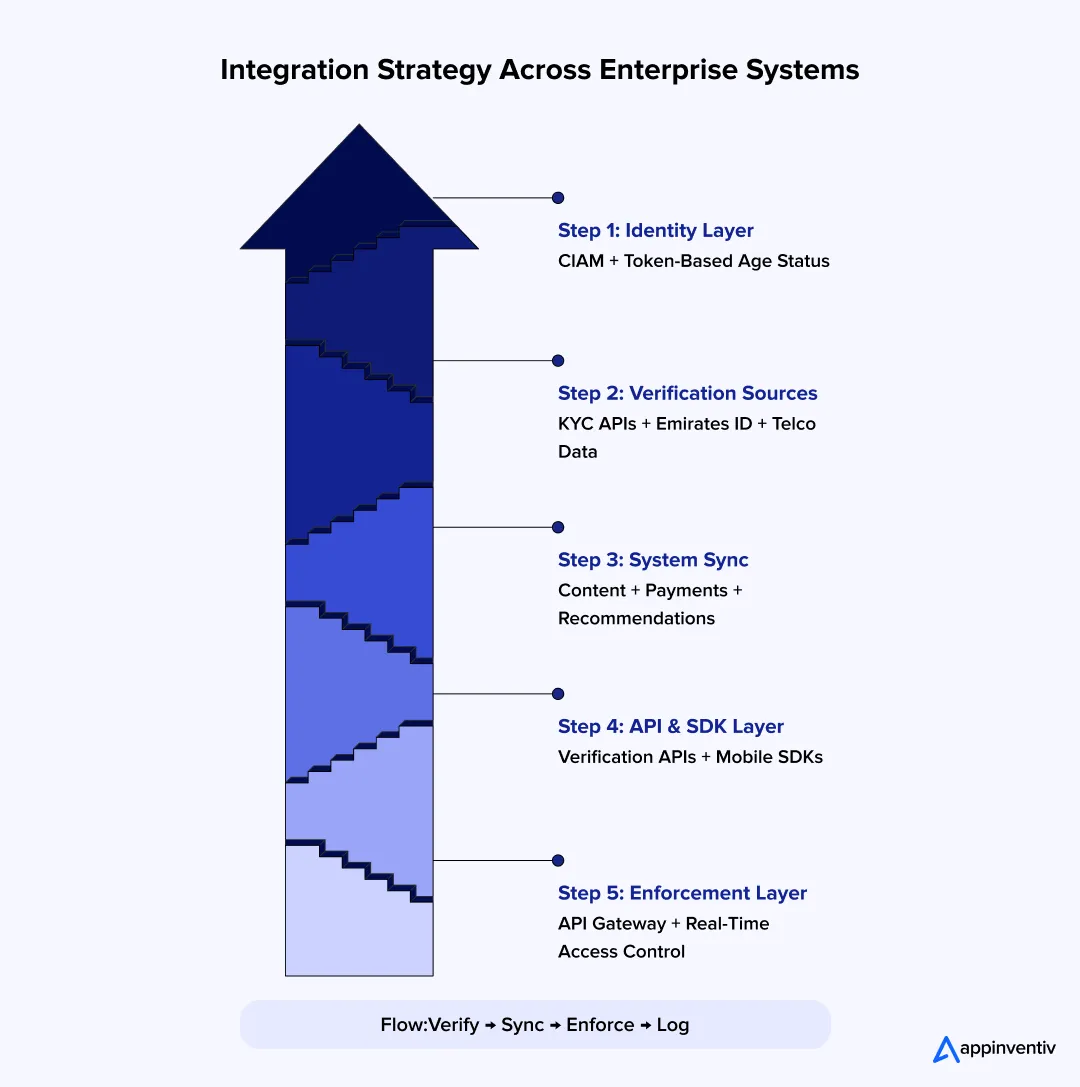
Step 1: Attach to Identity Layer
Link the age status to the user identity and session.
