- How Digital Immune Systems Protect Your Business Against Cyberattacks?
- Core Components of a Digital Immune System (DIS)
- Benefits of a Digital Immune System
- Important Factors Affecting the Adoption of Digital Immune Systems
- How to Build a Digital Immune System for Your Business
- Challenges and Solutions of Digital Immune Systems
- What’s Next for Digital Immune Systems: The Road Ahead
- Why Partner with Us for Your Digital Immune System Need
- FAQ’s
Key takeaways:
- Digital immune systems have become essential for organizations to combat rising cyber threats, with the global market expected to reach $57 billion by 2032.
- Digital immune system in cybersecurity integrates tools like firewalls, antivirus software, and intrusion detection systems, along with strong security policies and employee training to proactively prevent cyberattacks.
- AI and machine learning enhance the cyber immune system by predicting and detecting vulnerabilities early, enabling businesses to take proactive defense measures against potential cyber threats.
- Investing in DevSecOps and automation can streamline the integration of security into development cycles, making it a continuous, proactive process that strengthens the overall security posture of businesses.
When Netflix deliberately crashed their own systems through chaos engineering, they weren’t being reckless—they were being strategic. . The goal was to build an infrastructure that could detect vulnerabilities, adapt instantly, and self-heal before users even noticed a glitch. This real-world approach reflects a growing movement in enterprise resilience: the Digital Immune System.
In today’s world of cloud-native applications, distributed systems, and real-time processing, businesses face a brutal reality: cyberattacks and software failures. These digital breaches don’t just disrupt operations; they destroy customer trust and financial stability. Taking measures after the damage is done simply doesn’t work anymore.
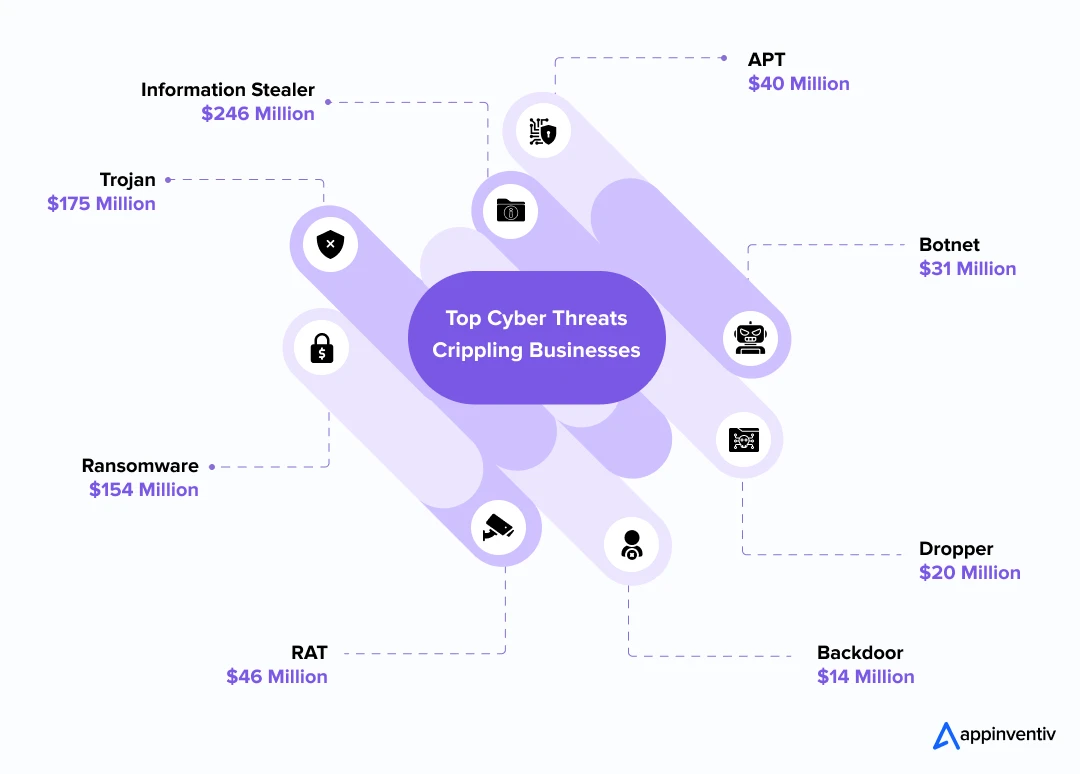
Cisco’s 2024 Cyber Threat Trends Report shows that Information Stealers, Trojans, and Ransomware dominate the threat landscape, with hundreds of millions of monthly blocks reported. These aren’t isolated incidents, they’re persistent, evolving threats that are crippling systems and draining resources across industries.
Traditional security and testing-focused quality approaches have proven too slow and too reactive for today’s threat environment. That’s where a Digital Immune System comes in—a proactive, AI-driven defense mechanism that mimics the human immune system to detect anomalies, neutralize threats, and ensure operational continuity.
