- Enterprise GRC Implementation Roadmap
- Common GRC Implementation Challenges and Solutions
- Why Appinventiv Is the Execution Engine for GRC?
- GRC Architecture: How Centralized Risk Systems Work
- Core Components of a GRC Program & Framework
- Best Practices & Benefits of GRC Implementation
- How to Update a GRC Framework With Appinventiv
- FAQs
Key takeaways:
- GRC implementation connects governance, risk, and compliance into a unified enterprise system.
- Fragmented tools limit real-time risk visibility and delay audit readiness across organizations.
- Centralized GRC platforms enable continuous monitoring, automation, and system-level compliance tracking.
- Integration with enterprise systems turns GRC into a live operational risk management layer.
- Strong governance frameworks improve audit outcomes, reduce risk exposure, and support regulatory alignment.
GRC implementation is the process of building a connected system that tracks governance rules, risk exposure, and compliance controls across an enterprise. It links policy management, risk registers, audit records, and security signals into one operational view.
Most enterprises already run parts of this system. Security teams track threats in SIEM tools. Compliance teams manage controls in separate platforms. Audit teams store evidence in isolated repositories. Each function works, yet the data stays disconnected.
This gap creates a serious problem. Recent global studies indicate that 71% of organizations now expect compliance teams to play a central role in digital transformation, reflecting a shift toward risk-led decision making.
Leadership cannot see real-time risk. Reports take days to compile. Control failures surface late. In fast-moving environments with cloud systems, third-party vendors, and AI-driven processes, risk does not stay in one place. It moves across systems, data flows, and teams.
The issue is not the absence of tools. It is the absence of integration and continuous monitoring. Fragmented systems and limited visibility make it hard to answer simple questions about current risk exposure.
This blog explains how enterprises move from scattered governance to a centralized GRC system. It breaks down GRC implementation steps, architecture, and key challenges.
Most organizations already use compliance to manage risk in real time. Limited visibility slows response and increases exposure across systems.
Enterprise GRC Implementation Roadmap
GRC implementation strategy usually becomes a priority when teams lose track of where risk sits. Logs come from cloud systems, security tools, and identity platforms, but they do not connect.
Compliance teams map controls for ISO 27001, PCI DSS, or GDPR in separate files. Audit teams pull evidence from tickets, emails, and shared drives, which slows everything down.
AI systems add more risk without clear tracking of data or access. Studies show that 63% of organizations still lack formal AI risk governance, and 97% of AI-related security incidents are linked to weak access controls.
A structured roadmap brings these pieces into one system, covering the core GRC implementation steps so risk can be tracked in real time.
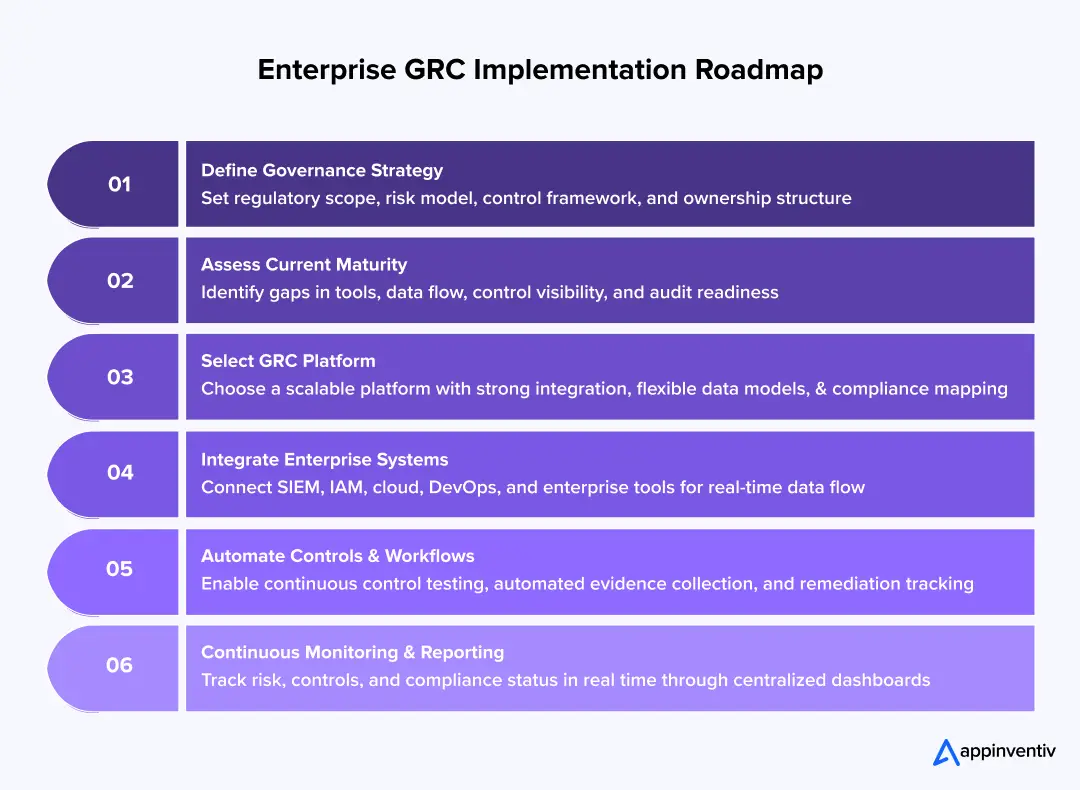
Phase 1: Define Governance Strategy
Start by setting a clear structure for governance, risk & compliance implementation across the enterprise. This step defines what the system must track before any tool is selected.