To integrate an age verification system in the app, start with CIAM or IAM and store age status as an attribute on the user profile. Pass this value inside the access tokens issued by the identity provider. Many UAE platforms link identity with telecom data or use UAE Pass for federation. Map that signal into your system so it can be read across services.
Step 2: Add Trusted Verification Sources
Pull verified signals from sources accepted in the region.
Connect to KYC providers that support Emirates ID validation through Emirates ID verification APIs used across UAE banking and fintech systems. These are already used by banks in DIFC and ADGM.
Add document checks only when risk crosses a threshold using an identity verification API in the UAE, widely adopted across UAE-regulated platforms. Keep this step separate so it can scale without slowing all users.
Step 3: Push Signals Across Systems
Every system must read the same age status.
Send age flags to content services, recommendation engines, and payment flows. Use a shared data layer or event stream. If a user moves from browsing to a high-risk action, the system must update their status before access.
Step 4: Build API and Event Flow
Keep systems in sync without tight coupling.
Expose verification through internal APIs and mobile SDKs for iOS and Android. Age verification SDK integration handles camera capture, liveness checks, and session control, while APIs manage backend verification and decision logic. Route traffic through gateways such as Kong API Gateway or Apigee.
Emit events when verification changes. Use a stream like Kafka so downstream systems update within seconds.
Step 5: Enforce at Runtime
Final control sits at the service layer, not the UI.
Check age status at the API gateway and backend service on every sensitive request. Do not rely on login-time checks. If risk increases, trigger re-verification before access. Log each decision with the signal used and the outcome. This keeps the system ready for audit reviews by UAE regulators.
Fraud Detection and Bypass Prevention
Verification fails at the point where systems trust inputs too easily. Fraud controls must sit inside the same decision loop.
- Most bypass attempts follow a pattern. Attackers try to trick the system before or during verification. That means every input, every frame, and every session signal needs validation.
- Start with biometric age verification in the UAE. A face scan is not enough. The system must confirm that a real person is present. Liveness checks handle this. They test movement, light reflection, and depth. Without them, a printed photo or a screen replay can pass.
- Next comes synthetic media. Deepfake inputs are now common across high-scale apps in the region. Models must inspect inconsistencies in facial movement and pixel structure. This step filters out manipulated video before age estimation runs.
- Device signals add another layer. Each session carries a fingerprint based on hardware and software traits. When the same device attempts multiple identities, the system should flag it. This is common in emulator-based attacks.
- User behavior gives further context. Fast retries, unusual navigation, or mismatched inputs often indicate abuse. These signals must feed into the same decision engine.
- Network checks close the loop. VPN traffic, proxy routing, and IP masking appear often in cross-border traffic hitting UAE services. Systems must compare location signals with device and session data.
All these checks feed a single risk score. If risk rises, the system must step up verification or block access at once.
Without these controls, attackers can bypass verification using spoofed inputs or masked sessions. That makes the system non-compliant even if verification methods are accurate.
Data Privacy and UAE Compliance Requirements
Age verification must meet strict data controls under UAE law and still deliver accurate decisions.
Data Protection Rules
UAE data laws set clear limits on what you collect and how you use it.
Platforms operating in the UAE must align with PDPL compliance and UAE data privacy requirements under the UAE Personal Data Protection Law. Age verification systems often process identity and biometric data, which fall under sensitive categories.
Key rules to follow:
- Collect only the data required for verification
- Store data for a defined purpose and duration
- Record user consent before processing identity or biometric inputs
- Maintain logs that show when and how data was used
| Control Area | Implementation Requirement |
|---|---|
| Data collection | Limit to age-related attributes |
| Storage | Define retention windows |
| Consent | Capture explicit user approval |
| Audit | Log all data access events |
Privacy-Centric System Design
System design must reduce exposure of sensitive identity data.