Gartner predicts that by 2025, organizations investing in digital immunity will reduce downtime by 80%, leading to significant increases in customer satisfaction. The global DIS market is forecasted to reach $57 billion by 2032, providing clear evidence of its strategic importance.
In this blog, we’ll dive into how a digital immune system works, exploring its core components, benefits, key drivers, implementation strategies, and the challenges it addresses.
We’ll also see how forward-thinking companies are leveraging it to turn cybersecurity resilience into a powerful competitive edge.
Digital immunity can slash downtime by up to 80%
Still relying on outdated defenses? It’s time to level up your cybersecurity game
How Digital Immune Systems Protect Your Business Against Cyberattacks?
Digital Immune Systems comprises hardware and software components working together to protect digital systems against online threats. Here’s how it works:
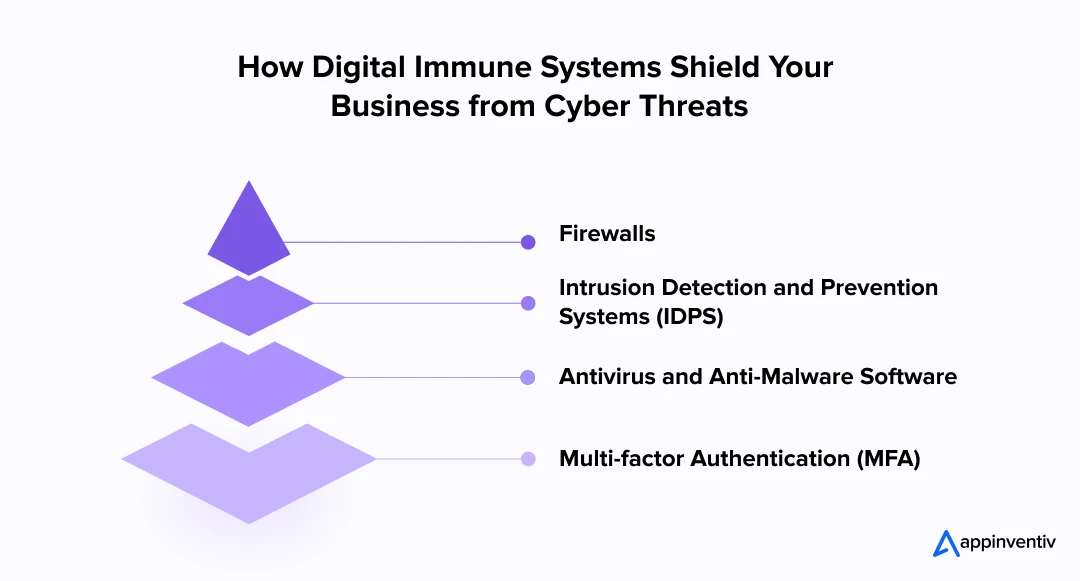
Firewalls
Firewalls act as the first line of defense, functioning like digital security guards. They diligently monitor incoming and outgoing data by following established rules. Their role is not only to prevent unauthorized access but also to block potentially harmful information. These rules encompass granting access to trusted sources while simultaneously restricting entry from malicious websites and allowing traffic based on verified user identities.
Intrusion Detection and Prevention Systems (IDPS)
IDPS acts as a vigilant watchman for your network. These computer programs closely monitor network activity to detect signs of a cyberattack. Using a set of rules and signatures, they define normal network behavior and identify attack patterns. For instance, IDPS can detect repeated failed login attempts or identify traffic from known malicious sources, effectively safeguarding your network against new threats and known attacks.
Antivirus and Anti-Malware Software
Antivirus and Anti-Malware software act as your digital guardians, protecting you from unwanted software such as viruses, worms, and spyware. They diligently scan files and emails to identify harmful content, swiftly removing or isolating it.
Multi-Factor Authentication (MFA)
Multi-factor Authentication (MFA) acts as an ultra-secure lock, safeguarding your digital doors. It entails users providing multiple forms of authentication for accessing a system or network. This may include something they are (e.g., a security token), something they have (like a password), or something they know (such as a fingerprint).
Core Components of a Digital Immune System (DIS)
A digital immune system in cybersecurity is a sophisticated, multifaceted approach that integrates various technologies and processes to protect an organization’s IT infrastructure. By leveraging advanced digital immune system strategies, businesses can ensure resilience and security from evolving cyber risks. Let’s break down the essential components that form the foundation of this dynamic system.
