- What “Good” Looks Like in DevOps for Financial Services
- How to Implement DevOps in Banking (Execution Roadmap)
- 1. Tier and Map Banking Systems by Risk, Dependency, and Change Sensitivity
- 2. Design a Regulated CI/CD Architecture, Not Just Pipelines
- 3. Embed DevSecOps Controls with an Evidence-First Model
- 4. Establish Platform Engineering and Golden Paths for Scale
- 5. Introduce Progressive Modernization for Legacy Integration
- 6. Scale by Product Domains and Govern Through Delivery Metrics
- What Differentiates Enterprise Banking DevOps from Basic Implementations
- Key Principles of DevOps in Banking
- Design for auditability, not just automation
- Shift compliance left and enforce it automatically
- Standardize delivery through approved patterns
- Enforce identity-driven access and least privilege
- Engineer reliability into the release lifecycle
- Compliance Pipeline Deep Dive: Turning CI/CD into a Control System
- Core Control Mechanisms Embedded in the Pipeline
- Evidence Artifacts Generated Automatically
- Architecting the DevOps Delivery Platform for Regulated Banking
- 1. Minimum Viable Regulated Delivery Stack (Pilot Stage)
- 2. Enterprise-Scale DevOps Platform Model
- 3. Tool Selection Criteria for Financial Institutions
- Why This Matters
- Business Impact of DevOps in Banking
- Challenges in DevOps Adoption in Banking and How We Navigate Them
- 1. Legacy Core Constraints Without Release Flexibility
- 2. Regulatory Scrutiny and Continuous Oversight
- 3. Organizational Silos Between Engineering, Risk, and Operations
- 4. Toolchain Fragmentation and Inconsistent Controls
- 5. Balancing Innovation Speed with System Stability
- Real-World Applications of DevOps in Banking
- Capital One: Scaling Cloud-Native Delivery with Controlled Releases
- ANZ Bank: Extending DevOps Practices to Mainframe Environments
- Industry Pattern: Compliance-Embedded Delivery Pipelines
- Industry Pattern: Progressive Deployment for High-Risk Systems
- Appinventiv Case Insight: Scalable Financial Platform Delivery
- Common Use Cases Enabled by DevOps in Banking
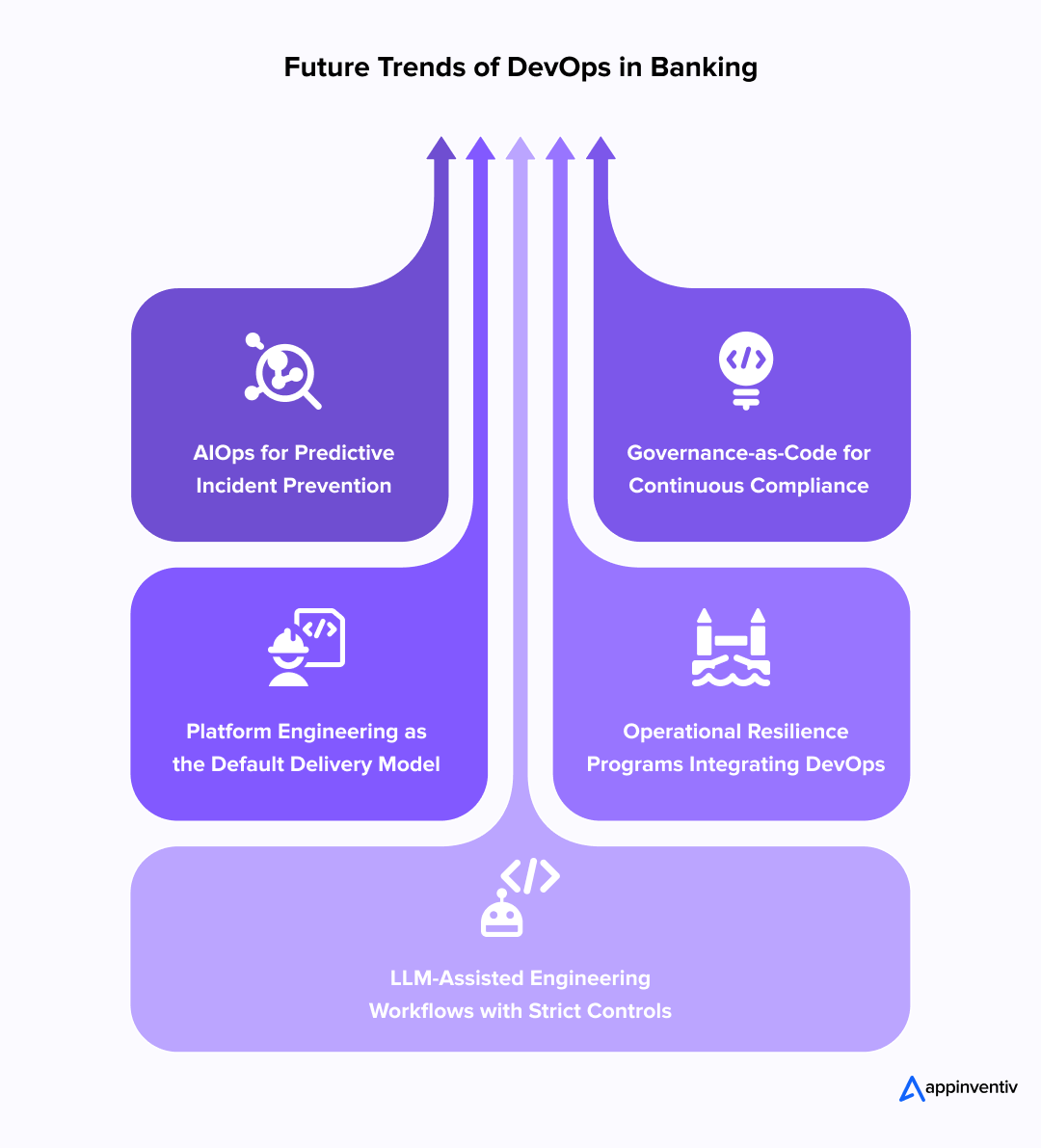
- Future Trends in DevOps for Banking
- AIOps for Predictive Incident Prevention
- Governance-as-Code for Continuous Compliance
- Platform Engineering as the Default Delivery Model
- Operational Resilience Programs Integrating DevOps
- LLM-Assisted Engineering Workflows with Strict Controls
- What These Trends Signal
- How can Appinventiv Help Banks Implement DevOps Successfully?
- Frequently Asked Questions
Key takeaways:
- DevOps in Banking is not about speed alone. It enables controlled, auditable change across critical customer journeys.
- In regulated environments, CI/CD becomes a governed control system that produces security, risk, and audit evidence automatically.
- The fastest gains come from a golden path approach with standardized pipelines, policy gates, and observability at scale.
- Legacy cores modernize safely through incremental patterns, not high-risk full replacements.
- Mature programs measure success beyond deployment speed, tracking risk reduction, compliance evidence, and customer-impact reliability.