Key areas to define
- Regulatory scope
Identify all applicable governance risk compliance guidelines, regulations, and standards. - Control framework
Choose a base framework and map controls to systems and processes. - Risk model
Define how risk is measured and prioritized. - Ownership model
Assign clear accountability for each control and risk.
Growing Global Regulatory Pressure
Companies operating across regions rarely deal with just one compliance framework, and AI regulation is rapidly becoming one more layer to navigate.
| Region | Regulation / Framework | Focus Area |
|---|---|---|
| Global | PCI DSS | Security standards for payment card processing and transaction data protection |
| Global | ISO 27001 | Information security management systems and risk-based security controls |
| United States | SOX (Sarbanes–Oxley Act) | Financial reporting integrity and internal control governance |
| United States | HIPAA | Protection of healthcare data and patient privacy |
| United States | SEC Cybersecurity Disclosure Rules | Mandatory disclosure of significant cyber incidents and risk management practices |
| United States | NIST Cybersecurity Framework | Security governance, risk assessment, and cybersecurity best practices |
| European Union | GDPR | Data protection, privacy rights, and cross-border data governance |
| European Union | DORA (Digital Operational Resilience Act) | Operational resilience and ICT risk management for financial institutions |
| European Union | EU AI Act | Governance, transparency, and risk management requirements for AI systems |
| Australia | APRA CPS 234 | Information security controls and cyber resilience for financial institutions |
| Australia | Australian Privacy Act | Data privacy protection and handling of personal information |
| Middle East (Saudi Arabia) | Personal Data Protection Law (PDPL) | Personal data governance, consent requirements, and cross-border data transfer rules |
| Middle East (UAE) | UAE Federal Data Protection Law | Data privacy, processing requirements, and data subject rights |
Also Read: EU Data Act Compliance: A Complete Guide for Executives
Around 85% of organizations report increasing regulatory complexity, and nearly three-quarters take over a year to implement new requirements, widening the gap between compliance and execution.
Control mapping example
- Access control policies → Okta, Azure AD
- Logging and monitoring → Splunk, ELK stack
- Data protection controls → Encryption systems, DLP tools
- Incident response → SIEM and SOAR platforms
Risk scoring structure
- Likelihood of occurrence
- Financial or operational impact
- Regulatory exposure
Each risk should have:
- a defined owner
- linked controls
- a measurable score
What happens if this step is weak
- Controls differ across teams and systems
- Risk ownership stays unclear
- Compliance gaps surface during audits
- Integration becomes harder in later stages
This phase sets the foundation of your governance risk and compliance framework. Every system, workflow, and report in the GRC program depends on it.
Phase 2: Assess GRC Maturity
Before adding new systems, understand how governance works today. Most enterprises already run parts of GRC, but understanding the factors affecting GRC implementation is essential before moving forward.
What to assess
- Current tools
List systems used for risk, compliance, and audit.