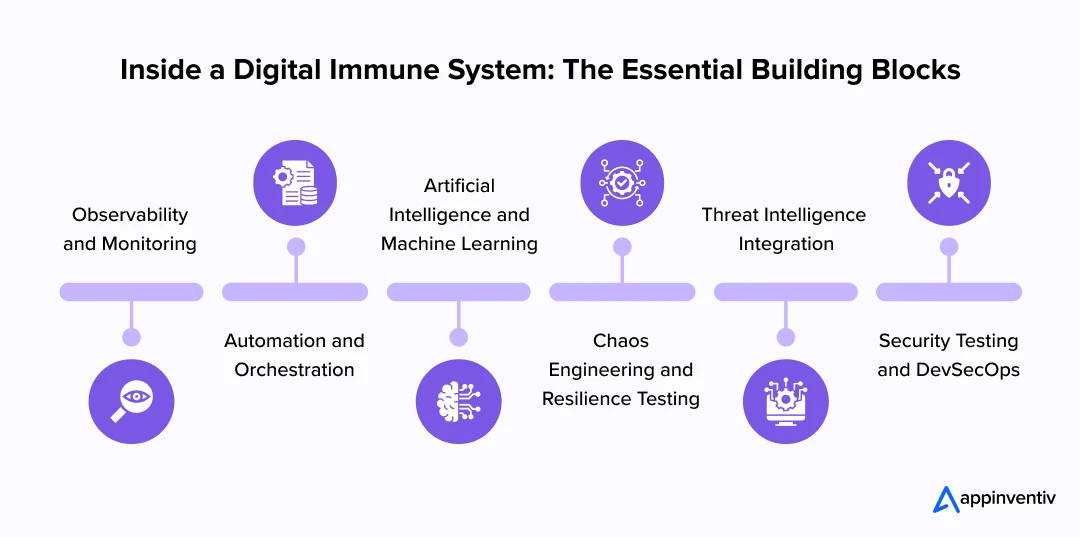
Observability and Monitoring
Real-time visibility into system behavior is crucial for identifying potential threats before they escalate. With observability, every aspect of the system—from user interactions to backend processes is continuously monitored. Anomalies such as unusual traffic patterns or resource consumption are detected swiftly, enabling a proactive response.
To enhance this, AIOps (Artificial Intelligence for IT Operations) and telemetry tools automate the data collection and analysis process. This enables smarter decision-making, ensuring the digital immune system in businesses remains agile and prepared to tackle emerging threats with precision.
Automation and Orchestration
Automation is a cornerstone of the digital immune system in business protection, particularly for threat detection and incident response. Automated threat detection mechanisms use machine learning and predefined protocols to quickly identify suspicious activities, allowing for rapid containment of risks. Once a threat is identified, automated response systems mitigate the issue, minimizing downtime and the potential for further damage.
Moreover, this automation is integrated into Continuous Integration/Continuous Deployment (CI/CD) pipelines, making it a seamless part of the development lifecycle. This ensures that secure applications are consistently deployed without manual intervention, significantly enhancing the role of digital immune system in improving system efficiency and security.
Artificial Intelligence and Machine Learning
Artificial Intelligence and machine learning are essential to strengthening the digital immune system in cybersecurity. Through behavior analysis algorithms, the system constantly monitors activities to establish baseline behaviors. When deviations occur, they are flagged for investigation, enabling early detection of potential attacks.
Predictive analytics, powered by AI and ML, provides insights into future risks based on historical data, improving the system’s proactive capabilities. Anomaly detection, fueled by machine learning, continuously adapts to new threats, ensuring the system can detect even the most novel attack methods, enhancing the cyber immune system’s resilience against evolving risks.
Chaos Engineering and Resilience Testing
To ensure robustness under pressure, chaos engineering and resilience testing play pivotal roles in a digital immune system within businesses. Chaos engineering involves intentionally introducing failures to test the system’s ability to recover from disruptions. This technique of digital immune system in threat prevention simulates real-world conditions, enabling the identification of vulnerabilities that attackers could exploit.
The system’s resilience is assessed to ensure it can withstand and recover from unexpected stressors. By introducing controlled disruptions, organizations can pinpoint weaknesses and improve their infrastructure’s overall ability to respond to real-world cyber threats.
Threat Intelligence Integration
Integrating real-time feeds from global threat databases is key to keeping the cyber immune system updated with the latest threat intelligence. These feeds provide crucial insights into emerging attack patterns, new vulnerabilities, and advanced persistent threats (APT). With real-time access to global threat data, the system can adjust its defenses dynamically.
This adaptive response mechanism ensures that the digital immune system in cybersecurity can effectively counter ever-changing risks, providing proactive protection before threats manifest. By constantly staying ahead of global threats, businesses can maintain a fortified security posture.
Security Testing and DevSecOps
The integration of security early in the software development lifecycle is fundamental to a successful digital immune system in businesses. DevSecOps emphasizes embedding cloud security into every phase of development and deployment, ensuring vulnerabilities are addressed before they reach production. Shift-left testing is used to catch security issues as early as possible, preventing the spread of potential threats.
Continuous validation of security protocols throughout the development pipeline ensures that security is a constant focus, not an afterthought. This holistic approach makes security a continuous process, essential for maintaining the integrity and resilience of digital ecosystems.