Banking no longer competes on products alone. It competes on how quickly, safely, and consistently it can deliver change. Digital onboarding flows, payment integrations, fraud rules, and regulatory updates now move through software pipelines, not paper approvals. In this environment, DevOps in banking becomes a strategic capability, not a technical preference.
Industry research shows that elite DevOps performers using automated governance and peer reviews achieve 2.6x higher performance than low performers relying on manual approvals, such as Change Advisory Boards (CABs), enabling banks to balance speed with compliance and reduce delivery risks.
Platform engineering and DevSecOps practices amplify these gains by embedding security early, reducing remediation costs, and automating compliance checks to enable faster innovation without stability trade-offs. When implemented correctly, DevOps in banking software development enables controlled innovation, regulatory alignment, and scalable digital growth without compromising stability.
At the same time, banks are investing heavily in intelligent automation and AI-driven decision systems. As these capabilities expand, delivery pipelines must support faster model updates, stronger security controls, and continuous compliance oversight.
Integrate DevOps and AI to modernize operations, strengthen security, and scale with confidence.
What “Good” Looks Like in DevOps for Financial Services
Before diving into implementation, it helps to define the target state. A mature DevOps for financial services environment is built around controlled delivery, auditability, and resilience.
| Capability | What It Enables | Business Impact |
|---|---|---|
| Policy-enforced releases | Automated approval gates and compliance checks | Reduces change risk and regulatory exposure |
| Full traceability | Immutable logs and versioned infrastructure changes | Speeds audits and improves accountability |
| Automated compliance evidence | Continuous capture of security and control artifacts | Lowers audit effort and improves governance readiness |
| Progressive deployment | Canary, blue-green, and rollback strategies | Minimizes service disruption during releases |
| Reliability engineering | SLOs, monitoring, and incident response workflows | Improves uptime and customer trust |
This is not about deploying faster. It is about delivering change with confidence, control, and resilience.
How to Implement DevOps in Banking (Execution Roadmap)
Implementing DevOps in banking is not a tooling exercise. It is the design of a controlled delivery system that aligns engineering velocity with regulatory oversight, operational resilience, and risk management.
The execution roadmap below reflects how enterprise banks operationalize DevOps in banking software development without compromising stability.
1. Tier and Map Banking Systems by Risk, Dependency, and Change Sensitivity
Enterprise DevOps begins with application tiering, not pipelines.
Banks operate systems with vastly different risk tolerances. Treating a payment switch and a mobile UI update with identical release controls creates either excessive friction or unacceptable risk.