Examples: ServiceNow (tickets), Jira (issues), Excel (risk registers), Splunk (security logs) - Data flow
Track how risk and compliance data move across systems.
Check if data flows through APIs or manual exports. - Control visibility
Identify where controls are tracked and tested.
Check if evidence is stored centrally or across shared drives and emails. - Audit process
Review how audit evidence is collected.
Measure the time taken to prepare for audits.
Typical maturity gaps
| Area | Common issue | Impact |
|---|---|---|
| Risk tracking | Stored in spreadsheets | No real-time updates |
| Compliance mapping | Manual control mapping | High error rate |
| Evidence collection | Email and shared drives | Audit delays |
| System integration | Limited or no APIs | Data stays siloed |
While 98% of enterprises have adopted some level of compliance automation, most still operate without fully integrated GRC data across systems.
What to look for
- Duplicate control records across teams
- Delays in audit readiness
- Security data not linked to compliance reporting
- No single source of truth for risk data is a problem that compounds quickly when data governance gaps go unaddressed across enterprise systems.
What happens if this step is skipped
- Existing gaps remain hidden
- New platform fails to connect with real workflows
- Data migration becomes complex and costly
This phase gives a clear picture of where GRC stands today and what must change before building a centralized risk and compliance system.
Phase 3: Select and Configure GRC Platform
At this stage, the goal is to run a GRC platform cost-benefit analysis and choose a system that can act as the central record for governance, risk, and compliance data.
What to evaluate
- Platform capability
Look for GRC platform features that handle policy management, risk registers, compliance tracking, and audit workflows.
Common platforms: ServiceNow GRC, RSA Archer, MetricStream, SAP GRC - Integration support
Check for API support and connectors for tools like Splunk, Okta, Azure AD, Jira, and ERP systems. - Data model flexibility
The platform should allow custom risk models, control libraries, and regulatory mappings. - Scalability
It should handle multiple business units, regions, and regulatory frameworks.
Configuration focus areas
- Policy lifecycle setup
Define how policies are created, approved, versioned, and acknowledged - Risk register design
Structure risk entries with ownership, scoring logic, and linked controls - Control library creation
Map controls to frameworks such as ISO 27001 or NIST CSF - Compliance mapping
Link each control to one or more regulatory requirements
Example mapping structure
| Control | System | Regulation |
|---|---|---|
| Access control | Okta / Azure AD | ISO 27001, GDPR |
| Log monitoring | Splunk | PCI DSS |
| Data encryption | Cloud KMS | GDPR, DPDP Act |
For teams building systems that handle personal data, understanding GDPR compliance software requirements is essential before configuring data encryption controls.
What happens if platform selection is rushed
- Limited integration with existing systems
- Rigid data models that do not match business needs
- Continued use of spreadsheets outside the platform
- Poor adoption across teams
The platform sets the foundation for how GRC will operate daily. A poor fit leads to fragmented workflows even after implementation, which is why platform selection is one of the key factors in GRC implementation.
Phase 4: Integrate Enterprise Systems
At this stage, the GRC platform must connect with the systems that generate risk and compliance data, including those built through software development services. Without integration, the platform becomes another isolated tool.
What to integrate
- Security monitoring systems
SIEM tools like Splunk or IBM QRadar for logs, alerts, and incident data - Identity and access management
Okta, Azure AD for user access, role changes, and authentication events - DevOps and cloud systems
Jenkins, GitHub, Kubernetes, and AWS CloudTrail for deployment activity and configuration changes, each of which carries its own cloud security risks. - Enterprise systems
ERP platforms, ticketing tools like ServiceNow or Jira for operational workflows
Integration methods
- API-based connections for real-time data flow
- Event streaming using tools like Kafka for continuous updates
- Scheduled syncs for legacy systems without API support
What the integration should enable
- Automatic updates to risk registers from live system events
- Control validation using real-time system data
- Linking incidents to compliance controls and audit records
- Centralized tracking of access changes and security events
Example flow
- User access change in Okta → triggers control validation
- Security alert in Splunk → updates risk score
- Deployment in Jenkins → logs compliance event
- Ticket closure in Jira → updates remediation status
What happens if integration is weak
- Risk data remains static and outdated
- Manual updates continue across teams
- Compliance tracking lags behind actual system activity
- Leadership still lacks a real-time view
This phase turns GRC from a reporting system into a live operational layer connected to enterprise systems.