Benefits of a Digital Immune System
A digital immune system offers several advantages in protecting digital assets and ensuring operational resilience. The key benefits of a digital immune system are:
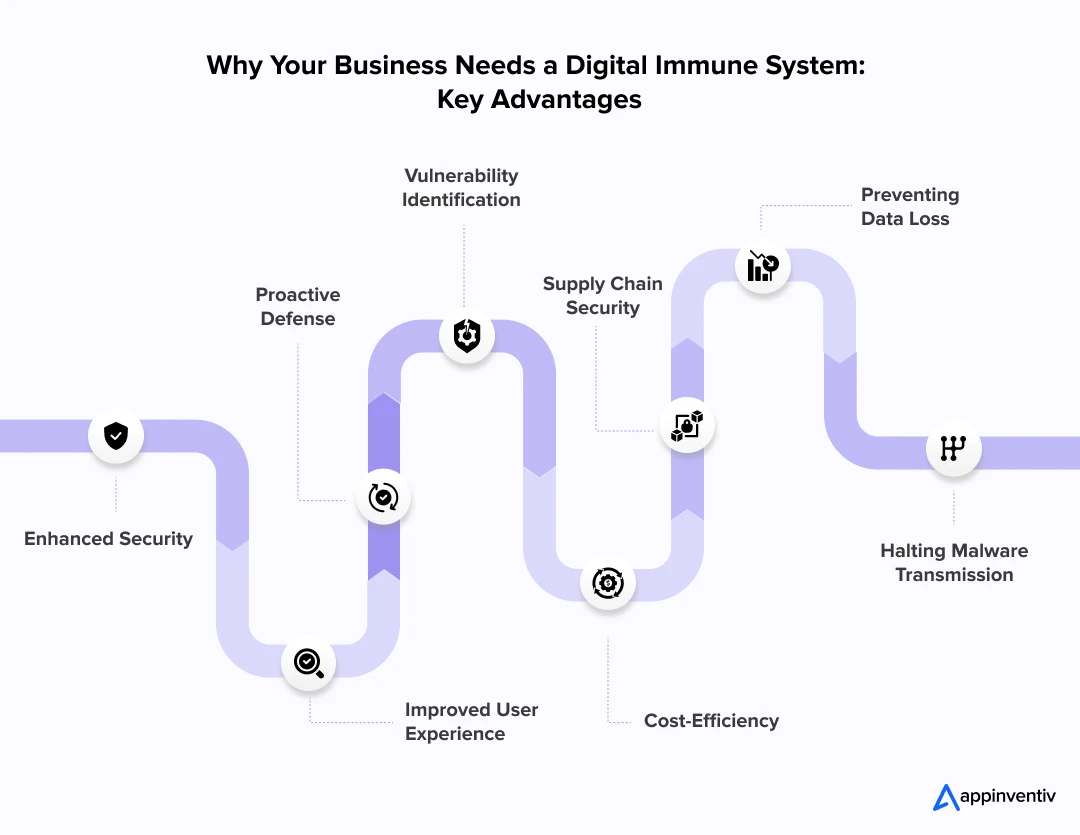
Enhanced Security
A digital immune system ensures robust protection against cyber threats through continuous monitoring and active defense against potential risks. It significantly reduces the chances of data breaches, unauthorized access, and other security incidents. By bringing together various security tools and protocols, it creates stronger defenses that protect digital assets and sensitive information from constantly evolving cyberattacks.
Proactive Defense
DIS enables continuous monitoring of digital environments, ensuring potential threats are detected the moment they appear. This proactive approach allows for swift responses, minimizing the impact of cyberattacks before they can escalate. By automating threat detection and response, the system ensures security measures are applied immediately, reducing damage and downtime.
Improved User Experience
With observability and auto-remediation features, DIS keeps digital systems running smoothly. This technology monitors system performance in real-time and automatically fixes issues before they affect end-users. By maintaining consistent uptime and preventing disruptions, it creates a seamless and satisfying user experience that’s essential for customer satisfaction and retention.
Vulnerability Identification
Chaos engineering plays a crucial role in identifying system vulnerabilities by intentionally introducing disruptions to test system resilience. This approach helps organizations uncover weaknesses that might otherwise stay hidden. By proactively addressing these vulnerabilities, businesses can strengthen their defenses and prevent attackers from exploiting them.
Supply Chain Security
Supply chain security is essential for protecting software and ensuring the integrity of both internal and external code. By implementing strong version control and managing vendor risks, organizations can protect their software supply chains from attacks. This ensures that any third-party software and components integrated into systems remain secure, reducing the risk of vulnerabilities from external sources.
Cost-Efficiency
A digital immune system provides significant cost savings by preventing expensive cyber incidents, such as data breaches and system downtimes. By automating threat detection, incident response, and remediation, DIS reduces the need for manual intervention and streamlines operations. Over time, this cuts both operational costs and the financial impact of security-related disruptions.
Preventing Data Loss
One of the main reasons for the significance of a digital immune system in cybersecurity is its role in preventing sensitive information from being lost. Whether it’s personal data, financial records, or confidential business documents, the consequences of unauthorized access to this data can be devastating. By detecting and blocking such attempts, a digital immune system in data protection offers a strong defence against data breaches.