Typical tiering model
- Tier 0 / Mission-critical: core ledger, payments rails, identity, fraud controls
- Tier 1 / Customer-facing: digital banking, onboarding, cards, API gateways
- Tier 2 / Operational systems: CRM integrations, reporting, workflows
- Tier 3 / Analytics & support: BI, data marts, internal tools
What changes in practice
- Release gates and approvals vary by tier
- Monitoring depth and rollback strategies differ
- Change windows and blast-radius controls are tier-specific
- Evidence and audit requirements scale with system criticality
This risk-based approach prevents over-control of low-risk systems while ensuring stringent governance where failure is unacceptable.
Also Read: A CIO’s Guide to IT Risk Management
2. Design a Regulated CI/CD Architecture, Not Just Pipelines
A banking-grade CI/CD system functions as a governed delivery backbone, not merely an automation pipeline. Core architectural components include:
Controlled source management
Branch protection, peer review enforcement, and traceable approvals.
Build integrity & artifact provenance
Signed artifacts, tamper-proof repositories, and version traceability ensure that deployed code matches approved builds.
Security & compliance gates
SAST, SCA, secrets detection, and policy-as-code checks prevent non-compliant changes from progressing.
Progressive deployment controls
Canary releases, blue-green deployments, and automated rollback reduce blast radius.
Environment parity & Infrastructure as Code
IaC ensures production parity and eliminates configuration drift.
Observability & incident integration
Telemetry, logs, and alerts integrate with incident response workflows.
Evidence capture & audit trail
Immutable logs and control artifacts support regulatory reviews and internal audits.
This architecture becomes the operational foundation of DevOps methodology in the banking industry.
3. Embed DevSecOps Controls with an Evidence-First Model
In regulated environments, DevSecOps in financial institutions must produce verifiable evidence of controls, not just pass security scans.
Control domains implemented in pipeline workflows
- Vulnerability and dependency scanning with remediation tracking
- Secrets management and key rotation policies
- Role-based access controls and just-in-time privilege elevation
- Policy enforcement for configuration and compliance rules
- Immutable logging of approvals, changes, and deployments
Why this matters
- Security teams gain continuous visibility.
- Compliance teams receive structured evidence.
- Engineering teams avoid manual review bottlenecks.
This approach ensures security and compliance in banking DevOps without slowing delivery cycles.
Moving from Manual Gatekeepers to Policy-as-Code
In traditional banking setups, the Risk and Compliance departments act as manual gatekeepers, often leading to 2-week review cycles that stall production. Modern DevSecOps replaces this bottleneck with Policy-as-Code (PaC).
By “coding” regulatory requirements (such as PCI-DSS encryption standards or SOC2 access controls) directly into the pipeline, the Risk department shifts from being a blocker to a co-author of the delivery process. If a change violates a policy, the pipeline fails instantly, providing immediate feedback. This transition transforms compliance from a reactive “snapshot” audit into a continuous, real-time assurance model.
Also Read: Developing Regulatory Compliance Software for the Financial Industry
4. Establish Platform Engineering and Golden Paths for Scale
As delivery expands across teams, fragmentation becomes the primary risk. Platform engineering introduces consistency without central bottlenecks.
Golden path components
- Pre-approved CI/CD templates
- Standardized infrastructure modules
- Integrated monitoring and alerting
- Built-in policy enforcement
- Secure secrets handling
Enterprise advantage
Developers provision compliant infrastructure and pipelines quickly while maintaining standardized controls.
This approach reduces tool sprawl and accelerates the integration of Devops in banking across business units.
5. Introduce Progressive Modernization for Legacy Integration
Most banks cannot replace core systems quickly. DevOps adoption must coexist with legacy platforms.
Enterprise modernization approach
- Expose legacy functionality via secure APIs
- Incrementally replace components instead of full rewrites
- Monitor data contracts and interface stability
- Maintain strict change controls around core systems
This incremental model enables digital transformation in banking through DevOps while minimizing systemic risk.
6. Scale by Product Domains and Govern Through Delivery Metrics
Enterprise scaling is achieved through domain adoption rather than organization-wide mandates.
Scaling pattern
- Pilot within a single product domain
- Validate reliability, compliance, and operational workflows
- Expand golden path adoption across adjacent teams
- Standardize governance reporting and KPIs
Key metrics for enterprise DevOps maturity
- Deployment frequency by system tier
- Change failure rate
- Mean time to recovery (MTTR)
- Incident impact minutes on critical journeys
- Compliance evidence completeness
- Policy exception trends
| Benchmarking Banking Success via DORA Metrics | ||
|---|---|---|
| Metric | Purpose in Banking | The “Elite” Target |
| Deployment Frequency | Measures agility in responding to market/regulatory shifts. | On-demand (multiple times per day) |
| Lead Time for Changes | Measures the efficiency of the “Idea-to-Value” cycle. | Less than one day |
| Change Failure Rate | The primary indicator of release quality and testing rigor. | 0% – 15% |
| MTTR | Measures operational resilience and “Self-Healing” capabilities. | Less than one hour |
This metrics-driven approach transforms DevOps practices in banking into measurable business performance improvements.