Phase 5: Automate Workflows and Controls
After integration, the focus shifts to reducing manual work through security compliance automation that keeps controls validated without human intervention. Controls, evidence collection, and remediation must run through defined workflows inside the GRC system.
What to automate
- Control testing
Validate controls using system data instead of manual checks.
Example: verify access reviews through Okta logs - Evidence collection
Pull audit evidence directly from systems like Jira, ServiceNow, and cloud logs. - Remediation workflows
Create tasks automatically when a control fails or a risk threshold is crossed. - Approval processes
Route policy updates, exceptions, and risk acceptances through defined workflows
How automation is implemented
- API triggers from integrated systems
- Rule-based workflows inside platforms like ServiceNow GRC
- Event-driven actions using tools such as Kafka or cloud-native services
Example automation flow
- Failed login pattern detected in Splunk → triggers security control check
- Control failure → creates a remediation task in Jira
- Task completion → updates control status and closes risk item
- Evidence stored automatically → ready for audit review
What automation should achieve
- Continuous control validation
- Faster audit preparation
- Reduced manual coordination across teams
- Clear tracking of remediation progress
What happens if this step is ignored
- Teams rely on manual evidence collection
- Audit cycles remain slow and error-prone
- Control failures go unnoticed
- Compliance tracking becomes reactive instead of continuous
This phase reduces operational friction and keeps governance processes aligned with real system activity.
Phase 6: Continuous Monitoring and Reporting
At this stage, GRC shifts from periodic review to continuous tracking. Risk and compliance data must be updated as systems change, not after audits.
What to build
- Risk dashboards
Show current risk scores, control status, and open issues across business units. - Control monitoring
Track whether controls are active, failed, or pending validation - Compliance status views
Map live control data to regulations such as ISO 27001, PCI DSS, or GDPR
Data sources
- SIEM tools like Splunk for security events
- Identity systems like Okta or Azure AD for access activity
- Ticketing systems like Jira for remediation tracking
- Cloud logs from AWS CloudTrail or Azure Monitor feed risk signals continuously. Teams running multi-cloud environments should also account for cloud compliance requirements specific to each provider.
What should update in real time
- Risk scores based on new incidents or system changes
- Control effectiveness using live system data
- Audit readiness based on available evidence
- Remediation status from workflow systems
Example reporting flow
- Security alert triggers in Splunk
- Risk score updates in the GRC platform
- Dashboard reflects change instantly
- Compliance status adjusts based on control impact
What leadership should see
| Role | Focus |
|---|---|
| CIO | System and infrastructure risk |
| CRO | Enterprise risk exposure |
| Compliance Teams | Control coverage and gaps |
| Board | High-level risk indicators |
CIOs focused on system and infrastructure risk will find a deeper operational lens in IT risk management practices that complement GRC dashboards.
What happens if monitoring is not continuous
- Reports reflect outdated data
- Risks remain hidden until audits
- Leadership decisions rely on incomplete information
- Compliance gaps surface late
This phase gives leadership a clear and current view of enterprise risk, backed by live data from operational systems.
Common GRC Implementation Challenges and Solutions
Most GRC programs fail during execution, not planning. The issues show up once teams try to connect systems, data, and ownership across the enterprise.
Organizational Silos → Inconsistent Risk Ownership
Security, compliance, and audit teams work in separate systems, which is one of the most persistent enterprise compliance challenges in large organizations. Each team tracks its own risks and controls.
- Risk registers do not match across teams
- Control ownership stays unclear
- The same risk appears in multiple places
Impact
- Financial risk increases as issues stay unaddressed
- Decisions slow down since no single owner is accountable
- Compliance gaps appear during audits
Fragmented Data → Delayed Audits
Evidence sits across tools like Jira, ServiceNow, email threads, and shared drives.
- No central repository for audit data
- Manual effort required to collect evidence
- Version control issues across documents
Impact
- Audit preparation takes weeks instead of days
- Higher audit costs due to manual work
- Increased risk of failed compliance checks
With the average global data breach costing $4.44 million, cybersecurity risk management becomes a financial imperative, not just a technical one.
Tool-First Implementation → No Integration
Many enterprises deploy a GRC platform without connecting it to operational systems.