Halting Malware Transmission
A digital immune system can halt the spread of malware and other malicious software. This becomes particularly critical during major cyberattacks, where just a single piece of malware can compromise the security of countless systems. The digital immune system in cyberthreats identifies and blocks such threats, significantly mitigating the impact of these attacks.
Important Factors Affecting the Adoption of Digital Immune Systems
Several key influencing factors are shaping the direction and urgency associated with DIS. These factors highlight the critical role that DIS plays in safeguarding organizations.
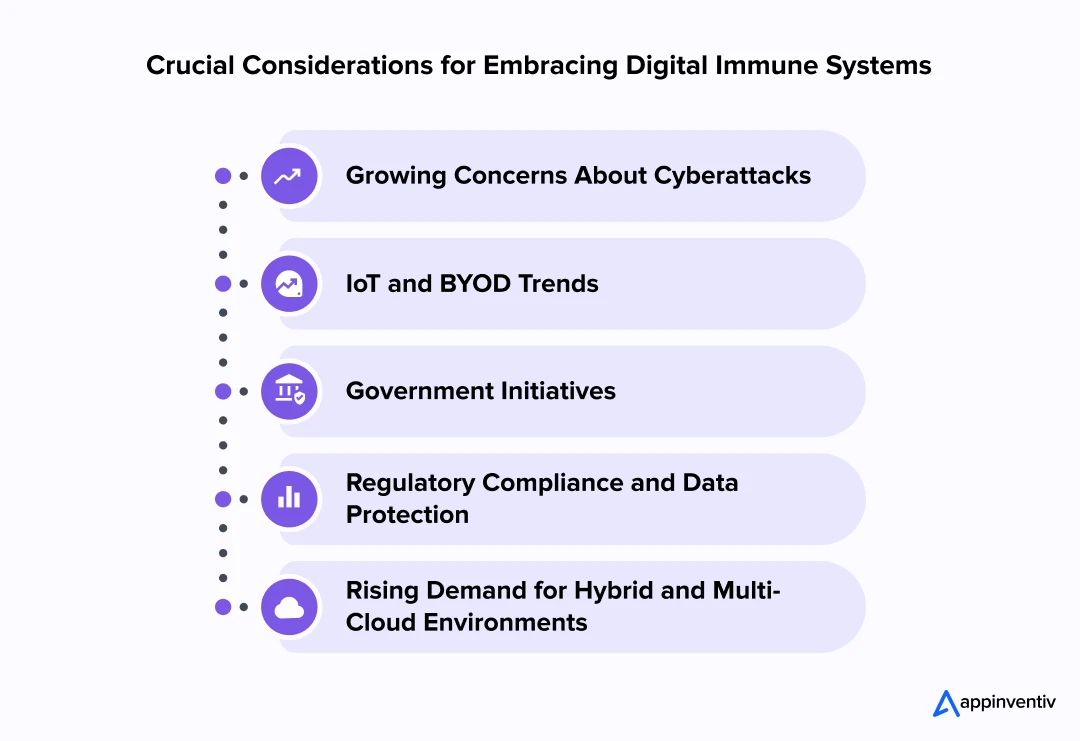
Growing Concerns About Cyberattacks
The adoption of digital immune system solutions and services has gained momentum due to the increasing threat of internal cyberattacks and breaches in cloud computing solutions. Consequently, leading organizations demand more secure IT infrastructure to response to such incidents. Contrary to earlier predictions that cybersecurity technology alone would fuel market growth, virtualized security solutions have enhanced their capability to monitor access by privileged users.
Moreover, the growing adoption of hybrid and multi-cloud technologies allows sensitive data storage in private clouds. However, this increased occurrence also brings about internal cyberattacks, paving the way for growth opportunities in the Digital Immune System market.
Also Read: Top 10 Cybersecurity Measures for Businesses in 2025
IoT and BYOD Trends
The Internet of Things (IoT) and the “bring your device” (BYOD) trend have drastically changed how smart applications are used in various sectors. This includes government, healthcare, retail, and IT & telecoms. The adoption of next-generation network-powered solutions and advancements in core technology is fueling the growth of the device immune system market. With IT consulting services, businesses can effortlessly integrate and optimize these innovative solutions, assuring strong cybersecurity measures.
However, employee-owned BYOD increases the risk of internal cyber theft. Therefore, robust virtualization security solutions for internal IT infrastructure are essential. Furthermore, as more devices connect, it leads to the collection of significant data blocks that enable the development of IoT-based data center applications. In addition to this, the BFSI sector’s growing reliance on machine learning-based applications is expected to drive market expansion further.
Government Initiatives
Many governments implemented comprehensive national cybersecurity strategies to boost their defenses against cyberthreats. These strategies involve collaboration among various stakeholders, including government agencies and private sector entities, to strengthen cybersecurity measures, promote information sharing, and establish effective incident response capabilities.
Regulatory Compliance and Data Protection
Companies today face mounting pressure from strict data protection regulations like GDPR and CCPA. These laws aren’t just suggestions—they carry serious financial consequences for non-compliance. Organizations have discovered that digital immune systems provide an effective path to meeting these regulatory demands.