What Differentiates Enterprise Banking DevOps from Basic Implementations
Enterprise banking environments operate under regulatory scrutiny, operational risk constraints, and complex legacy dependencies. As a result, DevOps in the banking industry must extend beyond automation to deliver controlled, auditable, and resilient change.
| Basic DevOps | Enterprise Banking DevOps |
|---|---|
| Focus on automation | Focus on controlled, auditable delivery |
| Security scans | Compliance evidence & policy enforcement |
| Single pipeline | Tiered governance & risk-based controls |
| Tool adoption | Platform engineering & standardization |
| Faster releases | Reliable, compliant, risk-aware delivery |
| Monitoring | Reliability engineering & SLO-driven operations |
Implementing DevOps in banking is not about moving faster for its own sake. It is about designing a delivery system that allows banks to innovate confidently while maintaining control, compliance, and resilience.
Key Principles of DevOps in Banking
DevOps principles must reinforce operational control, auditability, and resilience. The following principles guide safe, scalable adoption without slowing delivery.
Design for auditability, not just automation
Every release should generate traceable evidence, from code approvals to deployment records. When traceability is built into workflows, audits shift from manual reconstruction to real-time verification.
Shift compliance left and enforce it automatically
Security, regulatory controls, and policy checks must run inside the pipeline rather than after release. DevOps automation enforcement ensures that non-compliant changes never progress, reducing review bottlenecks and compliance risk.
Standardize delivery through approved patterns
Reusable pipeline templates, infrastructure modules, and deployment patterns reduce variability across teams. Standardization strengthens governance while allowing teams to move faster with fewer errors.
Enforce identity-driven access and least privilege
Pipeline access, deployment permissions, and infrastructure changes must be governed by strict identity controls. Limiting privileged access reduces insider risk and strengthens operational integrity.
Engineer reliability into the release lifecycle
Reliability is not an afterthought. Progressive deployment, automated rollback, and service-level objectives ensure that new releases improve systems without increasing operational instability.
These principles ensure DevOps practices in banking strengthen governance and resilience while enabling controlled innovation.
Compliance Pipeline Deep Dive: Turning CI/CD into a Control System
In banking environments, the CI/CD pipeline is more than a delivery mechanism. It functions as a regulatory gatekeeper that enforces controls, preserves evidence, and ensures every change meets security and regulatory compliance requirements before reaching production.
A compliance-first pipeline reduces manual oversight, strengthens governance, and creates continuous assurance instead of periodic compliance checks.
Core Control Mechanisms Embedded in the Pipeline
Artifact signing and provenance tracking
Every build artifact is signed and traceable, ensuring that only approved and verified code reaches production environments.
Binary authorization and release integrity
Deployment policies allow only scanned, validated, and signed artifacts to be released, preventing unauthorized or unverified code from execution.
Policy-as-code enforcement
Security, configuration, and regulatory policies are encoded into the pipeline, ensuring consistent enforcement of compliance requirements across environments.
Secrets management and controlled access
Sensitive credentials are stored in secure vaults with strict access policies, eliminating hard-coded secrets and reducing exposure risk.
Immutable audit trails
All pipeline actions, approvals, deployments, and configuration changes are logged in tamper-resistant systems to support regulatory review and forensic analysis.
Segregation of duties and approval workflows
Role-based approvals aligned with system criticality ensure that no single actor can introduce and deploy high-risk changes.
Evidence Artifacts Generated Automatically
A compliance-aware pipeline continuously produces structured evidence required for audits and internal governance.
- Security and vulnerability scan reports with remediation tracking
- Approval logs and access records tied to change workflows
- Infrastructure change history and configuration diffs
- Deployment manifests and release traceability records
- Incident logs, recovery timelines, and post-incident reviews
Why this matters for enterprise banking
- Compliance shifts from periodic audits to continuous assurance
- Regulatory reviews become faster and evidence-driven
- Security teams gain real-time visibility into risk exposure
- Engineering teams avoid manual compliance bottlenecks
- Governance strengthens without slowing delivery velocity
By transforming CI/CD into a compliance control system, banks can scale DevSecOps in financial institutions while maintaining regulatory alignment, operational resilience, and delivery confidence.
Also Read: The Role of DevOps in Compliance Management
Architecting the DevOps Delivery Platform for Regulated Banking
In enterprise banking, tool selection is secondary. The primary concern is architectural coherence, control integration, and long-term scalability. A fragmented toolchain increases operational risk and audit complexity. A structured delivery platform reduces both.
Rather than assembling disconnected tools, banks should design a unified DevOps platform aligned with governance requirements.
1. Minimum Viable Regulated Delivery Stack (Pilot Stage)
At the pilot level, the focus is on control validation and architectural integrity.