- No link to SIEM tools like Splunk
- Identity systems like Okta remain disconnected
- DevOps activity does not feed into compliance tracking
Impact
- Risk data stays static and outdated
- Controls cannot be validated in real time
- Investment in GRC tools does not deliver value
Lack of Leadership Alignment → Low Adoption
GRC remains a compliance initiative instead of a business priority.
- No clear risk appetite defined
- Limited executive visibility into risk dashboards
- Teams treat GRC as a reporting task
Impact
- Low adoption across business units
- Governance processes remain inconsistent
- Risk exposure increases without oversight
Regulatory Overload → Reactive Compliance
Enterprises deal with multiple frameworks at once, often across regions.
- Controls are mapped manually to ISO 27001, PCI DSS, GDPR, and others, with AI compliance rules adding a new and rapidly shifting layer.
- No system to track regulatory changes
- Compliance updates handled after deadlines
Impact
- Missed regulatory requirements
- Financial penalties and legal exposure
- Continuous pressure on compliance teams
These challenges build over time. Each one adds friction to governance processes and increases the cost of managing risk. Without a structured implementation, GRC remains fragmented and reactive — and the GRC business case never gets fully realized.
Fragmented systems and delayed tracking increase audit failure risk; fix integration gaps now before compliance issues surface under regulatory pressure.
Why Appinventiv Is the Execution Engine for GRC?
Most GRC programs fail at execution, where systems, data, and ownership do not connect. We implement GRC as a working system across enterprise environments.
We design a unified governance structure, integrate tools like Splunk, Okta, ServiceNow, and cloud platforms, and automate control validation using live data.
We centralize risk and compliance data, map controls to regulations such as ISO 27001 and GDPR, and build workflows that run continuously. This shifts GRC from manual tracking to real-time risk monitoring backed by system-level integration.
Proven Enterprise Execution
- 3000+ solutions delivered across industries
- 2000+ software products built and deployed
- 95% on-time delivery record
- 10+ years of enterprise experience
- 95% client satisfaction rate with 90% repeat clients
Real-World Enterprise Systems Delivered by Appinventiv
| Use Case | Before | After | Measurable Impact |
|---|---|---|---|
| Challenger Bank (Cloud Governance) | Fragmented cloud systems, no unified risk visibility, slow deployments | Centralized monitoring with integrated governance and risk tracking | 30% reduction in infrastructure cost, 40% faster deployments, 99.98% uptime, scaled to 2M+ users with continuous compliance readiness |
| Digital Wallet (Australia Compliance) | Disconnected identity, transaction, and compliance systems, and manual audit tracking | Integrated identity verification, transaction monitoring, and compliance controls | Compliance tracking moved to real-time, audit readiness shifted from periodic to continuous, and transaction-level risk validation was enabled instantly |
We do not treat GRC as a reporting layer. We implement it as a system that connects policies, controls, and live enterprise data.
GRC Architecture: How Centralized Risk Systems Work
A centralized risk management system runs as a layered architecture where live system data feeds risk tracking, control validation, and reporting.