When consumer data protection becomes a legal requirement rather than an option, businesses must ensure their digital infrastructure can withstand breaches and prevent unauthorized access. This regulatory environment has become a major catalyst driving companies toward DIS adoption, helping them stay compliant while avoiding costly penalties.
Rising Demand for Hybrid and Multi-Cloud Environments
The business world has embraced hybrid and multi-cloud strategies as the new standard for data management and storage. Cloud computing delivers the flexibility and growth potential organizations need, but it also opens new doors for internal security threats.
As more companies migrate sensitive information to private cloud platforms, protecting these distributed environments has become essential. DIS solutions step in to fill this security gap, providing comprehensive protection tools that keep both internal operations and external data exchanges secure across complex cloud architectures.
How to Build a Digital Immune System for Your Business
Creating a robust digital immune system for your business requires a comprehensive defense strategy that can adapt and respond to evolving cyber threats. Here’s a practical framework to help you develop this essential protection:

Assess Current Cybersecurity Maturity
Before you can improve your defenses, you need to understand your current security posture. Conduct thorough vulnerability assessments and penetration tests to identify weak spots in your existing infrastructure.
Consider this a comprehensive audit of your digital assets. Understanding your baseline security maturity helps you prioritize where to focus your resources and efforts most effectively. Document all findings systematically; this assessment becomes your roadmap for improvement and helps you measure progress over time.
Get Full Visibility Across Your Systems
Comprehensive observability is fundamental to effective cybersecurity. Implement real-time monitoring across your entire network to detect unusual activity as it occurs. Advanced telemetry provides the insights needed to identify potential threats before they escalate.
This type of digital immune system in network security serves as your early warning system, enabling proactive threat detection and response. Ensure your monitoring encompasses servers, networks, user behavior, and application performance to create a complete security picture.
Let Automation Handle the Heavy Lifting
Manual security processes cannot keep pace with today’s threat landscape. Integrate automation into your security workflows and CI/CD pipelines to handle routine tasks and enable rapid response capabilities.
This approach doesn’t replace human expertise; it enhances it by ensuring consistent, fast responses to emerging threats while freeing your team for strategic decision-making. Begin by automating your most repetitive security tasks, then gradually expand to more complex operations as your team develops proficiency with the tools.
Harness AI and Machine Learning for Smarter Defense
Advanced AI and ML technologies can analyze patterns in your data that traditional methods might overlook. These systems establish baseline behavior for your environment and identify deviations that could indicate security threats.
By predicting potential vulnerabilities before exploitation occurs, you shift from reactive to proactive defense strategies. Ensure these systems receive high-quality, well-organized data to maximize their effectiveness and accuracy in threat detection.
Test Your Resilience Regularly
Chaos engineering provides valuable insights into your system’s resilience under stress conditions. Regularly simulate system failures and attack scenarios to identify weaknesses in your infrastructure before real threats exploit them.
These controlled disruptions reveal gaps in your defense mechanisms that you can address proactively. Schedule these exercises during low-impact periods with proper rollback procedures to ensure learning opportunities don’t become operational disruptions.
Make Security Everyone’s Job from Day One
Integrate security practices throughout your entire development lifecycle using DevSecOps methodologies. Rather than treating security as an afterthought, embed it into every stage of your software development process.
This approach prevents vulnerabilities from reaching production environments and significantly reduces remediation costs. Establish clear security checkpoints and requirements that development teams can follow without impeding their productivity or workflow efficiency.
Build a Security-Minded Team
Your technical defenses are only as effective as the people who operate them. Implement regular training programs on threat recognition, proper security protocols, and maintaining security awareness across all organizational levels.
Since human error often serves as the entry point for security breaches, investing in your team’s security knowledge provides substantial returns. Design training programs that are role-specific and practical—targeted, relevant instruction is more effective than generic security awareness sessions.
Invest in the Right Technology Stack
Select security tools that align with your specific business requirements rather than pursuing the latest technology trends. Focus on solutions that integrate seamlessly with your existing infrastructure and provide actionable threat intelligence.
The most effective security platform is one that your team can operate efficiently and effectively. Plan for future growth from the outset by choosing scalable solutions that can expand and adapt as your business and security needs evolve.
Start with a clear vision and the right best practices to fortify your systems against evolving cyber threats
Challenges and Solutions of Digital Immune Systems
As organizations increasingly rely on digital technologies, the adoption of Digital Immune Systems has become crucial in combating cyberthreats. However, implementing these systems comes with its own set of challenges. Below, we outline some of these challenges along with their corresponding solutions to ensure successful DIS integration.