Core components include:
- Secure source control with enforced code reviews
- CI automation with integrated testing
- Artifact repository with signing capability
- Integrated security scanning
- Infrastructure as Code for repeatable environments
- Centralized logging and monitoring
The objective is not velocity yet. It is validating that controls, approvals, and evidence workflows function correctly.
2. Enterprise-Scale DevOps Platform Model
Once validated, scaling requires platform consolidation.
Enterprise-grade delivery platforms typically include:
- GitOps or controlled CD workflows
- Policy-as-code governance enforcement
- Internal developer portal (IDP) for self-service provisioning
- Centralized compliance evidence repository
- Observability stack integrated with SRE processes
- Hybrid and multi-cloud orchestration support
This shift from “tools per team” to “platform per organization” is what differentiates DevOps in the banking industry from generic implementations.
3. Tool Selection Criteria for Financial Institutions
When evaluating tooling for DevOps in banking software development, decision-makers should assess:
- Integration with enterprise IAM and least-privilege enforcement
- Ability to produce and export audit artifacts
- Support for policy enforcement and segregation of duties
- Environment parity and drift detection
- Scalability across multiple business domains
- Hybrid and on-prem compatibility
These criteria prevent long-term tool sprawl and reduce governance friction.
Also Read: How Enterprises Modernize DevOps Software Development Journey
Why This Matters
DevOps practices in banking fail most often due to:
- Uncontrolled tool adoption
- Inconsistent pipeline standards
- Weak integration with governance frameworks
- Fragmented evidence generation
A platform-first architecture ensures that security and compliance in banking DevOps scale consistently across teams.
Appinventiv helps modernize your core banking operations through secure, scalable digital platforms.
Business Impact of DevOps in Banking
When implemented with governance and reliability controls, DevOps in Banking delivers measurable outcomes beyond engineering efficiency. The impact extends to operational resilience, regulatory readiness, and customer trust.
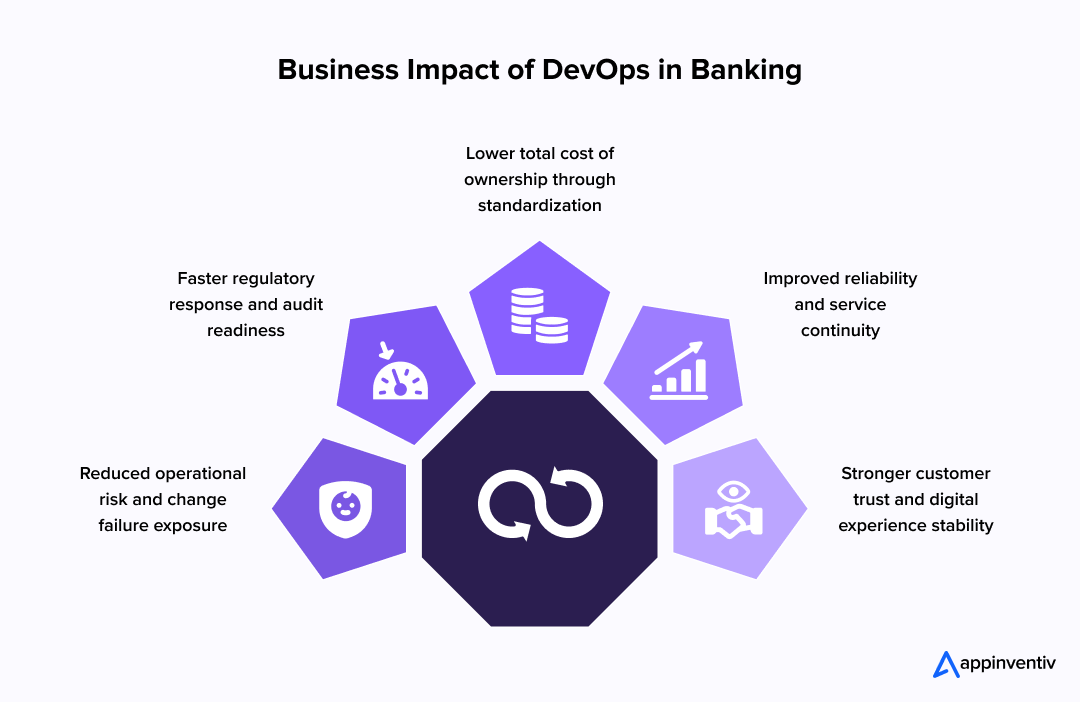
Reduced operational risk and change failure exposure
Controlled releases, policy enforcement, and progressive deployment reduce the likelihood of service disruption in critical systems such as payments and digital channels. Fewer failed changes translate into lower incident costs and reduced regulatory risk.
Faster regulatory response and audit readiness
Audit-ready pipelines produce structured evidence for security and compliance teams. Regulatory updates, policy changes, and remediation actions can be implemented and verified more quickly, improving governance responsiveness.