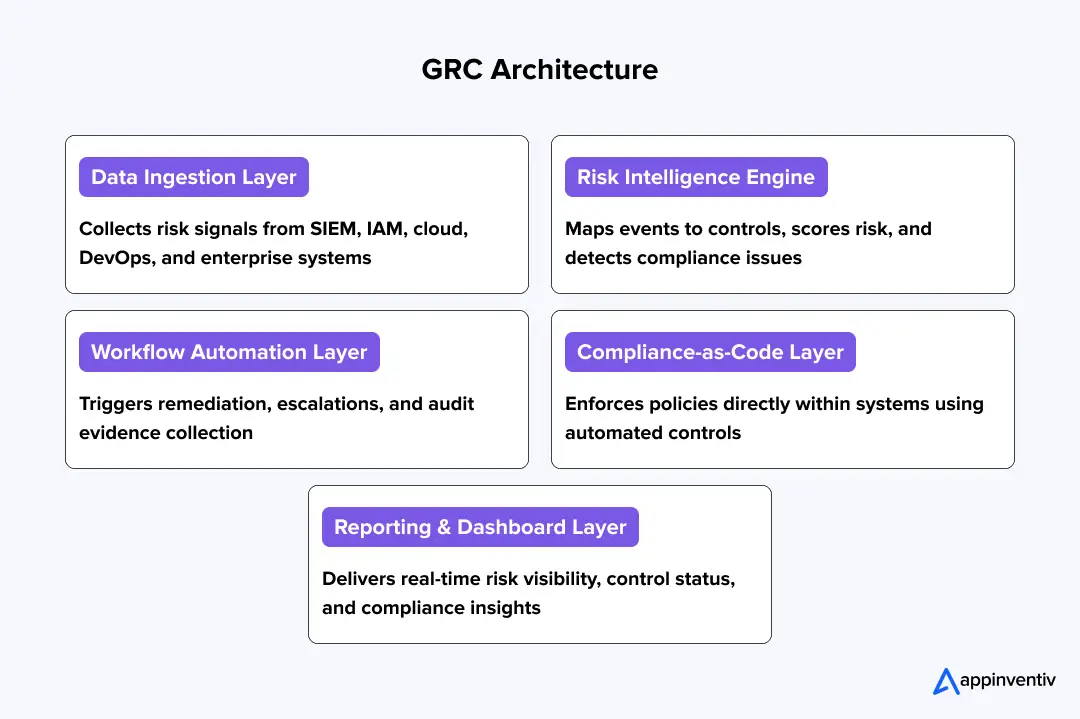
Data Ingestion Layer
This layer brings together data from all systems that generate risk signals.
- SIEM tools like Splunk for security events
- Identity platforms like Okta and Azure AD for access logs
- Cloud logs from AWS CloudTrail and Azure Monitor
- DevOps tools like Jenkins and GitHub for deployment activity
- Ticketing systems like ServiceNow and Jira
Data flows through APIs, log pipelines, or event streams such as Kafka. This creates a continuous feed of risk signals.
Risk Intelligence Engine
This layer turns raw system data into clear risk insights.
- Maps events to controls and regulations
- Scores are risk-based on impact and exposure
- Detects issues like unauthorized access or misconfigurations
Example: A failed access control in Okta updates the risk score and flags a compliance issue.
Workflow Automation Layer
This layer makes sure every risk event leads to action.
- Creates remediation tasks in Jira or ServiceNow
- Escalates high-risk issues
- Collects audit evidence automatically
DevSecOps integration
- Policy checks run during CI/CD pipelines, a practice that reflects the broader role of DevOps in compliance.
- Deployments fail if controls are not met
Compliance-as-Code Signals
This layer enforces controls directly inside systems instead of documents.
- AWS Config and Azure Policy enforce infrastructure rules
- Identity systems validate access controls
Each control sends signals back to the GRC platform.
Also Read: How Enterprises Can Ensure Compliance Using Blockchain
Reporting Layer
This layer gives leadership a clear and current view of risk. Dashboards show:
- Live risk scores
- Control status across ISO 27001, PCI DSS, GDPR
- Incident trends and audit readiness
This architecture connects systems, data, and controls into a single, real-time GRC model.
Core Components of a GRC Program & Framework
A governance risk and compliance framework only works when a few core parts stay connected. Each one has a clear role. Break that link, and the system starts to drift.
| Component | What it does | What it includes | Where it shows up |
|---|---|---|---|
| Governance | Sets rules and ownership | Policies, approval flows, control frameworks | Internal policy tools, board reports |
| Enterprise Risk Management | Tracks what can go wrong | Risk registers, scoring logic, and incident logs | GRC platforms, SIEM tools like Splunk |
| Compliance | Checks if rules are followed | Control testing, audits, and evidence records | ServiceNow GRC, audit systems |
| Technology | Connects everything | APIs, data pipelines, dashboards | Cloud logs, identity systems, Kafka streams |
Each part depends on the others. If risk data does not reach compliance, audits slow down. If governance rules do not connect to systems, controls stay on paper. A working setup keeps all four parts in sync.
Governance, risk, and compliance cannot operate in silos—connect systems, automate controls, and gain real-time visibility before gaps widen further.
Best Practices & Benefits of GRC Implementation
Strong governance, risk & compliance implementation programs do not rely on audits or manual tracking. They run as part of daily operations.