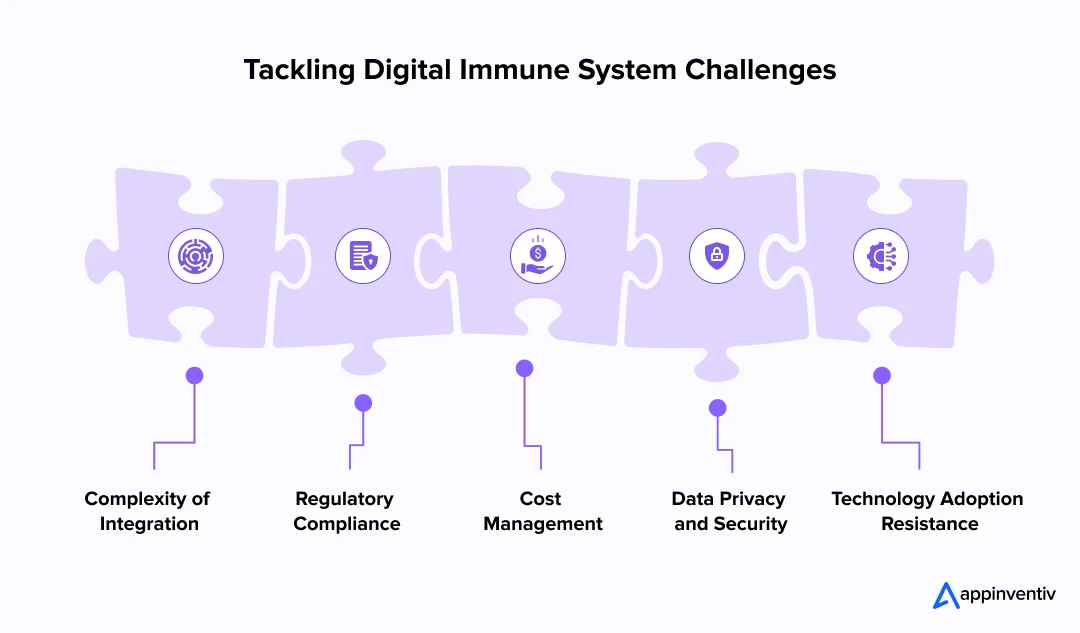
Challenge 1: Complexity of Integration
Integrating DIS into existing IT infrastructures can be intricate, requiring a comprehensive overhaul of current systems and processes.
Solution: Leveraging expert IT integration services can simplify this process. These services help blend new DIS technologies with established systems seamlessly, reducing downtime and enhancing efficiency.
Challenge 2: Regulatory Compliance
Ensuring compliance with international, national, and industry-specific regulations can be daunting, especially as these regulations are continually evolving.
Solution: Implementing a dynamic compliance management system within the DIS that automatically updates and adapts to new regulations can ensure ongoing compliance and mitigate legal risks.
Challenge 3: Cost Management
The initial setup and maintenance of a robust DIS can be costly, particularly for small to medium-sized enterprises.
Solution: Adopting a scalable approach to DIS deployment can help manage cyber security costs effectively. Cloud-based DIS solutions can also reduce upfront expenses and offer flexibility in scaling operations as needed.
Challenge 4: Data Privacy and Security
As DIS often deals with sensitive data, ensuring the privacy and security of this data is paramount to prevent breaches and maintain trust.
Solution: Utilizing advanced encryption technologies and secure data protocols within the DIS can protect against unauthorized access and data breaches. Regular security audits and updates can further enhance data security.
Challenge 5: Technology Adoption Resistance
Employees may resist new technologies due to unfamiliarity or fear of change, which can hinder the effective adoption of DIS.
Solution: Comprehensive training programs and change management strategies can ease this transition. Engaging employees in the implementation process and demonstrating the benefits of DIS can also help in reducing resistance.
What’s Next for Digital Immune Systems: The Road Ahead
As cyber threats become increasingly sophisticated, the digital immune system must evolve beyond traditional defenses to provide proactive, adaptive protection. The future of DIS lies in integrating cutting-edge technologies like generative AI, predictive cybersecurity, and zero-trust architectures to keep businesses resilient against an ever-changing threat landscape.
Evolution of Cyber Threats: Today’s advanced threats, including AI-driven malware, require adaptive immunity that continuously learns and evolves. These systems need to recognize new attack patterns and counter them automatically, staying one step ahead of cybercriminals who are constantly refining their tactics.
Role of Generative AI in Advanced Defense: Generative AI represents a game-changer for cybersecurity, enabling autonomous detection and real-time creation of defense strategies. This technology provides faster, more proactive responses to previously unknown threats, essentially allowing your security system to think and adapt like a human analyst but at machine speed.
DIS in Zero-Trust Architectures: Zero-trust models have become integral to modern DIS implementations, where every single access request gets verified regardless of its source. This approach minimizes vulnerabilities by securing all organizational levels and never assuming trust based on location or previous authentication.
Predictive Cybersecurity and Autonomous Response Systems: The future belongs to systems that can predict threats before they materialize and neutralize them autonomously. This capability dramatically reduces the need for human intervention while enhancing response speed, creating real-time defense mechanisms that operate around the clock.