Lower total cost of ownership through standardization
Standardized delivery patterns reduce rework, configuration drift, and environment inconsistencies. Over time, this lowers operational overhead and minimizes costly remediation cycles.
Improved reliability and service continuity
Reliability engineering practices, automated rollback mechanisms, and enhanced observability improve system uptime and recovery times. This strengthens customer confidence in digital banking services.
Stronger customer trust and digital experience stability
Stable releases and predictable performance ensure uninterrupted access to banking services. Consistent reliability directly supports customer retention and brand trust.
These outcomes demonstrate how DevOps practices in banking contribute to measurable business resilience and long-term DevOps ROI for financial institutions.
Challenges in DevOps Adoption in Banking and How We Navigate Them
Adopting DevOps in Banking is rarely blocked by technology alone. The real friction appears at the intersection of regulation, legacy systems, operational risk, and organizational structure. What differentiates successful projects is not awareness of these challenges, but how they are engineered around.
Below are the most critical barriers banks face and how we approach them in enterprise engagements.
1. Legacy Core Constraints Without Release Flexibility
Most large banks operate mission-critical core systems that cannot tolerate frequent or uncontrolled change. Attempting to “modernize everything” typically increases risk and regulatory scrutiny.
Our approach
- Map system criticality before any pipeline rollout
- Introduce API façades to isolate change from core transaction engines
- Implement tier-based release controls aligned to system sensitivity
- Apply progressive deployment only where operational risk allows
Rather than forcing DevOps practices onto legacy cores, we architect coexistence models that allow innovation at the edges while preserving stability at the center.
Also Read: AI in Legacy Application Modernization – A Complete Guide
2. Regulatory Scrutiny and Continuous Oversight
Banks operate under constant audit cycles and regulatory monitoring. A typical DevOps setup focused only on speed creates evidence gaps that surface during compliance reviews.
Our approach
- Design compliance-as-code controls directly into pipelines
- Create structured evidence artifacts aligned to regulatory frameworks
- Standardize segregation-of-duties workflows across system tiers
- Establish governance dashboards that risk and compliance teams can access in real time
This turns security and compliance in banking DevOps into a continuous assurance model instead of a reactive audit exercise.
3. Organizational Silos Between Engineering, Risk, and Operations
In many banks, delivery, infrastructure, and risk teams operate independently. This fragmentation slows the integration of DevOps in banking at scale.
Our approach
- Define cross-functional ownership models at the product-domain level
- Implement shared metrics across engineering and risk functions
- Align release governance with measurable KPIs such as change failure rate and compliance exception trends
- Establish platform standards that remove tool-level fragmentation
This reduces decision latency and creates a shared accountability framework.
4. Toolchain Fragmentation and Inconsistent Controls
Enterprise banking environments often accumulate disconnected tools across business units. This leads to uneven enforcement of DevOps practices in banking and inconsistent audit evidence.
Our approach
- Consolidate pipelines into standardized golden paths
- Integrate IAM and policy enforcement centrally
- Ensure evidence export and traceability across environments
- Transition from tool selection to platform governance
The goal is to eliminate delivery variance while preserving domain autonomy.
5. Balancing Innovation Speed with System Stability
The most delicate challenge in DevOps in the banking industry is managing change velocity without increasing operational exposure.
Our approach
- Apply SLO-based release gating
- Use canary and blue-green deployment strategies where risk permits
- Monitor incident impact minutes across customer-critical journeys
- Establish rollback playbooks aligned with system tiers
This ensures that acceleration does not come at the expense of resilience.
Banks rarely struggle because they lack DevOps awareness. They struggle because regulated delivery requires architectural discipline, governance alignment, and domain-level scaling strategies.
By addressing these challenges, DevOps in banking software development becomes sustainable rather than experimental.
Real-World Applications of DevOps in Banking
DevOps in banking is most credible when viewed through publicly documented engineering initiatives, conference disclosures, and observable industry patterns. Across global financial institutions, DevOps has evolved from a delivery acceleration tactic into a capability for resilience, compliance, and reliability.
Below are representative examples and patterns that illustrate how DevOps is applied in the banking industry within regulated environments.
Capital One: Scaling Cloud-Native Delivery with Controlled Releases
Capital One’s engineering organization has publicly shared its transition toward cloud-native architecture, automated pipelines, and cross-functional delivery teams. By standardizing build and deployment workflows and integrating security controls into delivery pipelines, the bank improved release consistency and operational resilience.
What this demonstrates
- Automation improves release predictability
- Integrated security controls reduce risk exposure
- Cloud-native delivery enables scalable, controlled change
This approach reflects how DevOps in banking software development supports innovation without weakening governance.
ANZ Bank: Extending DevOps Practices to Mainframe Environments
ANZ has documented efforts to modernize delivery practices while maintaining stability across legacy mainframe systems. Instead of replacing core platforms, the bank focused on automating manual processes, improving source control practices, and strengthening collaboration across delivery teams.