- Tokenize identity attributes such as age or verification status
- Store only derived values like “18+ verified” instead of raw data
- Process biometric inputs at the edge or within UAE-based zones
- Avoid storing raw facial images after verification completes
Many UAE platforms deploy edge processing within local cloud regions to keep biometric data inside controlled environments.
Data Residency
Data location directly impacts compliance in the UAE jurisdictions.
- Store critical identity and verification data within UAE data centers
- Align with sector-specific rules in DIFC and ADGM, where applicable
- Control cross-border transfers through encryption and access policies
| Data Type | Residency Expectation |
|---|---|
| Identity data | UAE-hosted storage |
| Biometric data | Local processing preferred |
| Logs and audit trails | Must remain accessible within the UAE |
Failure to control data location can trigger compliance issues, even if verification logic is correct.
How to Roll Out CDS-Compliant Age Verification
A phased rollout reduces risk, keeps systems stable under load, and improves verification accuracy over time.
Phase Plan
Each phase builds control, then extends it across UAE-hosted systems.
| Phase | Focus Area | What Happens in Practice |
|---|---|---|
| Assessment | Identify compliance gaps | Audit current flows, map where age checks fail, and review DIFC/ADGM obligations |
| Design | Define architecture and verification logic | Set risk tiers, choose signals (device, ID, federation), design APIs and policies |
| Pilot | Test with high-risk use cases | Deploy on restricted content or payments, measure latency and failure rates |
| Rollout | Expand across all systems | Extend to content, ads, and transactions, and enforce at the API gateway level |
| Monitoring | Track performance and compliance | Monitor logs, fraud rates, and model drift in UAE production clusters |
Start with high-risk flows, as enterprises have roughly a one-year compliance window. Many UAE platforms begin with payments, gaming, or media access. These areas face the highest regulatory scrutiny.
Execution Factors
Key decisions affect both compliance and user experience.
- Balance accuracy with friction. A strict ID check for every user will slow growth. Use step-up checks only when risk increases.
- Select providers that support Emirates ID and UAE Pass integration. This improves acceptance during audits.
- Track model accuracy. Face estimation models drift over time. Retrain using region-specific datasets where possible.
- Align legal and engineering teams early. CDS controls must map directly to system behavior and logs.
| Factor | Impact on System |
|---|---|
| Verification depth | Affects conversion and compliance strength |
| Provider choice | Impacts accuracy and audit acceptance |
| Model performance | Drives false positives and user drop-offs |
| Team alignment | Determines the speed of rollout and audit readiness |
A controlled rollout reduces rework. It allows teams to fix gaps before regulators or users expose them.
Also Read: AI Strategy Consulting for Enterprises in Dubai
Performance and Cost Trade-offs
Each verification step adds latency and cost. Systems must stay fast under GCC traffic peaks and keep spending predictably.
Where latency and cost come from
Identify the heavy paths in the request flow.
- Real-time checks must complete within 100–300 ms at the API gateway
- Third-party calls for Emirates ID or KYC add app development costs and network delay
- Biometric inference uses GPU or high-CPU nodes in the UAE regions
- Event streams and logging add write overhead at scale
| Component | Latency Impact | Cost Driver |
|---|---|---|
| Device/behavior signals | Low (10–30 ms) | Minimal compute |
| Age estimation (face) | Medium (80–150 ms) | GPU/CPU cycles |
| Document verification | High (200–800 ms) | Per-API fee |
| Federated identity (UAE Pass) | Medium (network dependent) | Integration + ops |
| Audit logging | Low per call | Storage at scale |
Trade-offs to manage
Choose where to spend time and money based on risk.