Looking ahead, digital immune systems will become indispensable business infrastructure components, functioning as the primary guardians of critical applications and data. They’ll need to adapt continuously to an evolving threat landscape that shows no signs of slowing down.
Why Partner with Us for Your Digital Immune System Need
The digital immune system in cybersecurity plays a crucial role in defending us against cyber threats. It stands out for its rapid growth, adaptability, and proactive approach towards detecting and preventing cyberattacks. Furthermore, its effectiveness translates into enhanced security measures, improved user experience, and substantial cost savings.
At Appinventiv, we understand the critical importance of a robust Digital Immune System (DIS) in safeguarding businesses against the evolving landscape of cyber threats. As a leading cybersecurity services company, our expertise in DIS not only stands out for its rapid growth and adaptability but also for our proactive approach to cybersecurity. Here’s why we are the right partner for enhancing your digital defenses:
- Expertise and Experience: Our cybersecurity experts are leaders in developing advanced, sector-specific digital immune systems.
- Customized Security Solutions: We deliver tailored DIS solutions that precisely meet your unique business security requirements.
- Proactive Threat Detection: We prioritize early threat detection to minimize risks and prevent breaches effectively.
- Cost Efficiency: Our DIS solutions reduce costs related to cyber incidents while boosting system reliability and performance.
- Comprehensive Support and Training: We provide extensive training and ongoing support to ensure your DIS operates at peak efficiency, enhancing your overall security posture.
Connect with our experts at Appinventiv for reliable custom software development services designed to strengthen your digital security with a robust digital immune system.
FAQ’s
Q. Why is a digital immune system important for my business?
A. Digital Immune Systems are crucial for businesses because cyberthreats have become increasingly prevalent and sophisticated. By implementing this system, you establish a robust defense mechanism to protect your digital assets from cyberattacks, data breaches, and security vulnerabilities. This proactive measure enhances system security, safeguards sensitive data, and ensures uninterrupted operations.
Q. How do enterprises implement a digital immune system?
A. Here are the basic steps of implementing a digital immune system in business:
- Integrate Advanced Technologies: Implement AI, machine learning, AIOps, and automation into cybersecurity systems.
- Real-Time Monitoring: Enable observability to track system behavior and detect anomalies early.
- Automate Threat Detection: Use CI/CD pipeline integration for automated threat detection and response.
- Behavior Analysis: Leverage AI to predict potential vulnerabilities by analyzing system behavior.
- Chaos Engineering: Simulate failures to test the system’s resilience under stress.
- Threat Intelligence: Integrate real-time threat intelligence feeds to stay updated on emerging risks.
- Embed DevSecOps: Implement security throughout the development lifecycle to address vulnerabilities early.
Q. How does a digital immune system protect businesses?
A. A digital immune system protects businesses with a proactive, multi-layered defense. It continuously monitors for threats, detecting anomalies in real-time and triggering automated responses to minimize breach impact. AI-powered predictive analytics help identify vulnerabilities before exploitation, while chaos engineering tests system resilience. By integrating real-time threat intelligence, the DIS adapts to emerging attacks, ensuring businesses stay ahead of cybercriminals and maintain system integrity.
Q. What are the key components of a digital immune system?
A. There are several key components of the Digital Immune System. These include perimeter security, which helps protect the network from outside threats. Endpoint security is essential for safeguarding individual devices connected to the system. Identity and access management ensure that only authorized individuals can access sensitive information.
Q. How can digital immune systems enhance customer experience?
A. Digital Immune Systems are crucial in enhancing the customer experience (CX) by ensuring the seamless operation of digital systems and services. It provides uninterrupted access to resources, instilling confidence in customers who rely on your business for their needs. This reliability fosters positive interactions, leading to higher customer satisfaction and loyalty.


- In just 2 mins you will get a response
- Your idea is 100% protected by our Non Disclosure Agreement.

From Legacy Security to Zero Trust Architecture: Upgrading Enterprise Security in Australia
Key takeaways: Australian cybercrime now costs large businesses $202,700 per incident on average, making Zero Trust architecture a board-level financial imperative Zero Trust is a phased programme, not a product. Identity controls, microsegmentation, and ZTNA must be sequenced deliberately to avoid operational disruption. Full ZTA implementation in Australia ranges from AUD 70,000 to 700,000+, but…

Claude Mythos: The Hidden AI Security Risks in Enterprise Digital Transformation
Key takeaways: AI is expanding the attack surface inside workflows, not just infrastructure, making traditional security visibility incomplete. Claude Mythos highlights a shift where risk comes from model behavior, prompts, and integrations, not just system vulnerabilities. Most enterprise AI risks do not start as breaches, they begin as small gaps in prompts, access control, or…

Key takeaways: The average cybersecurity breach cost in Australia has reached AUD 2.55 million in 2025, and that figure understates the true exposure for regulated industries when regulatory penalties, class litigation, and long-tail customer attrition are included. Data breach penalties in Australia have fundamentally changed. The maximum penalty for serious or repeated breaches is now…