What this demonstrates
- DevOps can coexist with legacy core systems
- Automation reduces manual release risk
- Delivery predictability improves even in hybrid environments
This example reflects a common reality: DevOps in banking must integrate with existing infrastructure rather than replace it.
Industry Pattern: Compliance-Embedded Delivery Pipelines
Tier-1 banks across Europe, North America, and Asia increasingly embed compliance and security controls directly into CI/CD workflows. Policy enforcement, automated security scanning, and immutable audit trails enable continuous assurance rather than periodic compliance reviews.
Operational impact
- Faster audit response cycles
- Improved traceability of changes
- Reduced compliance friction during releases
This shift illustrates how security and compliance in banking DevOps are moving from review-driven to pipeline-driven.
Industry Pattern: Progressive Deployment for High-Risk Systems
Banks operating critical payment and transaction systems use progressive deployment strategies such as canary releases and blue-green deployments to minimize disruption risk.
Operational impact
- Reduced customer impact during releases
- Safer updates to high-availability systems
- Faster rollback in case of anomalies
These practices strengthen resilience while enabling continuous improvement.
Appinventiv Case Insight: Scalable Financial Platform Delivery
While most published DevOps case studies focus on large global banks, Appinventiv’s work on enterprise financial solutions reinforces how secure, scalable systems form the backbone of regulated operations. In one engagement with a major European bank, Appinventiv delivered an AI-enabled banking platform that improved customer retention by automating complex processes and exposing scalable backend services.
Although this case centers on architectural scale and automation rather than explicit DevOps tooling, the underlying delivery model reflects DevOps principles: automation, repeatable environments, alignment with compliance, and observability; all of which support sustainable, regulated delivery practices.
Common Use Cases Enabled by DevOps in Banking
Across institutions, several recurring use cases of DevOps in banking demonstrate the practical value:
Digital onboarding and KYC workflows
Controlled releases ensure regulatory compliance while enabling frequent improvements to customer experience.
Payments and transaction processing systems
Progressive deployment and observability reduce outage risk and improve recovery times.
Open banking APIs and partner integrations
Automated testing and monitoring improve reliability and traceability across third-party integrations.
Fraud detection and risk systems
Safe deployment pipelines enable model updates without destabilizing critical risk controls.
| What These Examples Reveal | ||
|---|---|---|
| Delivery Need | DevOps Capability | Outcome |
| Release consistency | Automated pipelines & governance gates | Reduced change risk |
| Legacy coexistence | Hybrid delivery workflows | Stability with modernization |
| Compliance readiness | Evidence-driven pipelines | Faster audit response |
| System resilience | Progressive deployment & observability | Improved uptime & recovery |
| Scalable digital services | Standardized environments & automation | Sustainable growth |
These examples show that DevOps for financial services is not theoretical. It is a practical delivery model that strengthens reliability, compliance, and scalability while enabling controlled innovation.
Future Trends in DevOps for Banking
DevOps in banking is evolving beyond delivery automation. The next phase is defined by resilience engineering, continuous compliance, and intelligent operations.
These trends reflect how financial institutions are strengthening control while enabling faster, safer innovation.
AIOps for Predictive Incident Prevention
Banks are increasingly applying machine learning to operational telemetry to detect anomalies before they escalate into service disruptions. Instead of reacting to outages, AIOps platforms correlate logs, metrics, and traces to identify early warning signals.
What this enables
- Earlier detection of performance degradation
- Reduced overnight incident escalations
- Faster root cause identification
Predictive operations improve reliability while reducing operational strain on engineering teams.
Governance-as-Code for Continuous Compliance
Compliance is shifting from periodic review cycles to continuous enforcement embedded in delivery workflows. Governance-as-code extends policy enforcement beyond security scanning to include configuration standards, access policies, and regulatory controls.
Operational impact
- Consistent enforcement of compliance requirements
- Reduced audit preparation time
- Continuous assurance instead of reactive remediation
This evolution strengthens security and compliance in banking Devops without slowing delivery velocity.
Platform Engineering as the Default Delivery Model
As delivery scales across multiple product domains, platform engineering is emerging as the preferred model for standardizing controls and accelerating development.
Internal developer platforms provide:
- Approved deployment templates
- Secure infrastructure provisioning
- Built-in monitoring and policy enforcement
- Self-service capabilities with guardrails
This approach reduces tool fragmentation and enables integrating Devops in banking at scale.
Operational Resilience Programs Integrating DevOps
Regulatory focus on operational resilience is increasing globally. DevOps practices are increasingly integrated with resilience programs to ensure service continuity, visibility into dependencies, and tested recovery procedures.
What this means for banks
- Improved recovery readiness
- Better visibility into system dependencies
- Stronger incident response and recovery workflows
DevOps pipelines increasingly serve as execution layers for resilience testing and recovery automation.