- Higher accuracy increases friction. Use step-up checks only when risk rises
- Strong security can reduce conversion. Gate only high-risk actions
- Cache “18+ verified” status with short TTL to avoid repeat checks
- Route low-risk traffic to fast paths. Reserve ID checks for high-risk flows
- Batch non-critical checks in background jobs to cut peak latency
| Decision Area | Faster Option | Stronger Option |
|---|---|---|
| Verification path | Device signals | ID + federation |
| Biometric use | Skip or defer | Full liveness + model |
| External calls | Minimize | Full KYC checks |
| Logging depth | Basic events | Full trace logs |
A tiered model keeps latency low for most users and applies heavy checks only where required.
Common Implementation Mistakes
Most failures come from design gaps, not missing tools or vendors. Many UAE platforms already use KYC, device checks, or identity federation. The issue lies in how these parts connect and operate under CDS expectations.
Key Mistakes and Their Impact
Each mistake weakens control and creates audit risk.
- Using a single verification method
Systems rely only on document checks or face estimation. Attackers bypass one layer easily. - Skipping re-verification
Users verified once keep full access. No checks run when behavior or risk changes. - Weak audit trails
Logs do not show which signal was used or why access was granted. This fails regulator review. - Poor user experience
Heavy checks applied to all users increase drop-offs, especially on mobile-first GCC apps. - Lack of coordination between teams
Legal defines rules. Engineering builds flows. Risk teams monitor fraud. These stay disconnected.
What Correct Implementation Looks Like
Robust age verification system integration must combine controls and keep them aligned.
- Use layered verification with step-up checks
- Trigger re-verification based on risk signals
- Store detailed logs for each decision
- Apply stricter checks only where needed
- Align legal, engineering, and risk teams on one control model
Most failures appear during the audit or scale. Fixing them later costs more than building correctly from the start.
Also Read: How to Hire Mobile App Developers in Dubai
Are You CDS 2027 Ready?
Your platform is not ready if:
- Age checks run only during signup
- The API gateway does not enforce access decisions
- Systems do not re-check users during active sessions
- Audit logs cannot show how age was verified
- Identity signals do not sync across services
Most UAE platforms meet some of these conditions today. Fixing them after enforcement starts leads to higher costs and audit risk.
What Comes After CDS 2027
Age checks move from one-time gates to continuous identity control, making compliance-ready app development in the UAE essential across sessions and services.
- Systems will re-check users during sessions using device, network, and behavior signals. Risk spikes will trigger step-up checks in real time.
- AI models will adjust verification depth based on usage patterns seen on UAE platforms, not fixed rules.
- Identity signals will link across apps through federation, such as UAE Pass and telco-backed identity.
- GCC regulators will align controls across the UAE, Saudi Arabia, and Bahrain, pushing shared standards for age assurance and audit logs.
Enterprises have limited time to redesign systems. Delays increase audit risk and rework costs.
How Appinventiv Implements Age Verification Systems for UAE CDS 2027
Most enterprises do not struggle with choosing verification methods. They struggle with integrating them into systems that regulators can audit.
Enterprises need a partner that can build and run age verification systems that meet UAE compliance and scale across high-traffic platforms.
Appinventiv delivers age verification system integration and identity verification integration services across UAE platforms, working at the intersection of identity, risk, and system design.
The focus stays on production-ready systems that enforce policies in real time and generate audit logs that stand up to regulator review. Verification logic is not treated as a feature. It is built into API layers, identity services, and access control flows.
As an AI development company in Dubai, Appinventiv’s engineering teams bring experience in AI models for face-based age checks, fraud detection, and device intelligence.
These models are deployed with strong liveness checks and tuned for real-world traffic patterns seen across the UAE and GCC platforms. Integration work spans CIAM systems, KYC providers, and federated identity systems such as UAE Pass.
Execution strength comes from regional experience. Appinventiv has delivered 1000+ digital projects in the Middle East, with 10+ years in the region and 20+ UAE partnerships. The team has supported 12+ government and compliance programs and modernized 500+ enterprise workflows. Systems maintain 99.90% SLA uptime and have delivered up to 40% cost savings through structured transformation.