- Connect GRC with DevSecOps
Controls run inside CI/CD pipelines, which reflects the importance of GRC in software development — code changes, deployments, and configurations are checked before release. - Automate compliance workflows
Evidence is pulled from systems like ServiceNow, Jira, and cloud logs. Control testing runs on live data instead of manual reviews. - Centralize risk data
Risk signals from Splunk, Okta, and cloud platforms feed into one system. Teams do not maintain separate records. - Align leadership with governance
Risk dashboards are reviewed by CIOs and business heads. Ownership is defined at the system and process level. - Track risk continuously
Risk scores update as events occur. Teams do not wait for audits to detect issues.
Enterprises that follow these practices treat GRC as a working system. Others treat it as documentation and fall behind.
How to Update a GRC Framework With Appinventiv
Many enterprises already run a GRC setup, yet it fails to reflect real system activity. Risk data stays split across tools, controls rely on manual checks, and reports lag behind events.
Appinventiv, as a cybersecurity services company, rebuilds GRC as a connected system. We modernize existing frameworks by linking controls to live data from tools like Splunk, Okta, and cloud platforms.
We integrate legacy systems using APIs and data pipelines so logs, access events, and audit records flow into one structure. We automate evidence collection and control validation, which reduces audit delays and errors.
We also create dashboards that show current risk, control status, and compliance coverage. This turns GRC implementation into a system that tracks risk in real time instead of after the fact.
Schedule a consultation and identify hidden risk before it surfaces in your next audit.
FAQs
Q. What is GRC implementation?
A. GRC implementation sets up a system where policies, risks, and controls are tracked together. Most teams already have parts of this in place. Policies sit in one tool, risks in another, and audit evidence somewhere else. Implementation connects these pieces. Controls get linked to systems, not just documents. Risk data updates from real activity, not periodic reviews. This gives leadership a clear view without pulling reports from multiple teams.
Q. What is the cost of implementing GRC?
A. Costs depend on how deep the system goes. A small setup with limited integrations can start around $50,000. Enterprise programs often fall between $150,000 and $500,000. The main drivers are platform choice, number of integrations, and how much automation is built. Connecting systems like cloud logs, identity platforms, and security tools usually adds the most effort.
Q. How long does GRC implementation take?
A. A limited rollout can take three to six months. Larger programs take longer. When multiple systems, regions, and compliance frameworks are involved, timelines often reach six to twelve months. Integration and data cleanup take most of the time. Setting up workflows and ownership also adds effort.
Q. How do organizations maintain and improve a GRC program after implementation?
A. Teams keep the system active by linking controls to live data. Access logs, system events, and tickets feed into the platform. Risk scores update as changes happen. Evidence is collected automatically instead of being prepared at the last moment. Regular reviews keep control mappings aligned with new regulations.
Q. How does Appinventiv approach enterprise GRC implementation?
A. Appinventiv builds GRC around the systems already in use. The process starts with defining risk and control structures. Then, tools like Splunk, Okta, and cloud platforms are connected, so data flows into one place. Control checks run on system data, not manual input. Dashboards show current risk without waiting for reports. This creates a setup where governance and operations stay connected.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

Vibe Coding Security Risks: Why Your AI-Generated App is a Ticking Time Bomb
Key takeaways: Vibe coding removes security checks, not just effort Working code doesn’t mean secure code AI speeds up vulnerabilities, not just development Human oversight is essential for safe systems Scaling AI apps requires expert-led security rebuilds [blog_faq] We need to talk about the elephant in the IDE. Everyone is obsessing over "vibe coding." You…
Key Takeaways Vulnerability assessment finds weaknesses. Penetration testing proves exploitability. You need both to understand real exposure. Annual testing isn’t enough. Enterprise environments change too fast for checklist-driven security. Severity scores don’t equal business risk. Prioritization must factor in exploitability, exposure, and impact. Security value comes from remediation, not reports. If findings aren’t fixed and…

Cybersecurity Risk Management - Strategy, Framework, Implementation Plan
Key takeaways: Digital transformation is rapidly increasing attack surfaces, rendering annual risk assessments obsolete in as little as 90 days. Effective cybersecurity risk management has to be treated just as any other business risk: with executive-level accountability and ongoing monitoring. Breaches involving third-party vendors exceed 60%, underscoring the need for end-to-end supply chain risk management.…





