LLM-Assisted Engineering Workflows with Strict Controls
Financial institutions are beginning to explore AI-assisted development workflows to improve code quality, documentation, and pattern detection. Due to regulatory and security considerations, these implementations emphasize strict access controls, data protection safeguards, and auditability.
Potential benefits
- Faster code review support and documentation
- Improved detection of logic or configuration risks
- Increased developer productivity under controlled environments
Adoption remains cautious, with governance frameworks guiding usage.
What These Trends Signal
The future of DevOps in the banking industry is not defined solely by speed. It is shaped by resilience, continuous compliance, and intelligent automation. Banks are evolving delivery systems that reduce operational risk while enabling sustained digital innovation.
These future trends in DevOps for banking point toward a model where automation strengthens governance, platforms standardize control, and intelligent operations improve reliability at scale.
Get a pipeline and controls assessment that maps delivery workflows to evidence and governance requirements.
How can Appinventiv Help Banks Implement DevOps Successfully?
Banks don’t need more tools. They need a delivery system that balances speed, control, and regulatory accountability. Through our custom banking software development services, we help financial institutions design and scale DevOps models that align with operational risk, compliance requirements, and long-term growth.
Our DevOps consulting services begin with a structured assessment of your current delivery workflows, system tiers, and governance gaps. From there, we define a regulated CI/CD architecture, embed policy-driven controls, and standardize pipelines that reduce release friction without weakening oversight.
We focus on outcomes that matter to enterprise leaders:
- Reduced change risk across critical systems
- Faster, controlled feature rollouts
- Automated compliance evidence and audit readiness
- Lower operational overhead through standardized delivery
With 3000+ product launches and a team of 1600+ technology experts, we bring execution depth across complex banking ecosystems, from core integrations to digital channels.
If you’re evaluating how to modernize delivery while maintaining control, connect with our team to explore a structured DevOps roadmap tailored to your banking environment.
Frequently Asked Questions
Q. How much does DevOps implementation cost in banking?
A. The cost of implementing DevOps in banking could be $35,000-$400,000+, depending on scope, maturity, and regulatory requirements. A pilot focused on one product line is typically far more cost-efficient than an enterprise-wide rollout. The best approach is to start with a control and pipeline assessment, then fund a phased program tied to measurable outcomes.
Q. How does DevOps improve CI/CD pipelines for banking systems?
A. DevOps improves CI/CD by standardizing build and release workflows, automating tests, enforcing security gates, and enabling progressive delivery. In banking, the key upgrade is traceability and evidence. Every change becomes auditable, and release risk is reduced through controlled rollouts.
Q. What challenges do banks face during DevOps implementation, and how to solve them?
A. Common challenges include legacy constraints, strict compliance, organizational silos, and toolchain fragmentation. Banks solve them by tiering systems, adopting incremental modernization patterns, enforcing policy-as-code, standardizing golden paths, and scaling through platform engineering rather than one-off implementations.
Q. How can AI and ML be integrated with DevOps in banking?
A. AI is increasingly applied through AIOps for anomaly detection and incident correlation, and through MLOps to deploy and monitor models safely. In both cases, strong governance is essential: access control, data handling rules, monitoring for drift, and audit evidence for approvals and deployments.
Q. How can DevOps improve regulatory compliance in banking?
A. DevOps improves compliance by turning controls into automated pipeline gates and producing evidence automatically. Policy enforcement, signed artifacts, access logging, and immutable audit trails help banks respond faster to audits and reduce manual compliance effort, while keeping delivery predictable.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

How to Choose the Right DevOps Automation Tools for Your Business?
Key takeaways: Picking the right DevOps automation tools can turn release chaos into control. Smart automation enhances speed, reliability, and team efficiency. Tool selection should align with business goals, not market hype. Over-automation and poor alignment often lead to project failure. A well-planned DevOps setup drives measurable and sustainable business growth. Let’s be honest -…

Transforming Private ROSA Deployments with Automated Tekton CI/CD
In today’s cloud-native world, application teams seek automation, security, and scalability without trade-offs. Red Hat OpenShift Service on AWS (ROSA) delivers a managed Kubernetes experience with enterprise-grade features. But when clusters run in private subnets for security, it creates a common challenge: how do you enable CI/CD pipelines that rely on external triggers, like GitHub…
DevOps Maturity: Why It Matters and How Business Leaders Can Achieve It
Key takeaways: Business Impact: High DevOps maturity correlates with 1.5x higher revenue growth and significantly lower operating costs. The Reality Gap: While many adopt "tools," few achieve true maturity—struggling with silos and fragmented pipelines. The Roadmap: Maturity is a 5-stage journey from ad-hoc firefighting to AI-driven self-healing systems. Actionable Steps: Success requires measuring DORA metrics,…