This depth positions Appinventiv as a trusted age verification solution provider in the UAE, delivering faster CDS 2027 readiness, lower fraud exposure, and scalable age verification API integration in the UAE that grows with your user base.
This ensures your system enforces age checks in real time and produces logs that stand up to regulatory review.
Let’s connect and build CDS-ready age verification systems.
Frequently Asked Questions
Q. How can I integrate age verification APIs into a mobile app in the UAE?
A. Age verification API integration in the UAE starts with your identity layer. Connect the app to a CIAM system that issues tokens with age status. Call verification APIs during signup and before sensitive actions. Use device signals for low-risk flows and step up to ID checks when risk rises. Integrate with UAE Pass where possible. Enforce decisions at the API gateway and record each decision in audit logs stored in the UAE regions.
Q. How do I know if my system meets CDS 2027 requirements?
A. Your system meets CDS 2027 requirements only if it verifies age at runtime, enforces access through the API layer, and records each decision with time, method, and reason. It must re-check users during active sessions and maintain detailed audit logs that regulators can review at any time.
Q. What are the compliance requirements for age verification under UAE CDS 2027?
A. Systems must prove age using trusted signals, not user input alone. Each decision must be logged with time, method, and outcome. Access to restricted content must be blocked in real time. Controls must resist spoofing and proxy use. Data handling must align with the UAE Personal Data Protection Law, including consent, minimal data use, and clear retention rules.
Q. Which technologies are commonly used for age verification integration?
A. Teams combine several tools. Face-based age estimation with liveness checks handles mid-risk flows. Document verification validates the Emirates ID or passport through the KYC APIs. Device fingerprinting links sessions to hardware. Behavior scoring tracks anomalies. API gateways such as Kong API Gateway or Apigee enforce access at runtime. Event streams keep systems in sync across content, payments, and ads.
Q. What is the cost of integrating an age verification system into an app?
A. Cost depends on volume and method mix. In the UAE, device and behavior checks are low-cost per request. Face estimation adds compute cost, often AED 0.01–0.05 per call on CPU, higher on GPU workloads in local cloud regions. Document checks using Emirates ID or KYC providers can range from AED 0.50 to AED 3 per call. Integration, security, and audit logging add fixed costs. A tiered model limits spend by applying high-cost checks only to high-risk actions.
Q. How do businesses ensure secure and scalable age verification implementation?
A. Use a layered model with step-up checks. Run decisions at the API gateway for every sensitive request. Keep services separate, so each part scales on demand. Store only derived values such as “18+ verified.” Process biometrics within the UAE regions and avoid central storage of raw images. Stream events to update systems in seconds. Track model accuracy and fraud rates, then adjust rules as traffic patterns change.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.
How to Find the Right AI Ethics Consultant in the Middle East for Your Digital Product
Key takeaways: Hire an AI ethics consultant before architecture and data flows are locked. The right partner turns responsible AI into product controls, not policy fluff. GCC compliance knowledge matters, especially UAE PDPL, CBUAE, SDAIA, ISO, and NIST. Bias testing must cover Arabic, dialects, names, locations, proxy data, and UX gaps. Strong AI governance needs…
AI Browser Agents Development: Steps, Costs, Challenges, and More
Key takeaways: Rely on aggressive error recovery and deterministic APIs instead of just throwing a larger model at the reliability gap. Protect your budget by defaulting to the DOM and only triggering expensive visual processing when the markup lies to you. Treat the web as hostile by structurally isolating your planning models from untrusted page…

AI Hallucinations in Enterprise Apps: Real Costs, Root Causes, and How to Fix Them
Key takeaways: AI hallucinations are no longer minor model flaws; they now create real financial, legal, and reputational exposure for enterprises. Most hallucination failures happen because AI systems are not grounded in current, verified, and access-controlled business data. RAG helps reduce hallucinations, but it only works well when paired with citation enforcement, clean retrieval, and…